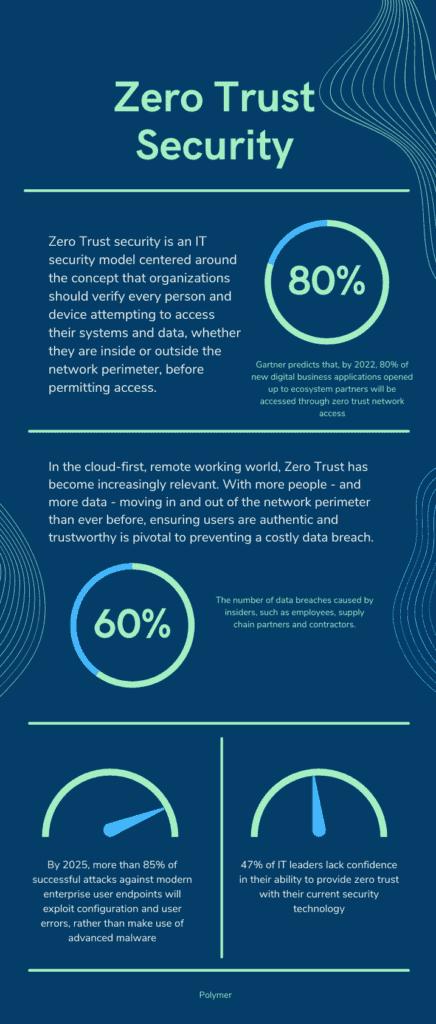
Zero trust security is an IT security model centered around the concept that organizations should verify every person and device attempting to access their systems and data, whether they are inside or outside the network perimeter, before permitting access. In essence, it’s the idea that no digital entity can simply be trusted to be who they say they are.
In the cloud-first, remote working world, Zero trust has become increasingly relevant. With more people – and more data – outside of the network perimeter than ever before, ensuring users are authentic and trustworthy is pivotal to preventing a costly data breach.
What makes zero trust different?
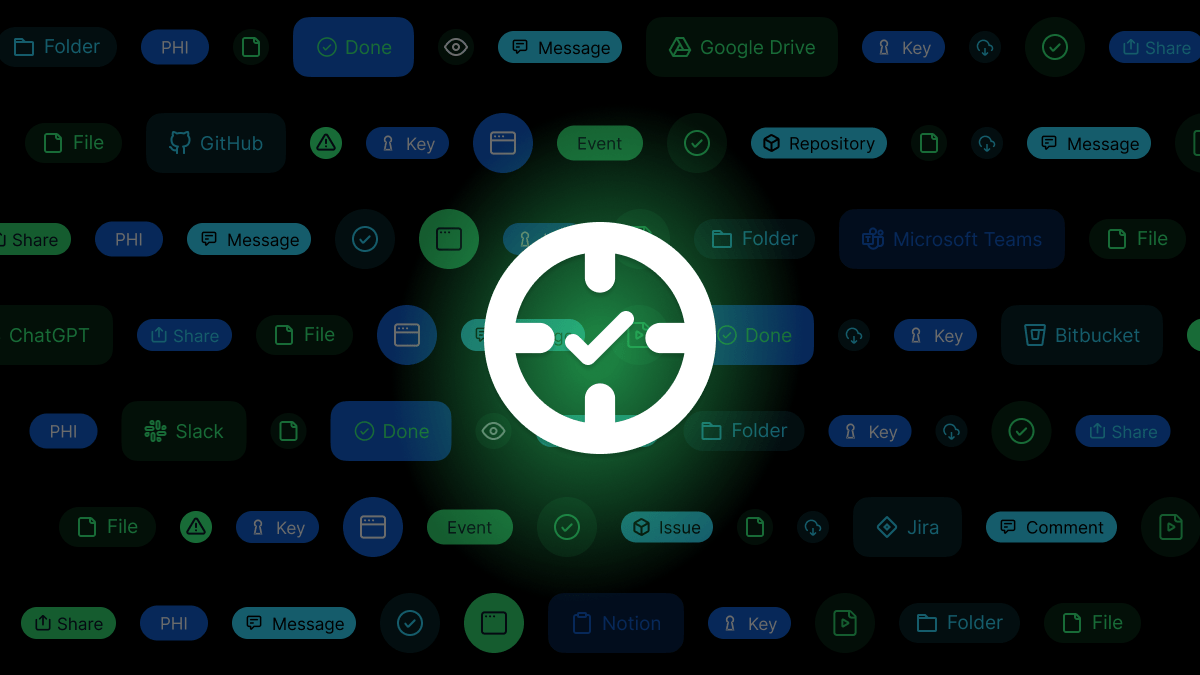
Zero Trust is not associated with one particular type of cybersecurity solution. It is more of a holistic approach, taking into account numerous technologies that are used in tandem, including multi-factor authentication, encryption, data loss prevention (DLP), identity and access management and endpoint security solutions.
It is an evolution from traditional network security approaches, designed to meet the data challenges of the modern world. Previously, security centered around the concept of “trust but verify”. This related to the “castle and moat” security approach, where users were automatically trusted once granted access to an organization’s network – usually through a one-time validation like entering a password.
In today’s workplace, “trust but verify” is widely thought of as outdated. Because of cloud adoption, the move to remote work and the increasing use of numerous collaboration tools and applications, the traditional network is disintegrating. The castle walls which once protected corporate data are now obsolete, replaced by a dynamic landscape of widespread endpoints, applications and users.
It is within this context that Zero Trust has become a necessity. In fact, Gartner predicts that, by 2022, 80% of new digital business applications opened up to ecosystem partners will be accessed through zero trust network access.
How does zero trust work?
Zero Trust architecture works by using a range of technologies to continuously monitor and authenticate users and devices. It enforces that users access only what they need to, and checks that users trying to access corporate data are genuine. Rather than validate users as a one-off, it encourages continuous authentication of access requests.
The approach relies on organizations having a deep understanding of their services and users, so that they can efficiently monitor and capture access attempts, and validate or deny them as needed in real-time, depending on if the user appears suspicious. Factors that could indicate suspicious activity include logging on from an unknown device or a user attempting to login from a new location.
From a data protection perspective, a Zero Trust approach has numerous benefits, including:
- Protection by isolation: Protects the network even if access vectors are compromised, like endpoint devices, cloud services, and even supply chain providers.
- Additional layer of security: Zero Trust is more robust than firewall rules, packet analysis, and endpoint protection.
- Continuous monitoring: Even if an attacker somehow gains access to the corporate network, real-time threat monitoring and behavioral analysis can identify those who got through the perimeter.
- Critical in remote connections: Remote endpoint devices are susceptible to more attacks outside the office, from phishing and social engineering attacks to malware, missed updates or even loss or theft. A Zero Trust policy can identify the device’s anomalous behavior inside the system and boot it out.
Challenges in implementing zero trust security
While Zero Trust has numerous benefits, it is not straightforward to implement. It is important for organizations to understand the common challenges that hinder Zero Trust deployment, so that they do not fall at the same hurdles.
- It is not like flipping a switch: Because Zero Trust is a holistic approach, it is not quick or easy to roll out. It relies on a synergy of solutions working together, as well as an underlying change in enterprise cybersecurity culture. It’s therefore important that organizations take a gradual approach to implementing zero trust, ensuring that nothing is overlooked as legacy solutions are replaced.
- It requires dynamic, ongoing monitoring and administration: Zero Trust is not a security solution that can be left to run by itself. Organizations’ users are constantly changing and evolving. People leave their jobs and new people join. To be effective, Zero Trust permissions will need to be updated in near real-time, in line with employee changes. Otherwise, users who should no longer have legitimate access may still be able to download and interact with a wealth of sensitive data.
- A potential hindrance to productivity: If poorly implemented, a Zero Trust approach can be a time and productivity drain for well-intentioned employees. They may find themselves blocked from accessing the files and data they need, leading to frustration and a negative impact on their work.
- The prevalence of Shadow IT: To be effective, Zero Trust requires complete visibility into the IT estate, including the digital supply chain, cloud applications and all users. If organizations fail to effectively establish this baseline to build upon, their initiative will be undermined by unknown applications and users who still retain the power to leak data, be it maliciously or unintentionally.
3 steps to starting with zero trust
Zero Trust is the future of enterprise security. However, it is not an overnight change or quick transformation. Many organizations will, to some extent, already be using some of the principles of zero trust. It is now critical for them to build on these foundations.
Here’s how to get started if you are at the beginning of your journey.
Step 1: Identify your users
Zero trust begins with an understanding of your company’s user base. To enforce zero trust without hindering productivity, you should implement tools like Identity and Access management with single sign-on. You should ensure that only users who are verified through these tools can access corporate data and applications.
Step 2: Protect your data
Just because a user has verified access to corporate data, that doesn’t mean they should be fully trusted. This means that, as well as authenticating users, additional steps should be taken to prevent accidental data loss or data exfiltration. Utilizing a cloud-based DLP solution, or Cloud Access Security Broker, provides real-time visibility into how users are interacting with sensitive data. As well as visibility, these solutions also use pre-defined policies to prevent data from being unlawfully shared or moved.
Step 3: Include cloud applications
Collaboration tools like Slack, Box and Outlook should all be considered within the Zero Trust model. Security controls, including DLP and user behavior monitoring, should extend to these cloud applications, where it is extremely common for data leakage to occur. For example, using data redaction, a next-gen DLP solution can prevent an employee from using Slack to share sensitive data with an unauthorized user in real-time.
For organizations concerned about the move from legacy systems to a Zero Trust approach, a good place to start is with the deployment of a next-generation, cloud-based DLP solution like Polymer DLP. These solutions are built on a zero trust framework. They incorporate security features such as identity and access management, along with data protection and redaction in cloud applications, to prevent unauthorized or suspicious users from misusing sensitive data.