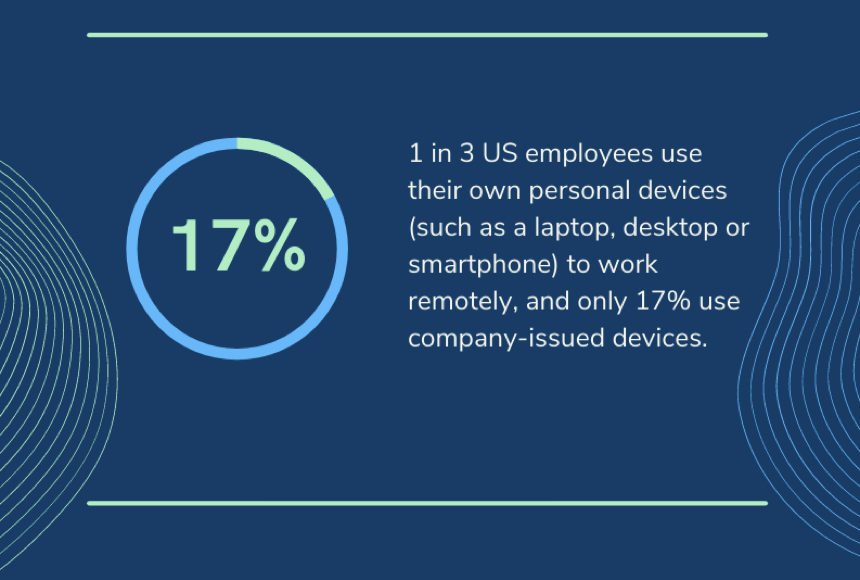
According to Gartner research, between 30 and 40% of employees will continue to work remotely after the end of the pandemic. It’s clear that distributed work is here to stay. So, it’s time for IT teams to rethink their strategy and build a security stack that is appropriate for the remote world.
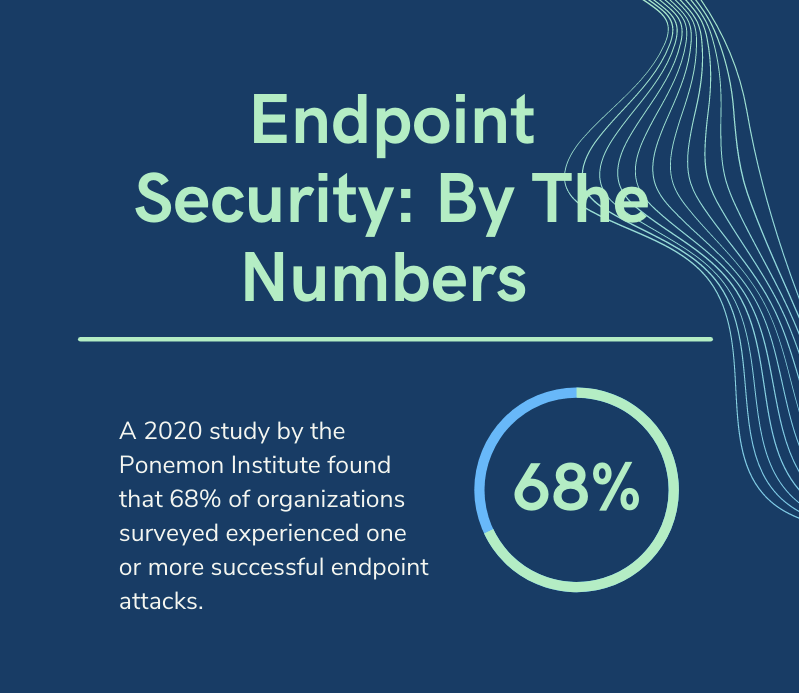
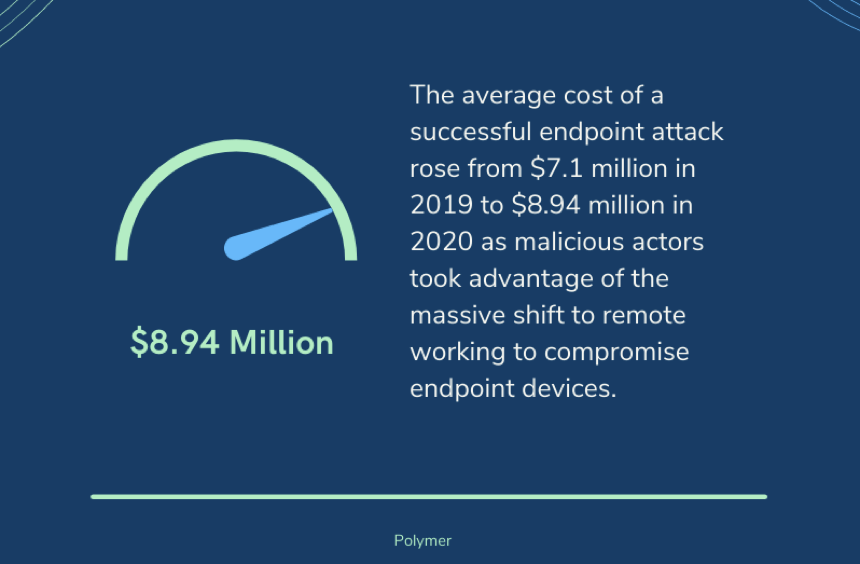
The first line of defense in this new paradigm is the endpoint: the devices that employees use – day in and day out – to access corporate resources, collaborate with colleagues and complete their work. According to Ponemon research, 68% of organizations experienced one or more endpoint attacks that successfully compromised their IT infrastructure in 2020. The same report also found that endpoint attacks had increased year-on-year.
It’s no wonder this is the case. In the remote working world, endpoints are a favorable target for cybercriminals. Think of how many devices employees can use to access the enterprise network: their work laptop, their personal computer, their personal cell phone. All of these devices offer a potential entry point for malicious actors. Because there are so many endpoints out there, the opportunities for malicious activity are exponential. This is why IT teams need to make endpoint security a priority.
What is endpoint security?
Endpoint security is a term to describe a range of security solutions that protect against endpoint security threats, such as zero-day attacks, malware and human error.
Anti-virus software alone is not enough to protect devices in the remote working world. Endpoint protection provides a holistic and centralized solution to protect endpoints that are connected to the corporate network – no matter where they are connecting from in the world.
Why endpoint security is important
In the remote working world, the traditional security perimeter has become obsolete. Employees have the potential to access the corporate network from a multitude of places and devices. Left unmanaged and uncontrolled, this environment creates a data security nightmare.
Firstly, this is because endpoints are a common entry point for cyber attackers, who use tactics like phishing and malware to infiltrate an end device, and then sneak into corporate networks and applications to steal sensitive data.
Secondly, without endpoint protection, it is inevitable that an organization will lose oversight of where its sensitive data is stored and how it is shared. Not only does this have compliance implications, but it puts sensitive data at risk of a breach, should a device be lost, stolen or compromised.
Effect on insurance costs from endpoint vulnerabilities
One the largest cybersecurity insurance cost arises from the safety measures put in place by the insured firm. Most insurance contracts stipulate that these precautionary security safeguards were sufficient. In the event that a breach occurs, proving this can be difficult. Having an effective end point security program is table stakes in clearing the bar to be fully compensated for any claims.
What are the components of endpoint security?
Luckily, today’s endpoint security solutions are designed to prevent malicious infiltration and data loss, giving IT teams much needed control over endpoints and the data on them. Here are the key solutions to consider when designing your endpoint strategy:
Antivirus and anti-malware protection: Antivirus protection was the first wave of endpoint security, and is still an integral feature of today’s solutions. It works by preventing malware from infiltrating an endpoint. For example, should an employee receive a fraudulent email that contains malware, the solution works by detecting the suspicious file, quarantining it and removing it – before it causes any damage.
Web security: Web browsers are now a common interface that employees use to access work applications, making it easy for them to conduct work from any device or network that connects to the internet. However, browsers also present a host of risks. From malicious websites to security vulnerabilities, browsers need to be protected. This is where web security filters and gateways come in. Filters can be deployed onto endpoints to control access to websites, and prevent employees from accidentally downloading malicious files. Web gateways go a step further, incorporating features such as user behavior analytics to identify and mitigate complex threats like zero-day malware.
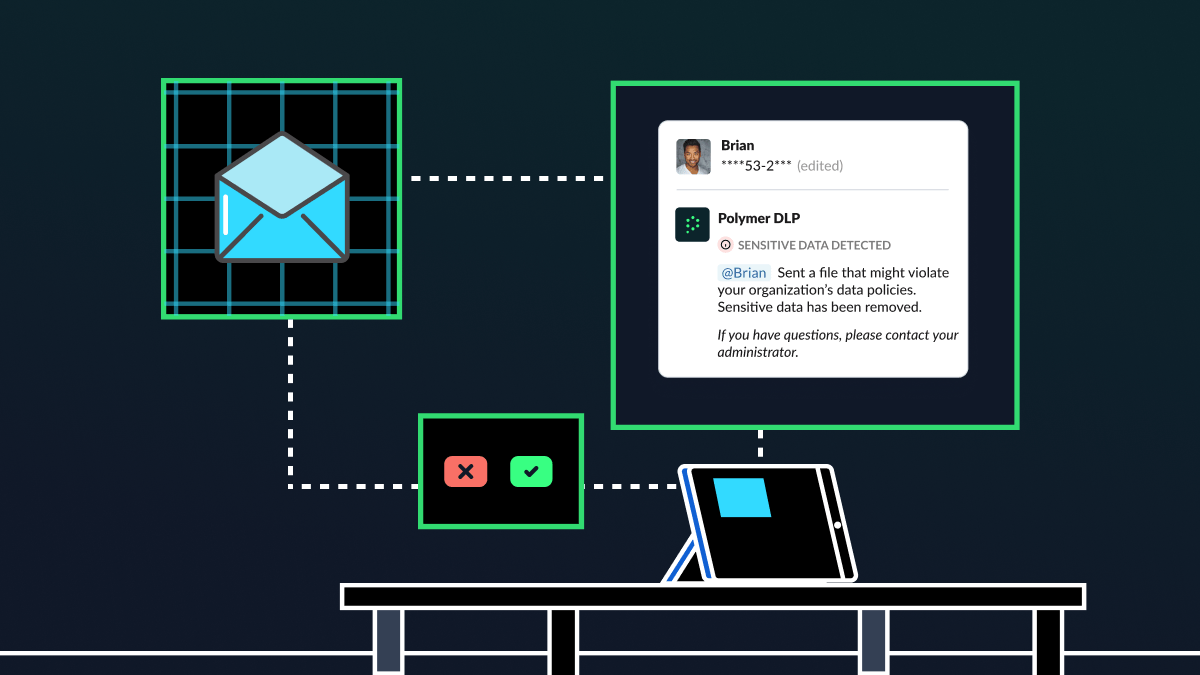
Data classification and DLP: Data classification and data loss prevention (DLP) work in tandem to protect sensitive data from being shared with the wrong person – maliciously or unintentionally. These solutions work by first classifying data into categories, based on risk and sensitivity. The DLP solution then monitors this data in real-time, as it moves between applications, collaboration tools and emails, to ensure that only authorized individuals are able to access it. Any organization that collects personally identifiable information (PII), protected health info (PHI), or payment card info (PCI) must enforce DLP policies, in line with regulations such as HIPAA and the EU’s all-encompassing GDPR.
As organizations continue to embrace the hybrid world of work, endpoint protection is a vital part of a modern cybersecurity strategy. Every single endpoint connected to the corporate network acts as a gateway into the enterprise, so protecting these devices – and the data on them – is integral.