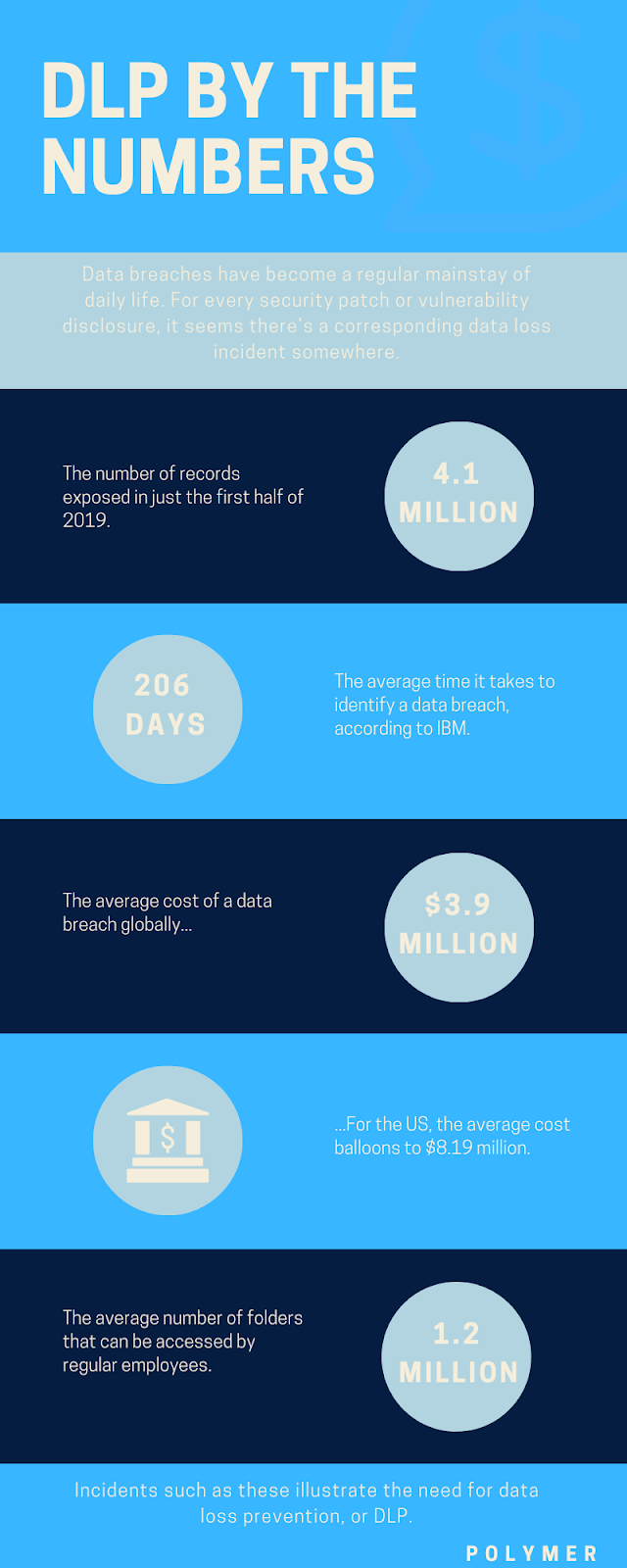
Data breaches have become a regular mainstay of daily life. For every security patch or vulnerability disclosure, it seems there’s a corresponding data loss incident somewhere.
Consider the following recent incidents:
- Hackers penetrate security camera startup Verkade, potentially affecting up to 150,000 CCTVs worldwide.
- Home-based healthcare provider Elara Caring discloses a phishing attack that may have accessed the records of over 100,000 patients
- A consumer privacy watchdog found that a Covid-19 testing company in Utah stored information on publicly accessible servers, impacting up to 50,000 customers.
And those are just over the past week, not even counting the worst data breach incidents that affected Forbes 500 companies like Yahoo, eBay, and Marriott in the past.
Incidents such as these illustrate the need for data loss prevention, or DLP.
What is data loss prevention?
DLP is a technology-based strategy for ensuring compliance and protecting sensitive data, including intellectual property, financial information and personal details. DLP works by analyzing, inspecting and encrypting data both at rest and in motion: whether it is being sent or received through messaging applications, downloaded to an end user device or being stored in the cloud.
It’s helpful to think of DLP as a small, invisible lock around your company’s sensitive data. As the security team, you decide which users get the keys. Through predefined policies, real-time alerts and remediation tools, these solutions also help you to monitor, respond and protect against any employee – or unauthorized third party – who is trying to break the lock without access.
To achieve compliance at the same time, DLP policies are often guided by regulatory standards like HIPAA, GDPR, and PCI-DSS.
Here’s an overview of the DLP process in action:
- Identification: Through real-time monitoring, DLP identifies a threat to data security based on predefined policies .
- Sounding the alert: The solution alerts the security team to the threat for visibility.
- Enforcing remediation: At the same time, DLP automatically encrypts the data in question to prevent a data breach.
- Reporting: To meet compliance standards and audit requirements, DLP provides reporting functionality so organizations can prove that data is being used correctly and any incidents have been avoided.
DLP vs CASBs
If you read our previous article on CASBs, you might be thinking that the two sound similar. While there are some overlaps, the main difference is their architecture. Traditional CASBs work by using proxies: either an agent is installed on end user devices to monitor data, or an agent is placed in the cloud to monitor data in transit between cloud services and end users.
However, with the proliferation of working from home, more users are accessing company data through unmanaged devices, collaboration tools and unmanaged services, creating blind spots in the CASB framework. For example, traditional CASB solutions aren’t able to monitor how sensitive data is being shared in collaboration tools like Slack. This is where cloud-based DLP has come into play.
Using APIs, cloud-enabled DLP extends data protection outside of the corporate network and directly into SaaS applications, giving security teams much needed control and visibility over how data is being used and stored – no matter where it travels. Confusion sometimes arises because a few CASB vendors have evolved their solutions to use APIs, creating a set of solutions that can be classified as either cloud-based DLP or CASB.
What are the common causes of data loss or leaks?
One of the reasons that data breaches are on the rise is because there are so many possible avenues for data leakage and theft. Below, we explore the most common data security threats that you need to be aware of.
- Hacker intrusion: The University of Maryland quantified that, every 39 seconds, hackers attempt to attack computers with internet access. Your organization’s intellectual property, personal data and financial information is a gold mine for hackers, who can use it for a wealth of malicious activities, such as phishing scams or selling it on the dark web.
- Unsecured endpoints: Many people are now working from home, outside of the corporate network. In this new setting, employees may be accessing corporate data from their own devices, rather than company machines, and connecting to unsecured Wi-Fi to get work done. Endpoints also extend to devices like USB devices, which are easy to lose. In fact, in 2018, the UK’s Heathrow Airport was fined £120,000 because a USB device with company information was found by a member of the public.
- Negligent data exposure: People are not perfect. In the busy work environment, it is easy to make mistakes, and security is rarely top of mind for employees. This puts data at risk of an accidental breach. In fact, research shows that 90% of data breaches are due to carelessness. Common examples include accidentally sending an email with confidential information to the wrong person, not configuring a database with access privileges and leaving it open to anyone, and poor password practices.
- Insider threat: We have covered what’s termed the ‘accidental’ insider threat above. But it’s also important to be aware of malicious insiders. These are employees (or even ex-employees) who intend to steal company information for their own gain – be it to take it to a competitor as they leave the business, or to sell it for money. A high profile example is the Coca-Cola case, where an ex-staff member was found to be in possession of a company hard drive, containing PII of 8000 employees.
- Cloud-based vulnerabilities: 93% of companies are concerned about cloud computing security risks. Its infrastructure is inherently complex, but the shared responsibility model of the cloud means that organizations must take security seriously. Common data protection issues in the cloud include misconfigured cloud storage, improper access controls and the misuse of employee credentials.
- Failure to patch: Security patches fix software vulnerabilities that cybercriminals can take advantage of. Without automatic patch management on all devices accessed by employees, organizations are at risk of data theft. In fact, nearly 25% of all businesses have experienced a cyberattack due to unpatched vulnerabilities. A well-known example of the failure to patch is the WannaCry ransomware, which related to a vulnerability in Microsoft Windows.
What are the components of DLP software?
With so many threats out there – spanning across every facet of the corporate IT ecosystem – cloud-based DLP software offers a solution to protect data from all angles. This is because it is data centric. Rather than focusing on securing an endpoint or the corporate network, it focuses on safeguarding data wherever it goes.
You should look for a DLP solution that protects all 3 types of data:
- Data at rest: This refers to data that is not actively being used. It can be stored in a number of places, including the cloud or on a hard drive. DLP protects this data using encryption.
- Data in motion: This is data that is in transit between two places – for example, through the internet. Using traffic analysis tools and encryption, DLP safeguards this data as it travels.
- Data in use: This defines data that a user is interacting with, like editing a document, or attaching a sensitive file to an email. Through real-time analysis, DLP monitors and protects this data from unauthorized access as needed.
What are the use cases for DLP?
Across industries, DLP is a common tool used to ensure data security. In fact, in highly regulated industries, DLP is not just recommended, but required to meet compliance standards. Here are the top use cases:
- For personal information protection: Any organization that collects personally identifiable information (PII), protected health info (PHI), or payment card info (PCI) must enforce DLP policies, in line with regulations such as HIPAA and the EU’s all-encompassing GDPR make such protection required for compliance.
- Intellectual property protection: Research shows that 95% of breached records come from government agencies, retail, and technology sectors. It’s no wonder this is the case, because these industries hold a wealth of trade secrets and IP. If this gets into the wrong hands, it could have a devastating impact on corporate reputation and the bottom line. In the case of federal agencies, for example, data can often involve national security – which is why cybercriminals and state-sponsored actors are keen to get their hands on it. DLP is essential for ensuring this kind of data stays safe.
- Secure workforce outside the office: The pandemic has changed the working environment for the foreseeable future. Many of us now work from home. Telecommuting and BYOD bring a new host of data security challenges, because data is now living mostly outside the corporate network. With cloud-based DLP, security teams can drastically reduce the likelihood of data leakage and breaches in the remote working world.
- Achieve data visibility: Auditing and compliance requirements mean that organizations need to prove they know where their data is, where it’s been and how it is being used. Through its reporting tools and real-time analysis capabilities, DLP gives organizations traceability and transparency over their sensitive data.
DLP: By the numbers
If you are looking for a DLP solution, check out our DLP for SaaS buyers’ guide.