MSPs, beware! Cybersecurity agencies across the world have recently warned about “an increase in malicious cyber activity, targeting managed service providers (MSPs) and expect this trend to continue.”
If you are an MSP, you need to bolster your security approach – and fast. Not only are hackers targeting companies like yours, but they are doing so with the broader aim of hacking your customers when they break into your infrastructure.
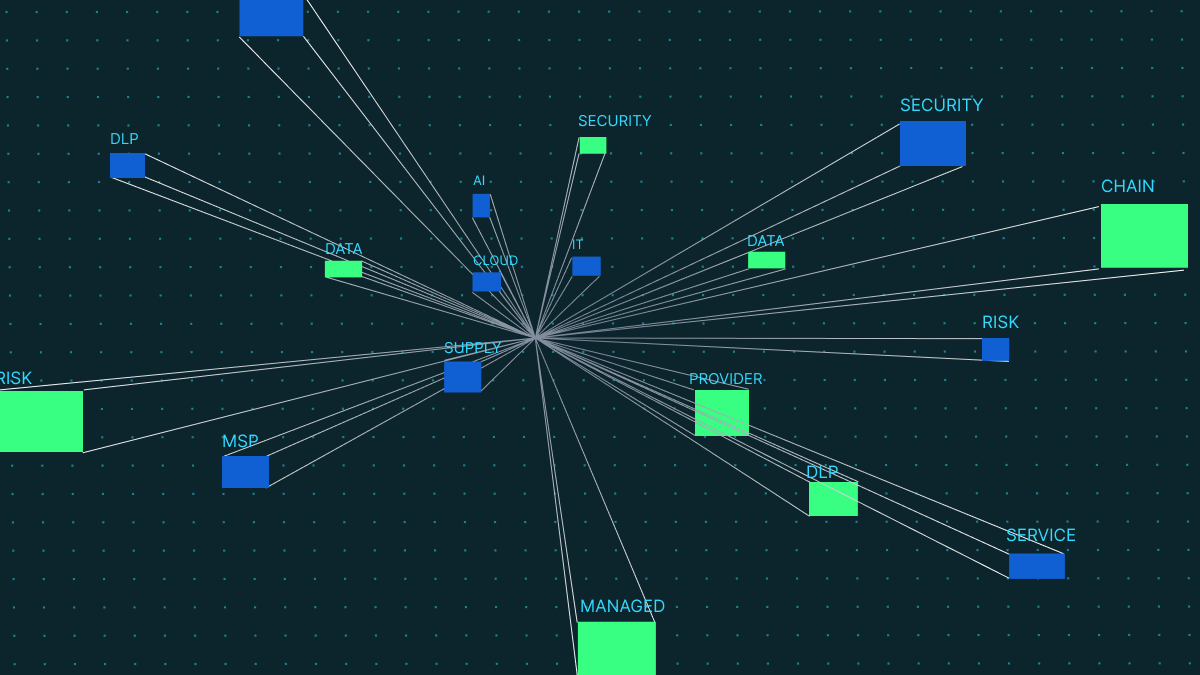
This form of attack is what’s known as a supply chain attack – a form of compromise that is increasingly popular amongst the cybercriminal community.
For MSPs, a successful software supply chain attack can not only result in downtime but can impact your reputation, lead to compliance fines and harm the bottom line long-term.
To help you protect your organization and your customers from compromise, we’ve written the MSP survival guide, which is full of tips to help you improve your security posture.
Let’s get started.
Challenges equate to opportunities for MSPs
While the cyber security risks to MSPs are undoubtedly mounting, they also present a significant opportunity. Increasingly, enterprises of all sizes are looking to MSPs to help them plug security gaps and reach compliance. At the same time, they’re also betting on MSPs to help them securely move to cloud-first, SaaS-based infrastructure.
For MSPs with a confident, thorough security approach, this is a huge opportunity to help customers discover new operational efficiencies, innovate their approaches and become more resilient.
Of course, though, to help your customers, you have to first be secure yourself. Unfortunately, research shows that most MSPs aren’t confident in their cybersecurity standing; they don’t have the right tools, processes and experience internally to facilitate their customers’ requirements – let alone secure their own infrastructure.
It’s clear that something’s got to give. This is a sink or swim moment for MSPs. They can either adapt, innovate and embrace a security-first culture…Or become a data breach statistic.
A framework for the MSP security evolution
To stay ahead of cybercriminals and offer their customers a solid security service, MSPs need to embrace the right tools. However, it’s all too easy to get bogged down by the sheer amount of security vendors and solutions out there, all promising to be the one saving grace for MSPs.
Honestly, we advise that you be extremely wary of any security vendor that promises to do it all. Instead, focus on taking a holistic approach.
Here’s what that looks like in a few actionable steps.
Cover the basics well
CISA’s notice to MSPs emphasizes the importance of covering security fundamentals flawlessly. You should put in place steadfast processes for the following, and advise your customers to do the same:
- Penetration testing and regular vulnerability scanning
- Automated patching
- Backing up critical systems and data
- Implementing MFA
- Utilizing anti-malware and anti-spam technology
Securely administer access to customer systems
One of the common security mistakes we see is MSPs using one login for accessing customer systems. However, doing this makes it much more difficult to detect cybercriminals. How can you tell who is who, if everyone is logging in from one account?
While it can be tricky to ensure your people don’t share login credentials, this is an essential security best practice. We recommend training your people on the risks of compromised credentials to drum home the importance of good password practices.
As well as this, you should put in place a strategy to dynamically authenticate and authorize users as they interact with customer resources. We advise deploying an identity and access management solution internally and then implementing a similar solution for your clients.
You should also make special considerations for privileged accounts within your IAM framework. They will need more rigorous monitoring, vetting and controls to prevent account compromise.
Take a data-centric approach
To protect sensitive data in third party environments, you have to first know where it is. This is where data classification comes in. It’s a process of organizing data according to its type, sensitivity, metadata, and perceived value to the organization.
Once you’ve classified customer data, you can implement a data-centric approach, which means using tools to secure data wherever it goes – including cloud applications like Slack, Teams and Zoom.
Traditional DLP solutions don’t protect customer data in these applications. To secure customer information in the cloud, you need next-gen data loss prevention (DLP).
Next-gen DLP works by monitoring, classifying and protecting sensitive data across cloud applications and collaboration tools. Through predefined policies, these solutions prevent data loss in real-time through automatic actions like redaction, encryption and deletion.
The best-in-breed cloud DLP solutions are also self-learning. They use AI to pick up on patterns about user behavior and sensitive data, and evolve their policies in line with this analysis. This takes the burden off your team having to re-define and set new data policies constantly.
Log everything!
Many of today’s data security regulations require rigorous reporting and auditing logs to demonstrate that data is secure – and it’s likely your customers will look to you to help with this. Ideally, your DLP solution can offer support here.
For example, our solution monitors, records and logs the journey of your sensitive data. Not only does this help you to make security improvements, but it makes the third party auditing process much more straightforward – the hard work is already done for you!
Plan for a cyber security incident
An incident response plan, as defined by NIST, is a “set of instructions or procedures to detect, respond to, and limit consequences of malicious cyber attacks against an organization’s information systems.”
Basically, your incident response plan is the rulebook that you follow in the event of a security incident.
Your incident response plan should include a number of playbooks, which will walk you through your response to specific threats, such as a phishing attack or credentials compromise in the cloud. We recommend looking at NIST’s resources on supply chain security and incident response management as starting points.
Be sure to rehearse your incident response plan regularly, so that you and your team feel well-prepared to action the plan if and when an incident occurs.
Final thoughts
With these fundamentals in place, your company is much less likely to suffer a security incident – and can also offer an enhanced security service to customers.
As always, value-adds are really important for customer relationships, so we will leave you with the advice to consider including employee security training in your offer to customers, which you can learn more about in this blog.