This week, thousands of schools across the US became embroiled in a mass data leak, after the school safety software company—Raptor Technologies—accidentally left troves of sensitive data exposed on the internet.
What happened with the Raptor Technologies data breach?
On January 11, a cybersecurity researcher unearthed a concerning discovery: an unprotected database housing an estimated four million records. This repository, devoid of password protection, held a trove of sensitive information encompassing school safety records and personally identifiable information (PII) of students, parents, and school personnel.
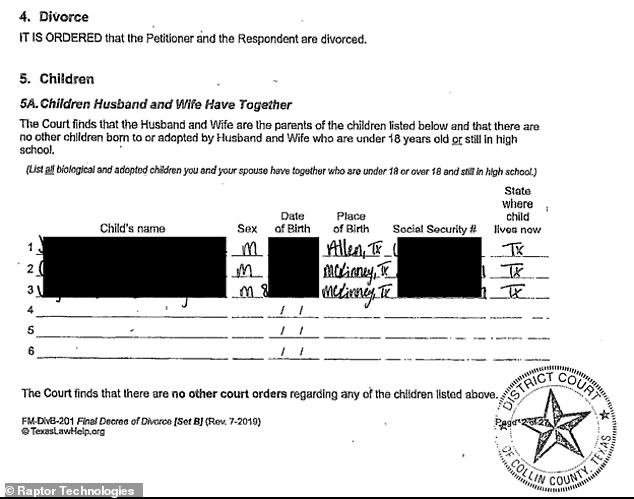
Within three distinct cloud storage buckets, these unprotected school documents unveiled a highly confidential cache. Among the disclosed contents were evacuation plans, complete with detailed maps outlining the routes students are instructed to follow and designated gathering points during emergencies.
The data leak also encompassed critical details about students deemed potentially threatening on campus, comprehensive medical records, court documents pertaining to restraining orders, and instances of family abuse. All this along with the names and identification numbers of both staff, students, parents, and guardians.
Upon deeper investigation, the researcher determined that the exposed documents were linked to Raptor Technologies, which equips schools with software solutions to track student attendance, oversee visitor activities, and manage emergency situations. Their software is trusted by over 5,300 school districts across the United States and utilized by 60,000 schools worldwide.
Upon identifying the source of the security lapse, the researcher promptly initiated a responsible disclosure notice to Raptor Technologies. Acting swiftly, Raptor Technologies took immediate measures to secure the vulnerable database and restricted public access the following day.
Currently, we don’t know how long the database instance was left visible to the public, or whether malicious actors might have accessed it.
David Rogers, Chief Marketing Officer at Raptor Technologies, released a statement to the press stating, “There is no indication at this time that any such data was accessed by third parties beyond the cybersecurity researcher and Raptor Technologies personnel.”
However, only time will tell whether this is truly the case.
What could Raptor Technologies have done differently?
Cloud misconfigurations like this have become commonplace. In fact, Gartner predicts that, by next year, 99% of security failings will be the result of such misconfigurations.
Thankfully, there’s a way to secure your data even in instances where an employee has accidentally left a cloud storage bucket set to “public”—cloud data loss prevention (DLP).
Next-generation cloud DLP tools like Polymer DLP harness the power of natural language processing to autonomously and speedily detect, classify, and protect unstructured sensitive data (PDFs, emails, and word files) in your cloud applications and online databases.
Using contextual authentication policies, these tools ensure that only authorized, legitimate personnel access sensitive documentation, regardless of whether the database is set to ‘public’ or ‘private’.
Should an unknown or unauthorized user attempt to access your sensitive files, Polymer DLP will automatically either redact the sensitive data from the file or block the user’s action altogether, ensuring that inevitable cloud misconfigurations don’t become full-scale data breaches.