Lurking in the shadows of every organization, employees are accessing, transferring, and downloading sensitive company information – without the IT team’s oversight.
This is shadow IT: the use of technology systems, like applications, devices and cloud services, that are not approved by the IT department.
Picture this: an employee installs Slack, which is not the company’s official channel for communication. A few months later, they neglected to update the app, which contained a security patch that fixed a critical vulnerability.
Or a VP needs to take a PowerPoint presentation home to complete it. But the company’s email server won’t allow attachments of that size. Rather than using a flash drive, they upload the file to Dropbox, which isn’t permitted. In doing so, they breach compliance regulations, as the file contains personal information.
Other common sources of shadow IT include:
-Messaging: including popular apps which may not be authorized like Messenger, Slack, or WhatsApp
-Productivity Tools: Ticketing systems like Asana, Trello, Jira & Zendesk
-Email: Employees’ personal emails that can be accessed via the web using company firewall or devices
-Data Storage: Cloud Based Storage systems like GDrive, Box, Dropbox and S3.
Benefits of using shadow IT
Employees unintentionally engage in shadow IT all the time. Most are looking to improve efficiency by taking advantage of the many cloud applications and collaboration tools that are out there. Here’s why:
Increased productivity: Organization-mandated software can sometimes hinder employee output. If the user experience is clunky, or the tools offered don’t meet their needs, then they may look to circumvent these applications in favour of personal ones that make their jobs easier. Even C-suite executives may collaborate on these tools, creating a workplace culture where shadow IT is encouraged.
Better business fit: IT solutions do not always evolve with the pace of business needs. To adapt quickly to solve a business challenge or conquer a new opportunity, employees may therefore engage with unsolicited applications. As Gartner puts: “Shadow IT will generally yield a solution more closely aligned with the original business need, with less emphasis on technology capabilities and more emphasis on the appropriateness, alignment, and the speed of delivery.”
Innovation: Experimentation and thinking outside-the-box can lead to better output. Some shadow IT applications and tools address gaps between what the organization needs and what their officially recommended tools fail to provide.
Personal preference: New solutions can be downloaded at the click of the button. If employees have interacted with a service in their personal life or heard good recommendations from a colleague or friend, they may simply prefer to use it. They are also generally more productive and engaged when using their own systems.
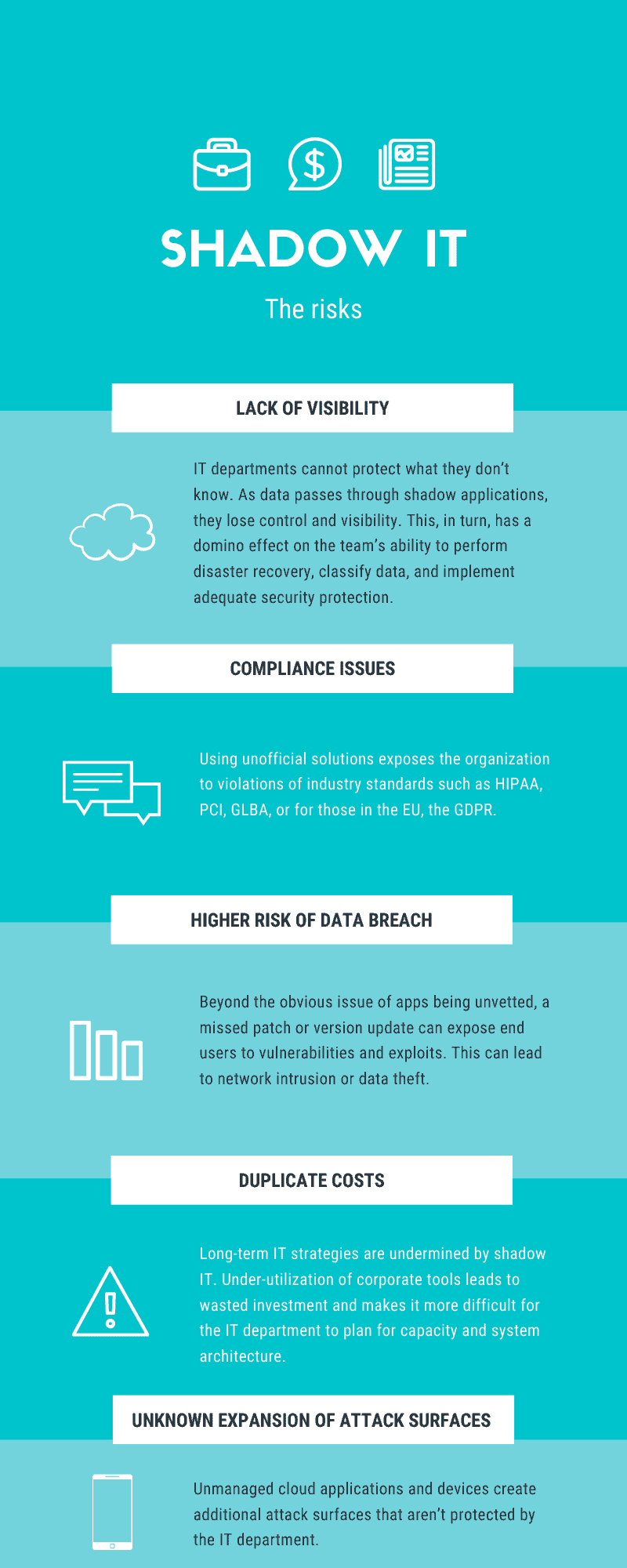
Risks of using shadow IT
While shadow IT applications are generally used with good intentions, the security risks of unvetted and unauthorized solutions cannot be ignored, especially for businesses that fall under strict compliance regulations. The top risks are:
Lack of visibility: IT departments cannot protect what they don’t know. As data passes through shadow applications, the IT team loses control and visibility. This, in turn, has a domino effect on the team’s ability to perform disaster recovery, classify data, and implement adequate security protections.
Compliance issues: Using unofficial solutions exposes the organization to violations of industry standards such as HIPAA, PCI, GLBA and GDPR. Something as simple as transferring files with personally identifiable information can be classified as a compliance violation and lead to hefty fines.
Higher risk of data breach: Beyond the obvious issue of apps being unvetted, a missed patch or version update can expose end users to vulnerabilities and exploits. This can lead to network intrusion or data theft.
Duplicate costs: Long-term IT strategies are undermined by shadow IT. Under-utilization of corporate tools leads to wasted investment and makes it more difficult for the IT department to plan for capacity and system architecture.
Unknown expansion of attack surfaces: Unmanaged cloud applications and devices create additional attack surfaces for cyber attackers to penetrate – and these will not be under the protection of corporate IT.
By the numbers: shadow IT statistics
-1 in 5 organizations suffer cyber attack due to shadow IT according to IBM study Perception Gaps in Cyber Resilience: Where are your Blind Spots?
-30%-50% are the estimated IT spending accounted for by shadow IT solutions, according to Gartner
-975 are average number of unofficial cloud services used by an organization.
-80% percentage of employees who admit to using SaaS solutions without getting approval from IT
–67% of teams use their own collaboration tools outside of official company software
-8% of enterprise know the full scope of shadow IT within their company
Shadow IT: a lurking threat
Shadow IT has long been a threat to organizations but, in the age of COVID-19, it is even more dangerous. As employees continue to work from home, many are looking to unofficial third-party applications to help them. In fact, research from earlier this year shows that over 40% of file-sharing traffic is now going through unapproved services.
With the proliferation of cloud applications, it’s near-impossible to stop employees from sharing data via unmanaged services. At the same time, these tools render traditional endpoint protection, firewalls and patch protection obsolete.
This is a data breach waiting to happen. IT teams must therefore strike a careful balance: controlling shadow IT, without hampering employee productivity and enterprise innovation. DLP is the answer.
These solutions use API controls to monitor and secure corporate data as it travels through cloud applications. They scan data in real-time to discover third-party cloud services that the IT team may not be aware of, and then use risk-based analysis to determine appropriate security policies. Effectively, they shine a light on shadow IT – giving the enterprise the deep visibility they need to enable adequate protections and meet compliance.
As well as this, CASB tools can integrate data loss prevention (DLP) to prevent sensitive data from being downloaded, uploaded or moved to unsanctioned devices or applications.
Ultimately, collaboration tools like Slack, Dropbox and Zoom are useful for employee productivity. It’s important that IT teams don’t block these applications. Doing so just encourages employees to find new shadow IT tools to get their work done. So, IT leaders must embrace the issue – and look to CASB instead. With the right solution in place, they can enable workplace innovation and efficiency, as well as ensuring compliance and data security.
Polymer is a CASB 2.0 framework that protects against data loss (DLP) on modern collaboration tools like Slack, Dropbox, Zoom, GitHub, Jira, Zendesk and more with alerting & real-time redaction of sensitive and regulated information such as PII, PHI, financial and security data.
Polymer protects against data loss (DLP) on modern collaboration tools like Slack, Dropbox, Zoom, Github and more with alerting & real-time redaction of sensitive and regulated information such as PII, PHI, financial and security data.