Zero trust. You know it’s important. You know you want to implement it in your organization. And you know it could make Slack way more secure – especially given the recent Uber breach! But there’s a problem. Moving from concept to reality is proving mighty difficult. You’re not alone. 96% of security decision-makers state that […]

AstraZeneca breach exposes sensitive patient data
This week, the pharmaceutical giant, AstraZeneca, hit the headlines after security researchers discovered credentials for one of the company’s internal servers on the code sharing platform, GitHub. While this is a relatively small-scale breach, there are a lot of lessons here about the risks of data exfiltration across SaaS environments. Here’s everything you need to […]
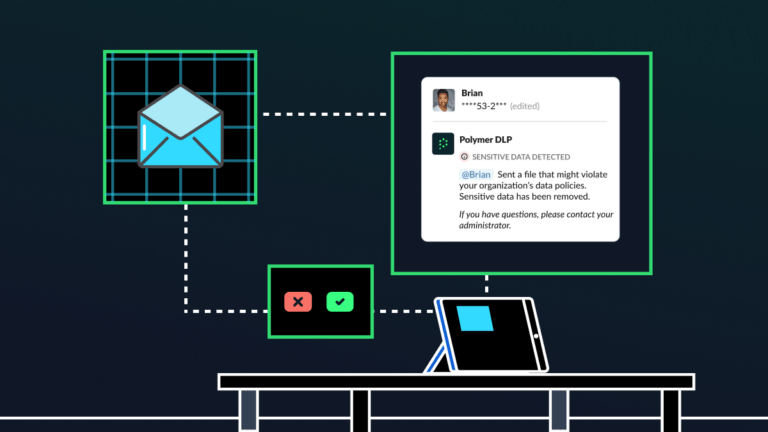
Should your business be worried about Slack security concerns in 2023?
In September 2022, tech giant Uber had to shut down its company Slack channels after a malicious actor sent a Slack message to multiple employees, stating: “I am a hacker.” Yikes! This incident isn’t the first time hackers have leveraged Slack in a cyber-attack, and we’ve got a feeling it certainly won’t be the last. […]

GitHub security risks and best practices you need to know
What software developer doesn’t love GitHub? This amazing—and free—platform is a fantastic way to share code files, connect with fellow developers and collaborate on projects seamlessly. It’s no wonder that the platform has over 32 million monthly users. But, unfortunately, many people aren’t using the platform securely. Just recently, security researchers scanned GitHub for sensitive […]

What is the cost of PII on the dark web in 2022?
How much money do you think a cybercriminal needs to steal your identity on the dark web? $1000? $2000? Maybe less; $800? Actually, the figure is much, much lower. According to recent research, cybercriminals can start purchasing personally identifiable information (PII) for as little as $15. That would buy you a hacked credit card with […]
How NLP can supercharge HIPAA compliance
The Health Insurance Portability and Accountability Act (HIPAA) consists of several rules that HIPAA-covered entities must follow to protect the confidentiality, integrity and availability of protected patient health information (PHI). One such rule, which we will focus on today, is the mandate to “enhance safeguards as needed to limit unnecessary or inappropriate access to and […]
How did Dropbox data breach of 100 GitHub repositories occur?
It looks like Dropbox has dropped the ball. In a blog post published on November 1st, the company revealed that it had suffered a data breach after a successful phishing lure fooled numerous employees. Read on to discover how this breach happened, and the critical learnings to apply to your organization. What’s Dropbox? For those […]

What is shared cybersecurity defense?
Hands up if your organization uses cloud applications like Microsoft 365, Google Workspace, Slack or AWS? If you do, you’re in the majority. It’s estimated that 90% of companies use the cloud. It’s a huge part of the future of work. But the cloud is complex—especially when it comes to security. This is because it […]

What are 5 most common SaaS security mistakes?
All great business leaders are adept at managing and mitigating risks. In the middle of an economic downturn, for example, you probably wouldn’t start increasing your overheads. Or, if you opened an office in an area with high-crime rates, you’d ensure to install CCTV cameras and other physical security measures at all entry points. And […]
6 Step guide to securely off-board employees
Did you know that 40% of ex-employees have admitted to stealing corporate data for their next role? Worse still, it’s estimated that 25% of departed employees still have access to company resources and data. Here’s a hard truth. If any of your employees have left your company with sensitive data downloaded onto their personal devices, […]
Can you afford Cyber Insurance as a small business in 2023?
If you’re looking to renew your cyber insurance for 2023, you may be shocked to find that next year’s cost is much higher than ever before. According to research, cyber insurance costs increased by an astonishing 102% during the first quarter of 2022. As a result of these steep price increases, analysts predict that the […]