Back in 2011, a botnet managed to infect an estimated 1 million computers worldwide. Known as GameOver Zeus, the infamous malware was programmed to specifically steal banking credentials.
It then used the captured banking information to initiate or re-direct wire transfers, managing to steal over $100 million from individual users, businesses and organizations. It took 3 years and a transnational investigation before the botnet was finally taken down in 2014.
You might think that three years is a long time for the feds to catch criminals stealing that much money. But, as with many things in the cybercrime sphere, the case isn’t straightforward. You see, the hackers didn’t steal money from plain sight. Instead, all the wire transfers they made actually looked legitimate. How?
By using IP spoofing.
What is IP spoofing?
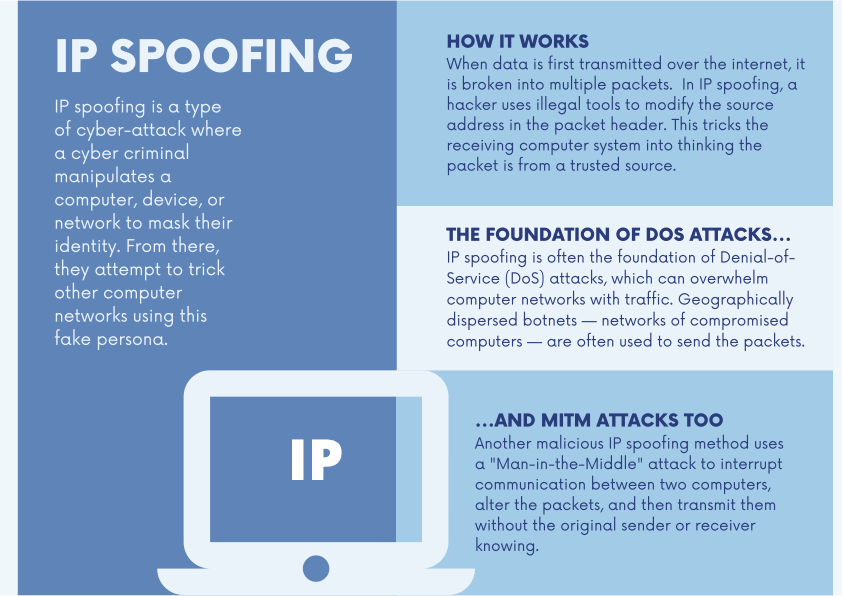
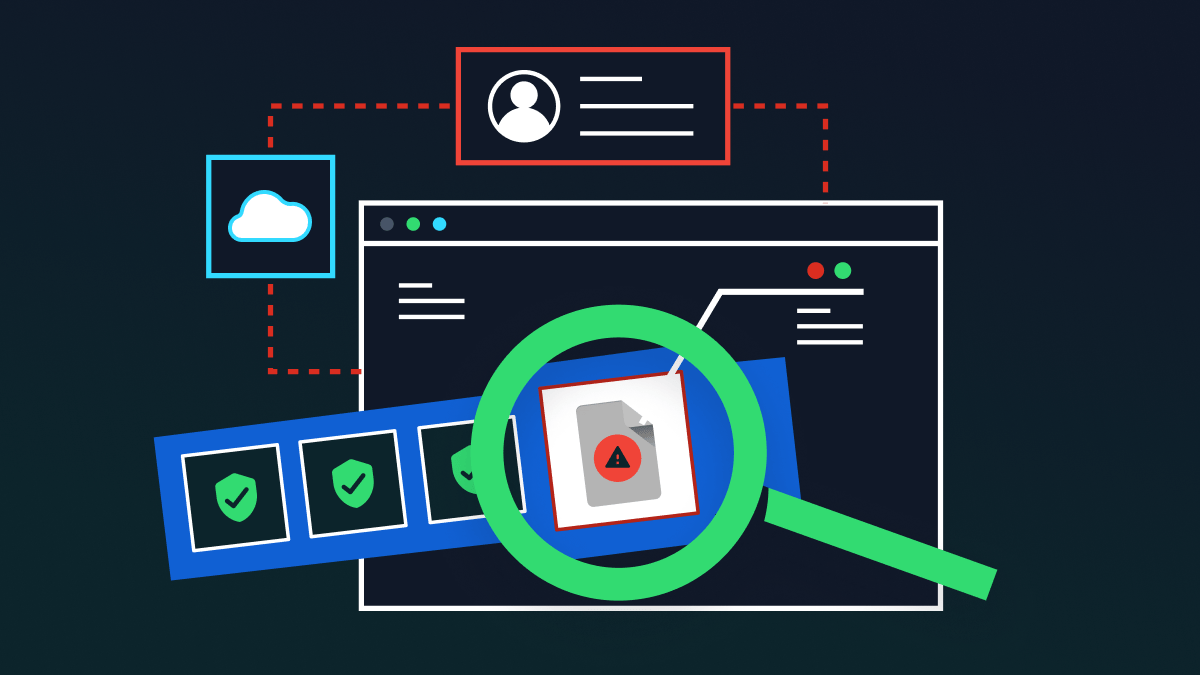
Spoofing is a type of cyber-attack where a malicious actor manipulates a computer, device, or network to mask their identity. From there, they attempt to trick other computer networks using this fake persona to gain access or carry out transactions that look like it came from a legitimate party. In other words, it’s a high-tech form of impersonation.
IP spoofing manipulates internet transmissions. When data is first transmitted over the internet, it is broken into multiple packets. Those packets are transmitted independently and reassembled at the end. Each packet has an IP (Internet Protocol) header that contains information about the packet, including the source IP address and the destination IP address.
Methods of IP spoofing
- In IP spoofing, a hacker uses illegal tools to modify the source address in the packet header. This tricks the receiving computer system into thinking the packet is from a trusted source, and accepts it. Because this occurs at the network level, there are no external signs of tampering.
- IP spoofing is often the foundation of Denial-of-Service (DoS) attacks, which can overwhelm computer networks with traffic. Geographically dispersed botnets — networks of compromised computers — are often used to send the packets.
- Another malicious IP spoofing method uses a “Man-in-the-Middle” attack to interrupt communication between two computers, alter the packets, and then transmit them without the original sender or receiver knowing. Over time, this enables hackers to collect a wealth of confidential information they can use or sell.
- IP spoofing can be used to bypass IP address authentication. The idea behind the “castle and moat” defense is simple. Those outside the network are considered threats, and those inside the castle are trusted. Once a hacker breaches the network and makes it inside, it’s easy to exploit the system.
What makes IP spoofing dangerous
As indicated above, the key threat posed by IP spoofing is that it’s difficult to detect. It happens before malicious actors attempt to access the target network, or initiate communication with a target. This means victims are often none the wiser until it’s too late.
Here are some examples that highlight why IP spoofing can be difficult to intercept:
It’s more insidious than phishing – A successful spoof does not show any of the signs of phishing. Instead, it merely redirects the communication or transaction intended for a legitimate receiver to a hacker who has spoofed the device’s IP address.
It can bypass firewalls and perimeter security – A sufficiently large attack allows external actors to bypass security systems and flood the network in order to cause temporary disruption or shut down services. In fact, services such as remote procedure calls and R services suite luike rlogin and rsh are vulnerable to IP spoofing, so errors like “the remote procedure call failed” should not be taken lightly.
It provides extended concealment – Like a sleeper cell, a spoofed IP allows hackers to access systems for extended periods under the guise of a trusted user.
More connections are being made remotely – In the post-Covid era, the shift to remote work means that more users and devices are connecting to the network from outside. This greatly increases the risk of IP spoofing, and it only takes one spoofed device to compromise the network.
Other types of spoofing
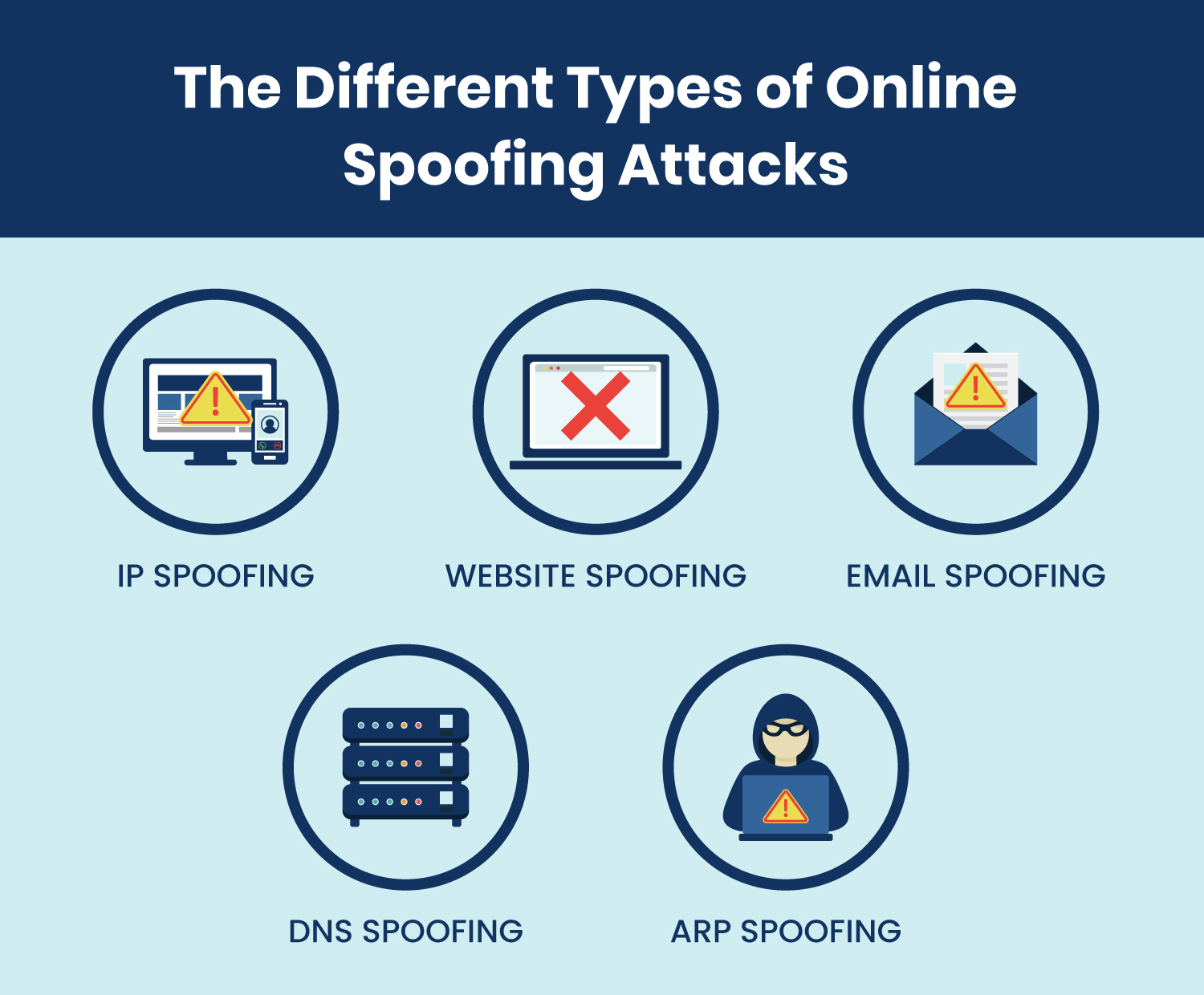
IP spoofing isn’t the only type of attack you need to watch out for. There are other kinds of spoofing too – as we’ll explore below.
- URL: A spoofed URL takes the form of a fraudulent link that looks eerily like a legitimate one. Cyber criminals rely on victims not closely checking these deceptive links before clicking on them. Once the victim does click, the cyber criminal may either infect their device with malware, or steal sensitive details that are entered on the phony page. These days, with the rise of URL shorteners like bit.ly on social media, it’s even harder to detect spoofed URLs – as it is hard to discern an authentic shortened link from a malicious one.
- Email: Email spoofing is often the basis of phishing attacks. It involves tricking the recipient into thinking an email came from a legitimate source – such as an official body or a person they know. They work by forging email headers to make them look real. It’s only when the recipient inspects the sender address closely that they’ll see the discrepancy. Less alert users may be tricked into sharing sensitive details, clicking a malicious link, or even wiring company money to the malicious sender. A vivid example is the Crelan Bank heist of 2016, when hackers successfully phished the CEO’s email account, and tricked an employee into wiring over $75 million. Even worse, the attack was only discovered after an internal audit.
- DNS: Domain Name Server (DNS) spoofing is a type of attack that uses altered DNS records to reroute online traffic to a phony website that looks a lot like the real destination. From there, the victim will be asked to login into their account, while in the process sharing their credentials with cyber criminals. These websites often also deploy malware onto the victim’s device.
- ARP: Address Resolution Protocol (ARP) is a protocol for enabling network communications to reach a certain device that’s on the network. ARP spoofing is a common Man in the Middle attack. It enables attackers to ambush communications between network devices. To do this, the attacker needs to have network access. From there, they can use spoofing tools to send out phony ARP responses to fool different devices into thinking they are communicating with each other. Once this is complete, the devices will transmit information to the attacker rather than to each other.
How to defend against spoofing attacks
While it’s scary to realize how many kinds of spoofing attacks there are out there, there’s also tons of ways to defend against them. Cyber criminals are smart but cyber security solutions are just as intelligent. You just need to know the right ones to use. These include:
1. Firewalls and spoofing software
Firewalls are your first line of defense, so make sure they are configured and updated regularly. Many firewall vendors include anti-spoofing solutions in their offerings, which helps to defend against all the kinds of spoofing attacks we’ve talked about above. As well as firewalls, there are several dedicated solutions for spoofing attacks – such as NetCut and Arp Monitor. These tools help to discover spoofing attack attempts before they wreck havoc on your company.
2. Encryption protocols
Make use of upper layer protocols that have built-in safeguards against spoofing. One such protocol is TCP, which uses sequence numbers that are negotiated with the remote machine. This forms a layer of protection against hackers who are unable to see the reply packets and thus determine the sequence number.
3. Packet filtering
Packet filtering is the process of examining IP packets for each user and device that connects to the network. A packet filtering firewall pays close attention to the header and the IP address to determine if it matches the source and if there are any suspicious discrepancies. In the event of an anomaly, the packet will not be allowed to complete the connection. A good zero-trust approach also pays equal weight to ingress and egress filtering.
4. Training nudges
Sometimes, despite your best efforts, a spoofed URL or email will make its way into your employees’ laps. As they say, knowledge is power, meaning your best defense is ensuring your employees know about spoofing techniques. On-the-go cybersecurity training is your best bet here. This is an intelligent, real-time form of training that reacts dynamically to your employees’ actions. For example, if they receive an email from an unknown address, the nudge program will prompt the user, asking them to check if the email is safe to open and reply to.
5. DLP
Cyber criminals are often after your sensitive data when they conduct a spoofing attack. So, protecting your data – wherever it may be – is crucial. The best way to do this is through next-generation data loss prevention (DLP) software like Polymer DLP. The next-generation of DLP protects your data not just in the network, but across the cloud and collaboration tools. It can stop employees from sharing sensitive data with unidentified or suspicious users, and also protects data in motion – preventing it from being opened even if it is intercepted by a malevolent actor.