Over the past 18 months, the Securities and Exchange Commission (SEC) has levied an onslaught of fines against public companies for inadequate disclosures of cybersecurity issues. In the latter half of 2021, British company Pearson agreed to pay $1 million, while First American Financial agreed to a settlement of $500,000.
Then, just last week, the SEC announced the biggest fine yet. The donor data management company, Blackbaud, agreed to pay $3 million for misleading disclosures relating to a 2020 ransomware attack that impacted almost 15,000 customers.
The latest fine, combined with the SEC’s proposed amendments to the cybersecurity rule, strongly indicate that the body is taking cybersecurity disclosures more seriously than ever. Public organizations can’t afford to be complacent.
The question is: are your policies and procedures up to scratch?
What happened with Blackbaud?
Before we dive into the what and why of the SEC’s cybersecurity requirements, let’s first quickly cover off the Blackbaud case in a little more detail.
On March 9th, the SEC released a public statement explaining it had reached a settlement with Blackbaud for a ransomware attack years earlier, stating:
“On July 16, 2020, Blackbaud announced that the ransomware attacker did not access donor bank account information or social security numbers. Within days of these statements, however, the company’s technology and customer relations personnel learned that the attacker had in fact accessed and exfiltrated this sensitive information.”
“These employees did not communicate this information to senior management responsible for its public disclosure because the company failed to maintain disclosure controls and procedures. Due to this failure, in August 2020, the company filed a quarterly report with the SEC that omitted this material information about the scope of the attack and misleadingly characterized the risk of an attacker obtaining such sensitive donor information as hypothetical.”
In essence, Blackbaud failed to tell the SEC about the full extent of the ransomware attack, and the data impacted, even though its employees knew more. Worse still, they publicly underplayed the attack’s blast radius.
In line with this, the SEC found that Blackbaud violated Sections 17(a)(2) and 17(a)(3) of the Securities Act of 1933 and Section 13(a) of the Securities Exchange Act of 1934 and Rules 12b-20, 13a-13, and 13a-15(a), leading to a huge $3 million penalty.
Why Is the SEC involved in data breach reporting?
When a lot of people think of the SEC, their minds immediately jump to the stock market. This is accurate. The SEC’s three goals are: “protecting investors, maintaining fair, orderly, and efficient markets, and facilitating capital formation.”
Most of us know about the SEC’s responsibilities in relation to market manipulation – for example, ensuring that consumers don’t invest in stocks based on falsified information.
However, the SEC’s role goes much deeper than that. The body is also the champion of transparency. In line with this, it requires public companies to share all sorts of risks that could impact a company’s earnings and stock price, including things like supply chain risks, environmental, social and governance risks and, of course, cybersecurity.
After all, when a company undergoes a cyber-attack or data breach, the ramifications can be huge: loss of customer trust, IT downtime and the public disclosure of confidential information can all affect revenue and, consequently, stock price.
Quite quickly, you can see why the SEC needs to know about a company’s cybersecurity risk management strategy, and any incidents they have suffered, in order to protect the interests of investors and the public.
What should companies include in a data breach disclosure to the SEC?
Under federal law, all companies must report and disclose security breaches or incidents to the SEC in line with transparency requirements. These requirements have been around for decades, but they’re about to get more complex.
As we speak, the SEC is pushing forward a new set of proposed cybersecurity disclosure rules for public companies, which bring further clarity and rigidity to reporting requirements.
The key obligations include:
- Report “material cybersecurity incidents” to the SEC within 4 days of the incident
- Report non-material incidents that, in conjunction with other incidents, become material “in the aggregate”
- Share updates on previous incidents in regular SEC disclosures
- Share an overview of the company’s cybersecurity risk management framework
- Explain the Board’s leadership in relation to cybersecurity risk
- Share the cybersecurity expertise of Board members.
These rules aren’t a big departure from what the SEC already has in place. Rather, the augmented obligations hold companies to a higher standard. Under the new rules, for example, there will be a bigger focus on the roles of senior leadership in overseeing cybersecurity programs.
Similarly, organizations will be put under more pressure to demonstrate they are adequately protecting their data and infrastructure from attack.
Generally, though, the rules further clarify what the SEC already expects, solidifying earlier guidance on breach disclosures so no company can claim it didn’t understand their responsibilities.
The SEC is taking security seriously. Are you?
While the SEC’s proposed rules aren’t yet formalized in law, the recent Blackbaud fine highlights that the SEC is becoming more stringent and less forgiving about data breach disclosure misconduct.
Already, you should have some processes in place for reporting cybersecurity incidents to the SEC and, where relevant, bodies like the Office for Civil Rights (OCR), PCI SSC and more.
As enforcement gets tougher, you should look to standardize and improve your disclosure procedures – if you haven’t already. Here’s how to do it.
Create a disclosure committee at the leadership level
Recent research shows that 90% of companies in the Russell 3000 lack even a single director with the necessary cyber expertise to meet the SEC’s increasing requirements. It’s paramount for organizations to create a dedicated disclosure committee.
This committee will play an important role in helping the CEO and CFO prepare for disclosures in line with the SEC’s rules, while also acting as a check and balance to ensure that disclosure controls and procedures are correctly followed.
Disclose cybersecurity risks, incidents and their blast radius quickly
You should review your cybersecurity policies and procedures to ensure you meet the SEC’s disclosure expectations. Namely, you’ll need to consider the communications channels between infosecurity personnel, legal and leadership to ensure that all information is shared effectively and quickly between the right people.
It will also be helpful to revisit your company’s definition of a cybersecurity incident and data breach. Generally speaking, a data breach is anything that compromises the confidentiality, integrity, or availability of sensitive information, be it an insider threat or a ransomware attack.
Unauthorized access to cloud systems, widespread network outages and DDoS attacks, even if no information is compromised, would also be considered cybersecurity incidents.
Given that the SEC expects to know about an incident in four days or less, you and your team will need to accept that you may need to disclose an incident before you understand the full extent of it.
Reduce the severity of data breaches
Ideally, of course, an organization would never have to disclose a breach because there would not be one in the first place. Our last piece of guidance, then, is to shore up your defenses to prevent the risk of a data breach or cyber-attack.
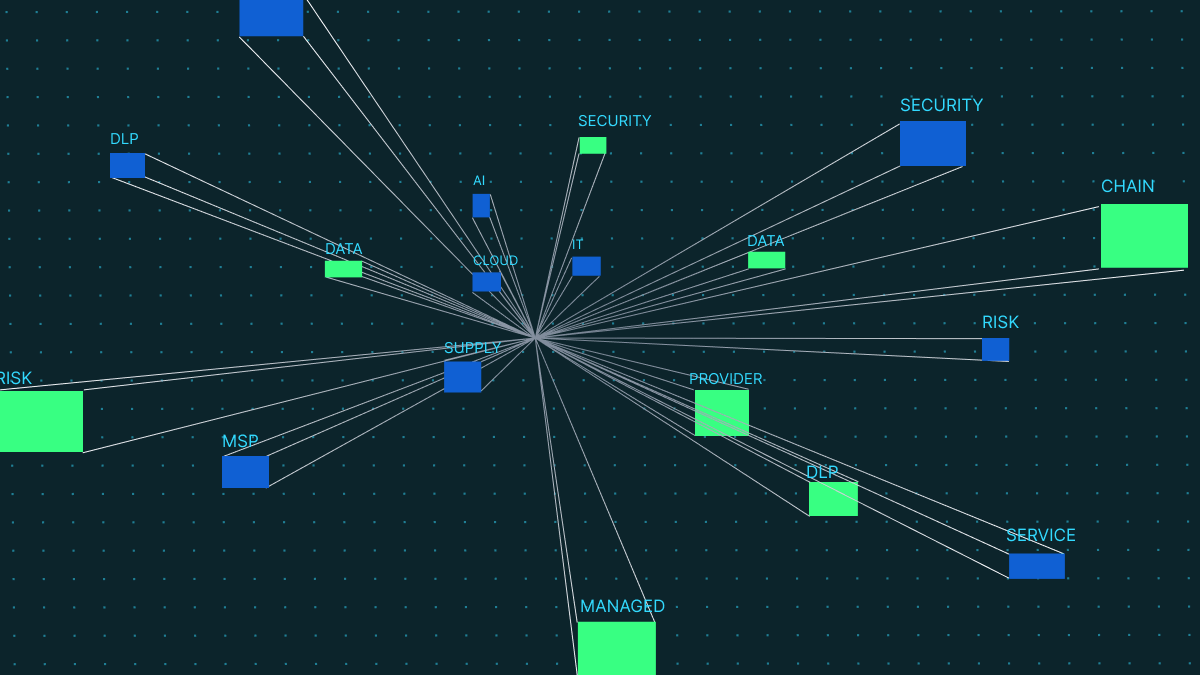
The way to do it? Working with a trusted cloud security provider like Polymer data loss prevention (DLP). Our solution dramatically reduces the risks of data leakage and exfiltration from the cloud apps your teams use every day, so you’re less likely to suffer a data breach.
How Polymer DLP can help
Be it insider trading taking place in chat, a hacker attempting to download sensitive information from Box or a complex-multi stage attack, our smart engine uses artificial intelligence and natural language processing to carefully monitor your cloud applications for signs of a potential cybersecurity incident.
When it sees suspicious activity, our engine autonomously kicks into action, analyzing a range of contextual factors to decide whether the user should be prohibited from engaging with data.
Depending on the severity of the incident, our engine will either alert the security team so they can take a further look or educate the user on why their action was unsafe, and redact the sensitive data in question.
For your SEC reporting requirements, Polymer DLP helps three-fold:
- Minimizes the possibility of data exfiltration or leakage in the cloud, thus reducing the overall likelihood of needing to disclose a severe data breach.
- Simplifies auditing and reporting requirements by automatically generating incident reports on thwarted attacks.
- Educates users on compliant cybersecurity practices through bite size training modules in cloud apps like Slack, Teams and more.
Curious about the data security risks in your cloud apps? Try our free risk scan.