Gaming fans got an unexpected treat last weekend when in-development gameplay footage of the upcoming Grand Theft Auto (GTA) game was leaked online. No, this wasn’t an attempt by Rockstar Games—the publisher of GTA— to drum up anticipation for the pending launch.
The company was hacked. And badly. The hacker managed to break into an internal Slack channel, from which they stole 90 videos of the unreleased game and some of the company’s source code. In fact, the group responsible is now trying to extort Rockstar Games into paying them so they don’t release more of the stolen footage.
You’re probably wondering how the leak happened, and who’s responsible? Here’s everything we know so far.
Anatomy of the Rockstar Games breach
Following the breach, the company released a brief statement on Twitter. It shared that:
“We recently suffered a network intrusion in which an unauthorized third party illegally accessed and downloaded confidential information from our systems, including early development footage for the next Grand Theft Auto. At this time, we do not anticipate any disruption to our live game services nor any long-term effect on the development of our ongoing projects.”
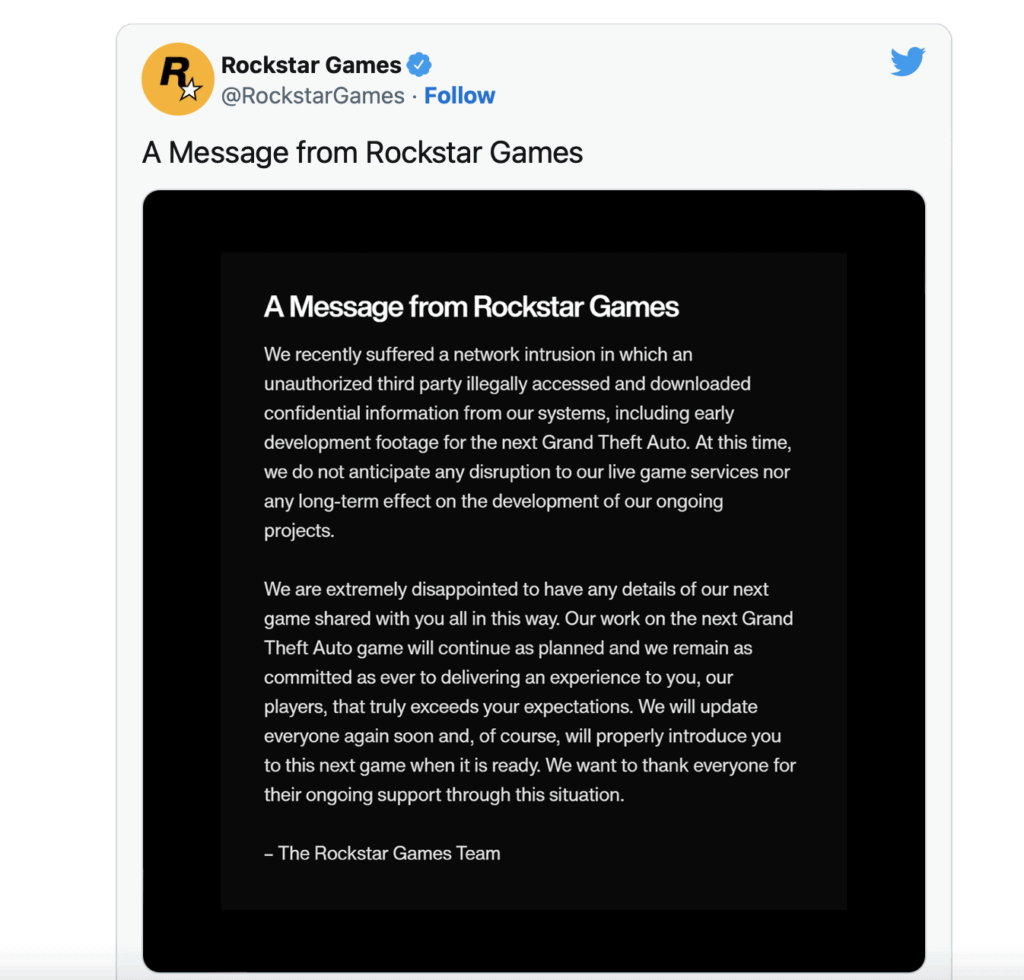
As you’ll see, this statement doesn’t really tell us much—and Rockstar Games hasn’t yet released any more details about how the attacker infiltrated their network.
Enter Uber, which you may remember also suffered a cyber-attack last week. Well, in a statement released September 19, Uber shed more light on the security incident it suffered, and included a shout out to Rockstar Games. The company said:
“We believe that this attacker (or attackers) are affiliated with a hacking group called Lapsus$, which has been increasingly active over the last year or so. There are also reports over the weekend that this same actor breached video game maker Rockstar Games. We are in close coordination with the FBI and U.S. Department of Justice on this matter and will continue to support their efforts.”
This link is crucial. It indicates that the guys behind the Uber breach are also responsible for the Rockstar Games incident, which means it likely involved social engineering
A malware collective on Twitter, vx-underground, confirmed social engineering was involved, stating: the “individual who breached Rockstar Games states they got initial access by social engineering an employee”.
Putting two and two together, it’s very probable that the hacker used social engineering tactics to manipulate a Rockstar Games employee into either sharing their Slack password (if no multi-factor authentication enabled), or to click on an authentication link via text message.
This would have then enabled the criminal to log on from their own device. The latter is exactly what happened in the Uber data breach.
Who’s responsible?
The City of London police announced on Twitter that they arrested a British 17-year-old teen suspected of being responsible for both incidents. While it has been officially confirmed, it’s highly likely the team is part of Lapsus$.
Lessons learned
While it’s great that law enforcement has been quick about these breaches, it’s better to prevent crime than respond it.
The Uber and Rockstar Games data breaches highlight that multi-factor authentication alone isn’t enough to protect organizations from malicious actors. Instead, companies need to move towards a dynamic, zero-trust approach, where employee permissions are continuously authenticated during sessions to ensure they are who they say they are.
In applications like Slack, Teams and Zoom, the best way to adopt zero-trust is through a data loss prevention (DLP) solution like Polymer DLP. Our solution uses artificial intelligence (AI) to protect against insider threats by spotting and responding to suspicious activity in real-time.
For example, suppose a user attempts to download a folder of trade secrets—or a large amount of unreleased video footage—from Slack. In that case, Polymer DLP will block the action and alert the IT team at the same time so they can review the request in more detail.
Rather than being on the back foot and responding to breaches when it’s too late, you can stay one step ahead of malicious actors like Lapsus$.