Uber has been hacked by an 18 year old. Yep, you read that right. On the 15th September, tens of Uber employees received a Slack message from an unknown identity, stating “I am a hacker.”
But that’s just the tip of the iceberg. The threat actor’s self-announcement was the final step in a lengthy data theft process. According to vx-underground’s Twitter, a provider of malware and other tools, the hacker “completely compromised Uber. They have posted screenshots of their AWS instance, HackerOne administration panel, and more.”
How did this breach happen, and how can you ensure the same doesn’t happen to your company? Let’s find out.
How did the Uber breach happen?
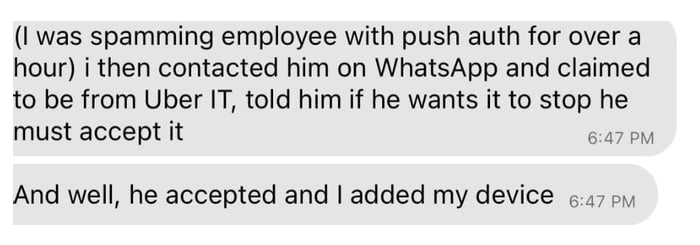
This incident started as many attacks do; with a targeted social engineering scam. The hacker targeted an Uber external contractor, whose username and password he had obtained from the Dark Web. He then tricked the contractor into giving him access to internal systems by harassing them with an onslaught of multi-factor authentication (MFA) push notifications.
Once the victim finally accepted the MFA request, the hacker was able to break into Uber’s network via the internal VPN.
At this point, things get a little complex. A whitehat hacker on Twitter, Carbon Leo, managed to contact the hacker about what he did once in Uber’s network.
The individual shared that Uber had an “internal network share that contained powershell scripts. One of the powershell scripts contained the username and password for an admin user in Thycotic (PAM). Using this I was able to extract secrets for all services: DA, DUO, Onelogin, AWS, GSuite.”
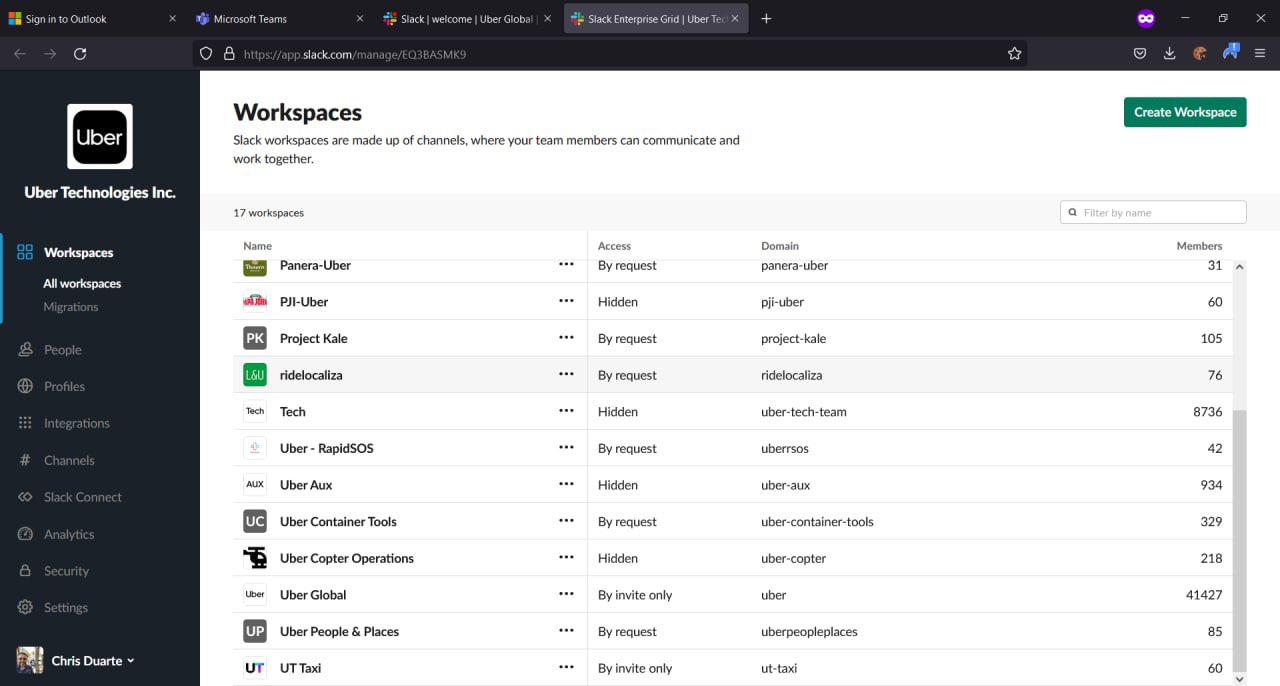
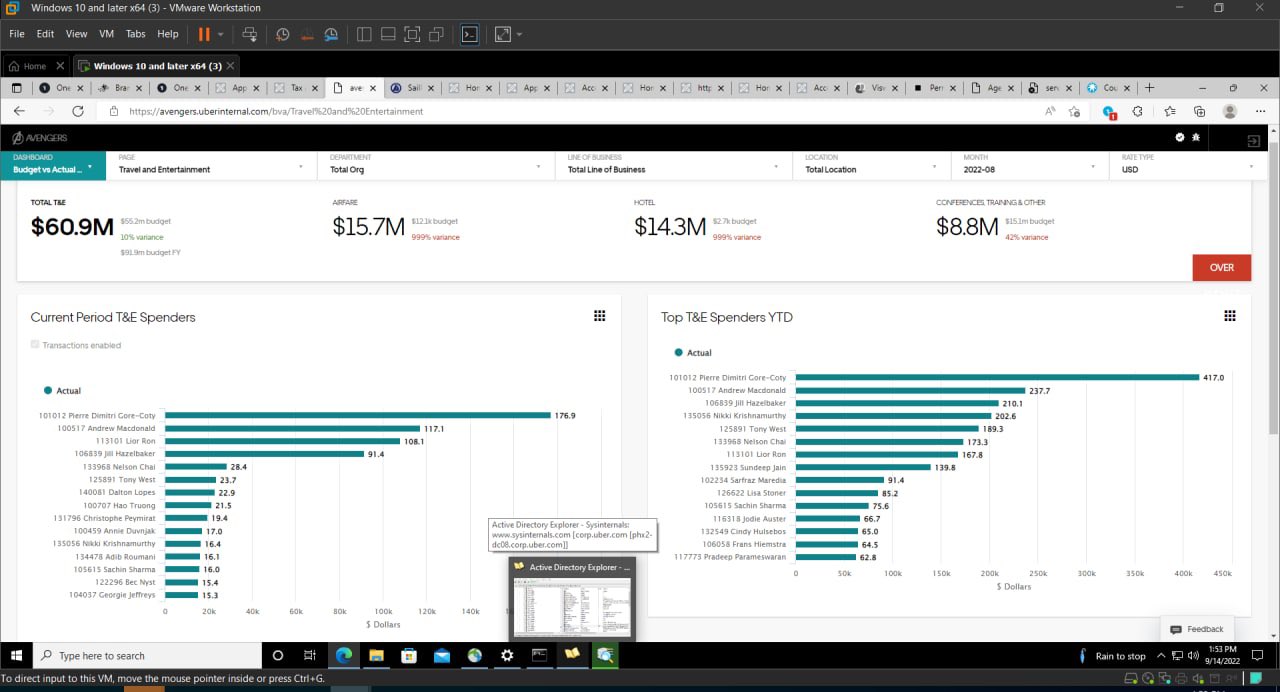
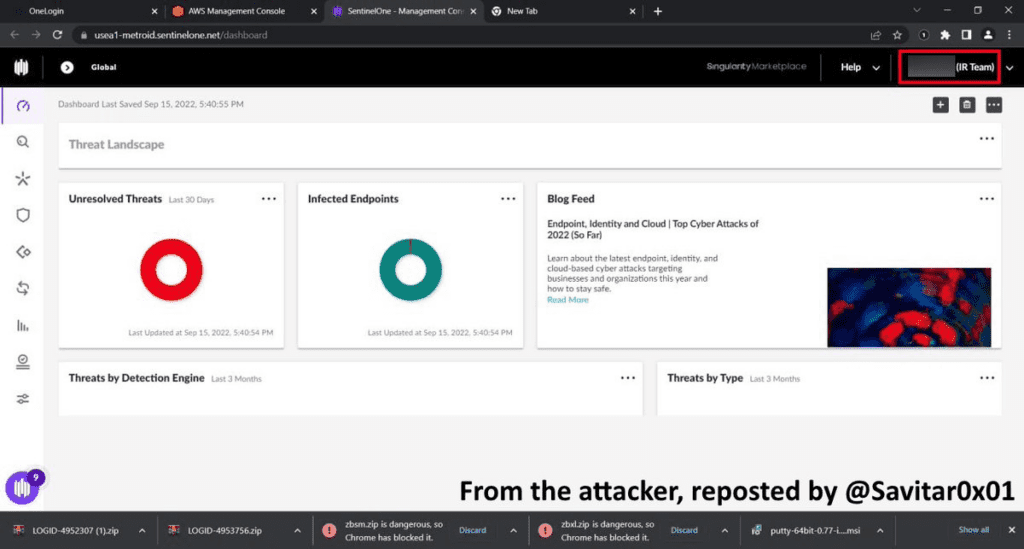
The attacker also shared screenshots of the infrastructure he compromised, as shown below. These screenshots include images of Uber’s IAM portal, showing the attacker has administrative access. They also show a compromised account of an incident response team member – which is very troubling.
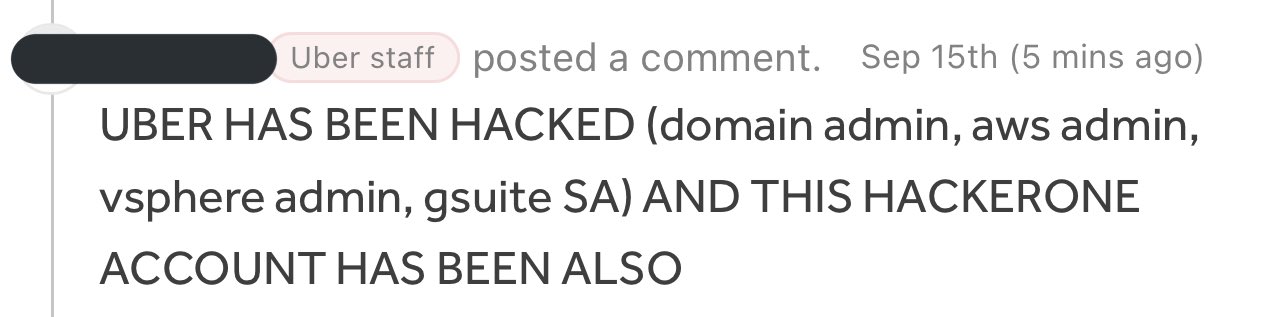
After stealing vast amounts of data—without being caught—the hacker decided to announce his presence on the company Slack, taunting the company about their apparent poor security posture.
What is Uber doing about the breach?
Undoubtedly, it was a long weekend for Uber as they dealt with the ramifications of this breach. The company shut down its internal communications platforms, including Slack, after the incident and released a brief statement on Twitter, saying:
“We are currently responding to a cybersecurity incident. We are in touch with law enforcement and will post additional updates here as they become available.”
A week on, more details are emerging about the breach. Uber has shared that it believes the hacker responsible is affiliated with the cybercrime group Lapsus$, which has hacked high-profile companies like Microsoft, Samsung, Nvidia, Ubisoft, and Okta.
Initially, there were concerns that the cyber-criminal got away with all of Uber’s data, including information like trip history and addresses. However, in a statement released on September 19, Uber said the attacker did not access “the production (i.e. public-facing) systems that power our apps; any user accounts; or the databases we use to store sensitive user information, like credit card numbers, user bank account info, or trip history.”
The attacker did, though, manage to infiltrate the company’s Slack, information from an internal tool the company’s finance team uses for invoicing, and the company’s HackerOne dashboard.
“Any bug reports the attacker was able to access have been remediated,” the company stated in the update.
Moreover, the breach raises concerns about whether other cyber-criminals might have breached Uber’s network undetected. This hacker, it appears, compromised Uber to make a point that the company’s security posture needs some work.
However, other criminals may not be so vocal about their successful breach attempts. It’s possible that Uber is more vulnerable and exposed than it even realizes.
What are the lessons from the Uber breach?
First things first, this breach reinforces the importance of social engineering training. This all started because an employee actively shared their password with the hacker, believing them to be a legitimate person. Training—especially phishing awareness—is crucial to combat threats like these.
In the event that a password is compromised, you should ensure that multi-factor authentication is enabled across your accounts.
On top of this, it’s vital to deploy intelligent data loss prevention (DLP) that uses the zero-trust model like Polymer DLP. It’s no longer enough to base access on people’s static identities. Organizations need to use tools that enable dynamic identity verification at the data level. These tools are the only ones that can halt attackers that manage to break into your network.