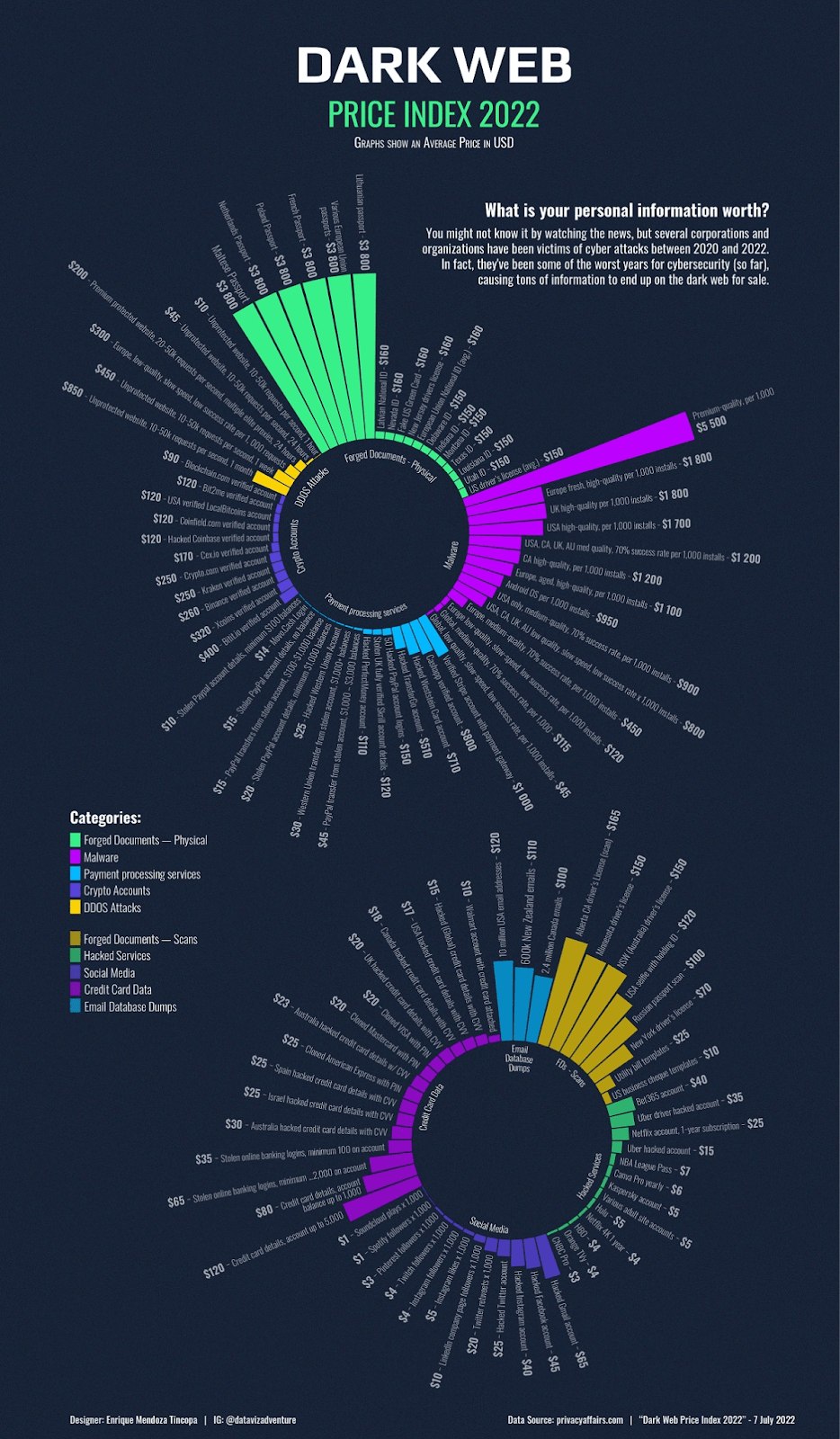
How much money do you think a cybercriminal needs to steal your identity on the dark web? $1000? $2000? Maybe less; $800?
Actually, the figure is much, much lower. According to recent research, cybercriminals can start purchasing personally identifiable information (PII) for as little as $15. That would buy you a hacked credit card with CVV information.
And that’s just the tip of the iceberg. For between $100 and $150, malicious entities can purchase databases with millions of stolen emails, compromised online banking logins, and verified Stripe and PayPal accounts ready to be exploited.
The revelation of how easy and cheap it is to buy stolen data on the dark web should heed warning to businesses. Here’s everything you need to know.
What’s the dark web?
First things first, for any dark web newbies, here’s a quick definition. The dark web is basically the digital underworld; a malevolent realm where individuals can go to purchase illegal weapons and commit nefarious deeds: drugs sales, weapons, hacking tools, fake documents and stolen data can all be found in the dark web’s online marketplaces.
Given the illicit nature of the dark web, it’s in hackers’ best interests to ensure it’s not easy to find for law enforcement. That’s why dark web marketplaces can’t be found on Google or other search engines on the surface web (that’s the web you’re using to read this article!)
Instead, hackers must use a specialist browser – known as Tor – to gain access. Tor, which stands for The Onion Router, connects users to the Dark Web through layers of complex encryption that shadow the user’s IP address and identity, enabling hackers to interact with the dark web completely anonymously.
PII on the dark web: a visual breakdown
To exemplify the range of PII on the Dark Web, designer Enrique Mendoza created an in-depth visual, showcasing the cost of different types of sensitive information up for sale, which you can see below:
Why should organizations be concerned?
For businesses and individuals, the commercialization of PII on the dark web is extremely worrying. When hackers purchase PII, their number one aim is usually fraud or further data theft, which can look like:
- Account takeover fraud: A cybercriminal gains access to a victim’s online accounts, using them to either withdraw money, make purchases or steal sensitive information
- Business email compromise: A sophisticated attack in which a malicious entity takes over the victim’s business email, and begins masquerading as the individual with the aim of redirecting an invoice or payment to their own bank account
- Spear phishing and social engineering: The attacker will use the stolen PII to create eerily realistic and convincing social engineering scams that manipulate a business or individual out of money.
- Ransomware, malware and extortion: Using the sensitive information they have purchased, malicious actors may launch complex attacks once they are able to invade the enterprise network, perhaps launching ransomware or another disruptive form of malware.
This isn’t a theoretical issue either. Just last year alone, online fraud cost the US economy $6.9 billion in 2021— up 64% the year before.
Why the sudden increase? Well, as online data leaks and data theft soar, cybercriminals are sharing more and more PII on the dark web. What was once a lucrative commodity has become pretty commonplace, so malicious sellers have to lower their prices and sell more data to make a living.
Chances are, at least some of you or your employees’ data is on the dark web. Your business is just one sale away from a fraud attempt. When this happens, your level of cyber preparedness will be the difference between a thwarted incident or a successful scam— and all the reputational damage and compliance headaches that come with it.
How Can I Protect My Organization?
Protecting your organization from online fraud requires a two-pronged approach:
- Accept that malicious actors will attempt to breach your organization using stolen PII at some point, and put in place controls to prevent them being successful
- Reduce the possibility of threat actors stealing more PII from inside your network with a layered, zero-trust approach
That’s the strategy at a high-level. Here’s how to implement it step-by-step:
- Mandate that all users and administrators use unique, complex passwords for each of their online accounts to prevent widespread fraud. Back this up with two factor authentication, too.
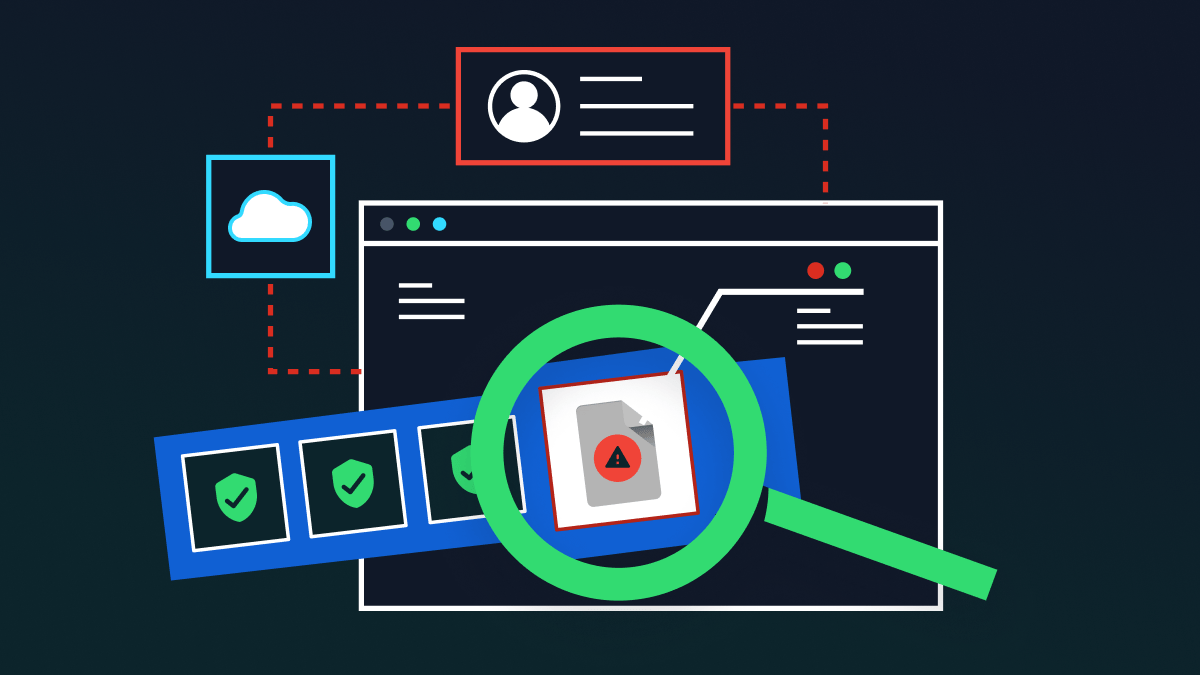
- Implement a data loss prevention solution (DLP), which is a comprehensive suite of technologies that monitor and protect PII as it moves within your infrastructure, cloud applications and servers. In conjunction with data classification policies, DLP remediates threats to sensitive data. For example, if a suspicious or unauthorized user attempts to download a document with PII, DLP will automatically redact the sensitive information in real-time, preventing a data breach.
- Take a zero-trust approach. This is a security framework for preventing breaches, by giving employees and third-parties access to only the information they need to do their jobs, and nothing more. It’s the idea that no one can be trusted when it comes to data security. This approach drastically reduces the likelihood of a data breach through stolen credentials. Forward-thinking DLP solutions incorporate zero-trust principles into their models.
- Audit identities, access and user privileges: Many fraud attempts are successful because hackers manage to break into dormant employee accounts. Combat this by ensuring that, when an employee resigns, you decommission their accounts. To keep track of different roles and privileges, we recommend putting in place a defined auditing system.
Wrapping up
Unfortunately, in today’s digital-first world, our data will probably end up on the dark web at some point or another. Even if your own organization’s security is superb, you and your employees’ will have accounts with many other businesses and platforms. It takes just one breach at one of these companies for data to wind up on the dark web.
Preparing for this eventuality is crucial. PII is becoming incredibly cheap, meaning scam attacks are becoming more attainable for malicious actors all over the world. Don’t bury your head in the sand about dark web risks.
Your best defense is to be proactive; bolster your cybersecurity by investing in data-centric solutions that reduce the likelihood of successful data theft and fraud.
Keep your PII safe with Polymer. Try a complimentary risk scan today.