Background on Cozy Bear
Cozy Bear is a Russian cyber-espionage group classified by the United States federal government as advanced persistent threat 29 (APT29).
It’s responsible for several high-profile data breaches over the last few years, including the SolarWinds attack and recent Google Drive phishing scams.
While APT29 is notorious in the public domain, the group’s infamy hasn’t impacted its capabilities. It continually wreaks havoc on government agencies and associates in NATO countries.
APT29’s latest offense targets Microsoft 365. While this campaign’s details are only coming to light, it appears these attacks have been going on for months.
The sophistication of APT29 cannot be underestimated. This group consists of highly-proficient threat actors who use a variety of tactics, techniques and procedures to compromise their targets without raising the alarm.
Is my organization vulnerable to Microsoft 365 compromise?
Cozy Bear’s exploitation of Microsoft 365, thus far, seems highly targeted and purposeful. This isn’t one of those campaigns that attempts to catch as many people and organizations as possible.
The targets are government organizations that play a role in crafting foreign policies for North Atlantic Treaty Organization (NATO) countries. In this way, Cozy Bear’s current mission appears to be one of espionage.
However, while government agencies are currently the primary target, organizations in other sectors cannot rest on their laurels. As we saw in the SolarWinds attack, cyber-attacks can often spill over, causing turmoil for organizations associated with the original target.
Moreover, we must remember that cyber-criminals outside APT29 may replicate these attacks on other organizations.
So, no matter what sector you operate in, if you use Microsoft 365, you should keep aware of this threat.
What tactics, techniques, and procedures is Cozy Bear using to compromise Microsoft 365?
Cozy Bear is taking a multi-pronged approach against Microsoft 365, including:
Disabling licenses featuring Purview Audit
Microsoft 365 offers a range of licensing models with different security features. With the E5 license and specific add-ons, organizations receive a feature called “Purview Audit” (formerly Advanced Audit).
With this feature enabled, security administrators receive logs of valuable, granular data streams — including IP addresses, timestamps, and usernames — each time someone accesses an email account. This log source lets organizations quickly see if an account has been accessed suspiciously or unexpectedly.
Cozy Bear, of course, would rather their activity stay hidden from any log sources. As such, the hacker group disables Purview Audit on accounts it targets. Once the feature is disabled, the group begins email collection, with the target none the wiser that they have been compromised because no log information is available.
Solutions like the Azure AD Investigator can prevent attackers from successfully disabling the Purview Audit feature.
Exploiting the self-enrollment process for multi-factor authentication
Multi-factor authentication (MFA) is a valuable identity and access management solution that helps organizations prevent account takeover attacks and validate their users’ identities.
MFA works by requiring users to verify their identity in two ways, such as through a password and a code sent to their mobile phone. However, as Cozy Bear’s second tactic shows, MFA is far from infallible.
We’ve already seen how threat actors use MFA push notifications to pressure end-users into sharing sensitive details. Now, Cozy Bear is exploiting MFA in another way.
For Microsoft 365, MFA typically involves a self-enrollment process, as shown in the image below. In this workflow, organizations enable individual users to set up MFA on their devices.
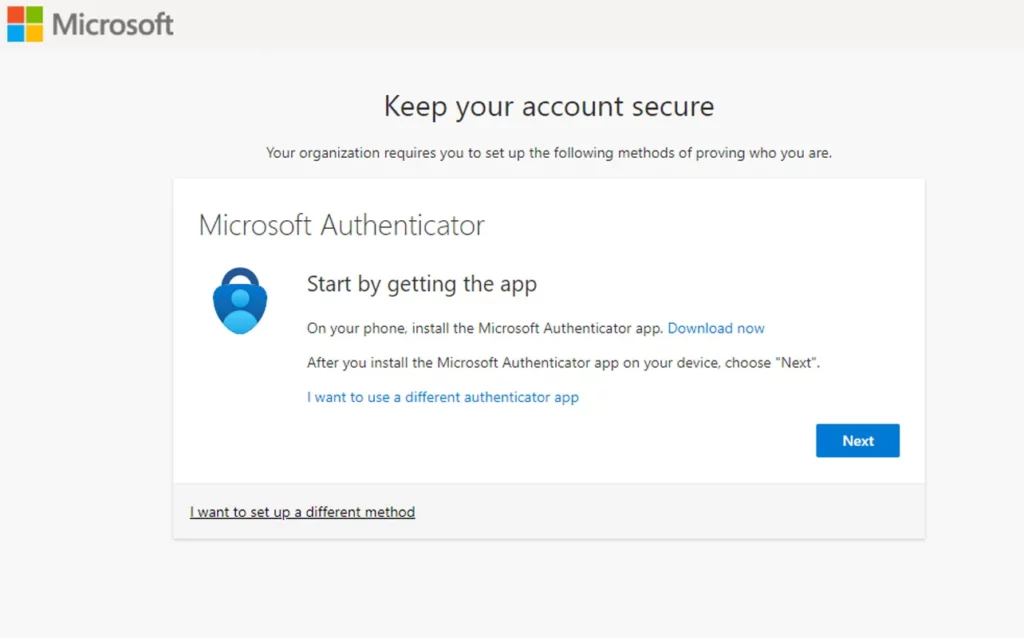
However, Cozy Bear identified a loophole in this system. The MFA enrollment process only requires users to enter their username and password. If a threat actor knew these details before a user had enrolled their device, then they could set up MFA on any device of their choosing and attain access to that user’s account.
In practice, Cozy Bear targets accounts that have been set up but never logged into, meaning MFA is not yet enabled. Using a mixture of brute-force attacks and compromised data, the hacking group guesses passwords to these accounts and then enrolls for MFA.
From there, the group accesses the victim organization’s Virtual Private Network (VPN), where it moves laterally through the network and harvests valuable data.
While this technique is certainly troubling and sophisticated, you can implement some easy fixes, which will prevent this form of compromise. These include:
- Close down all dormant/inactive Microsoft 365 accounts urgently
- Make sure all active accounts already have MFA enabled
- Use the Microsoft feature that places geographical and device restrictions on where users can enroll for MFA
Strategic and stealthy
Cozy Bear is undoubtedly a hacking group that plays the long game. Once they are in a victim’s network, the work only just begins. They stay hidden for as long as possible, evading detection and capturing more data for espionage.
They achieve this through several means. For example, APT29 uses Azure Virtual Machines to obfuscate their IP addresses from those of the victim organizations.
The attackers also cleverly blend legitimate administrative actions with malignant ones. For example, they compromised a global administrator’s account in Azure. From there, they implemented a backdoor to collect the administrator’s emails. At the same time, the actors stealthily introduced a certificate with a Common Name (CN) that corroborated the display name of the backdoor. They also inserted a new application address URL to the service principal.
From an attack perspective, this doesn’t make much sense initially. The address serves no purpose in the attack and doesn’t help Cozy Bear achieve its goals. However, on further analysis, we realize that, through these actions, Cozy Bear has added legitimacy to its movements while in the account.
APT29: The threat isn’t going away
These findings show that APT29 is a highly sophisticated, organized cybercrime group. This campaign is not their first and will certainly not be their last.
Organizations can mitigate the risks of the attacks mentioned above by proactively hardening the Microsoft 365 environment.
Extending security hardening to Microsoft Teams and Microsoft OneDrive
Remember, too, that security hardening must go beyond email security. In the age of cloud applications, threat actors increasingly target well-known services like Microsoft Teams and OneDrive.
Polymer DLP helps you reduce the likelihood of data loss and account compromise in these applications. Powered by a self-learning engine, Polymer DLP automatically discovers, scans and protects data in cloud applications, ensuring that only legitimate, verified users access sensitive data in real-time.
Find out how Polymer DLP can help you.