A few decades ago, employees had to physically be in the office to collaborate, access workplace resources and get their work done. Now, thanks to cloud applications like Slack and Google Workspace, your users can log-on to workplace applications anywhere, anytime from any device.
While this flexibility is undoubtedly a major benefit for workplace productivity, it also comes with risks; namely in the form of cloud account hijacking. Cloud account hijacking occurs when a malicious actor manages to gain control of one of your employee’s cloud-based accounts. Once in the account, they can access a wealth of sensitive data or even impersonate your employee to commit fraud.
The most stealthy cybercriminals will also work to further compromise the accounts they’ve hijacked, perhaps launching a ransomware attack or installing backdoors so they can access these accounts at any time they choose.
Cloud account hijacking; a notable case study
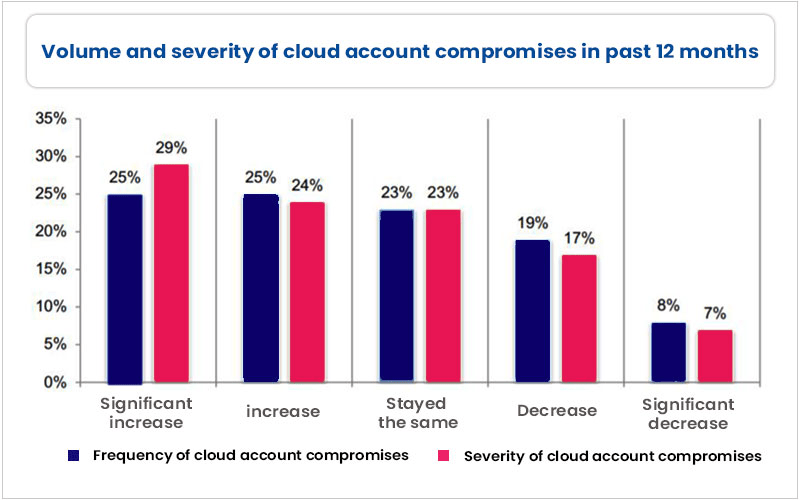
Cloud account hijacking is a serious problem for companies across sectors. According to research, 86% of IT leaders said this form of cybercrime cost them more than $500,000 in the last year.
Account hijacking isn’t rare either. The same report found that the average organization experiences roughly 64 cloud account compromises annually, with a third of these resulting in the loss of sensitive data. As you can see below, it appears this figure is rising year on year.
Possibly the most infamous example of cloud account hijacking is the Capital One data breach. In this incident, a former Amazon software engineer used a server-side request forgery (SSRF) attack to steal the credentials of an employee with access to sensitive data in an Amazon S3 bucket.
The data included financial information relating to 100 million credit card applications. Following the successful attack, Capital One was fined $80 million and settled customer lawsuits for $190 million.
How does cloud hijacking happen?
It’s clear that cloud hijacking is a real risk for businesses – with grave consequences if a hacker manages to steal sensitive data.
There are many ways for a cloud hijacking attack to happen, including:
- Phishing attacks
- Brute force password attacks, in which a cybercriminal uses trial and error to guess an employee’s password
- Using stolen password and login data up for grabs on the Dark Web
- Server-side request forgery (SSRF) attacks
- Manipulation of insecure web and mobile applications
- Credential-stealing malware
Underlying all of these tactics is a common thread: the fact that hackers don’t need to be physically on-premises to access your employees’ cloud accounts. Unless you have the right security tools at your disposal, it will be impossible for you to tell whether the person logging in to your employee’s account is legitimate or malicious.
Step-by-step: Cloud hijacking in action
Before we dive into how to prevent cloud hijacking, let’s first take a look at what a cloud hijacking attack looks like contextually. Below, we’re presuming that the threat actor has already got a hold of your employee’s credentials through one of the means above.
Step 1: The attacker uses your employee’s stolen credentials to log-in to their cloud account (something like Slack, Microsoft Outlook or Google Workspace)
Step 2: The attacker goes through your employee’s files, contacts and information for data that could be lucrative on the Dark Web and/or to build a picture of the employee so that they can then convincingly impersonate them.
Step 3: Depending on the attacker’s goal, this step tends to go in one of a few ways. They may simply take what data they’ve found and monetize it. Alternatively, they may pose as your employee in order to reroute invoices and receive monetary payment. Some cybercriminals will also spread malware via email or file upload in order to compromise the organization further.
Step 4: The cybercriminal ends the attack after they have received financial payment.
How to prevent cloud hijacking
Because cloud hijacking can have many root causes, you need to take a multi-levelled approach to ensure adequate protection. Here are our top tips to consider:
- Enable MFA: Multi-factor Authentication (MFA) is an authentication tool that mandates your users to verify themselves using two or more methods in order to access corporate resources like cloud applications. MFA is a simple way to protect common cloud hijacking tactics like brute force attacks. You should use MFA in conjunction with strong password policies – such as enforcing employees to change their passwords every six weeks. As a side note, if MFA is difficult to implement across your cloud applications, set a company policy that encourages employees to call the cellphone of the person who has asked for a wire transfer to ensure it’s legitimate.
- Implement the principles of least privilege and zero trust: Zero Trust sanctions that all networks, devices and users must first be treated as untrusted. Users will need to authenticate their identity before being able to access corporate files and resources. A big part of zero trust is the principle of least privilege, whereby employees are given just enough corporate access to get their job done – but can’t access unnecessary sensitive files. This prevents cybercriminals from using any employee’s account to steal data, making things more difficult for them.
- Invest in SaaS DLP: While identity and access management (IAM) principles are important, IAM alone will never be enough. Your IAM strategy needs to be complemented by a more rigorous approach to cloud security management, focusing on access at the data level rather than the application level. An excellent cloud DLP solution gives you real-time visibility into user behavior and data movement in the cloud. It lets you see how users behave and uses automation and pattern recognition to spot and block suspicious behavior in real-time. At the same time, DLP uses predefined policies to find, classify and protect unstructured data across your cloud applications, ensuring that only authorized, verified users can access sensitive information.