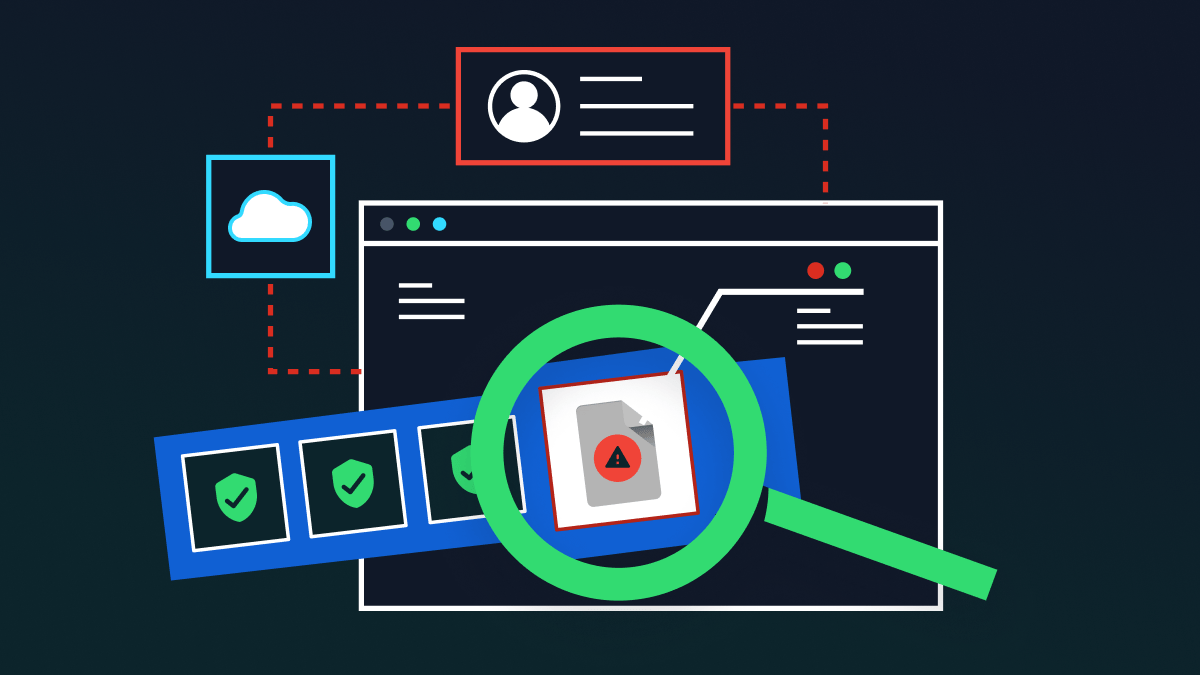
For IT and security leaders, the term ‘shadow IT’ tends to send a shiver down the spine. About ten years ago, it became an epidemic in the corporate world. The consumerization of cloud applications, combined with the rise of bring your own device (BYOD), led to employees downloading non-authorized applications, for work purposes, in their hundreds and thousands.
Over time, firewall rules were not sufficient to protect companies against data exfiltration. Sensitive company data was being downloaded, uploaded, transferred and stored in places the IT team had no idea about. Some of these apps had vulnerabilities, others weren’t configured properly and many more were the target of cyber attacks.
This was the first wave of shadow IT – a costly and risky practice that might be about to make a comeback in its incarnation of shadow IT 2.0.
Shadow IT 1.0 statistics
As noted in our previous article, SaaS platforms carry a whole nest of risks for unwary organizations, and the teams that use them, in the name of efficiency and productivity.
- According to Microsoft, an astonishing 80% of employees use unauthorized apps that no one has reviewed, or fail to comply with security and compliance policies.
- A McAfee survey found that the average organization assumes they use only 30 cloud services, when in reality the number is closer to 2,000.
- Based on the Cost of a Data Breach Report, the global average of the costs incurred in a data breach was $3.86 million in 2020. The figure is higher in the US, where the average loss comes up to $8.19 million.
The rise of PaaS
Thankfully, the original shadow IT outbreak was mostly quashed by evolving security tools. With standardization and the rise of cloud access security brokers (CASBs), it is more difficult for employees to lose – either purposefully or unintentionally – sensitive company data through unauthorized cloud applications.
However, IT leaders can’t breathe a sigh of relief just yet. A new threat is now rising: Shadow IT 2.0, and it stems from PaaS (platforms as a service).
PaaS offers a cloud-based development and deployment environment, enabling developers to build custom applications in the cloud, without the hefty expense of purchasing infrastructure. You can think of PaaS as an online service for building apps – the developers create and manage them, while the cloud service provider manages the underlying storage. Common examples you might know include Heroku and Google App Engine.
PaaS has a range of enterprise benefits: excellent scalability, freedom and – when used correctly – cost efficiency. Because of this, the market is rapidly growing – just look at the stats below.
- According to Forbes, in 2018, 48% of IT budgets went to SaaS, while 30% went to IaaS and 21% to PaaS. Today, investment in the cloud is rising due to remote work caused by the pandemic.
- By 2022, the public cloud PaaS market is forecast to reach almost $60 billion, with the four giants (Microsoft Azure, Amazon Web Services, IBM PaaS, and Google Cloud Platform) accounting for over 50% of the market.
- Gartner estimates that PaaS will grow by nearly 27% this year, beating SaaS’ growth rate.
Shadow IT 2.0: the 2nd wave
While PaaS is a productivity haven for developers, its potential to impact data security is troublesome. If left unchecked, this growing market could lead to a new, more aggressive wave of shadow IT.
The first wave of shadow IT came about because employees felt empowered to download and experiment with unsanctioned applications that the IT didn’t know about. The same exact thing could happen with PaaS services.
These platforms mean that developers no longer need the IT team to progress with servers and virtual machines. They can autonomously source infrastructure as needed and build what they want to. If the IT team isn’t in the know on each and every service being used, this practice becomes a data security nightmare.
Developers are notoriously known for working at a fast-pace. Rapid scaling and automation are a huge risk for vulnerabilities, cloud misconfigurations and security issues relating to APIs, credentials sharing and SSH keys. Every virtual machine created needs to be registered and managed by the IT team. But, right now, it’s unlikely this is happening.
For security and compliance, the threat is huge. Unauthorized applications are a key violation in regulations like HIPAA and GDPR. They make security audits obsolete and indicate a lack of control and visibility over data security.
This problem has snowballed over the last year. For one, in the remote working world, developers are not physically in the same building as the IT team. They are less likely to speak with each other, and are outside the traditional security perimeter.
Furthermore, remote working in itself has set a precedent for fast-paced innovation. To be productive, employees need new tools and they need them fast. On one side of the coin, it is useful that PasS can facilitate this. On the other hand, when security is an afterthought, a nasty data breach could occur.
Keeping shadow IT v2 in check
PaaS is a looming threat for organizations everywhere. But the shadow IT problem doesn’t need to become as big as it was last time. The solutions already exist to stop this issue before it leads to a breach. IT and security teams need to be proactive. Here’s how:
- A culture of collaboration: Communication between IT and DevOps teams can go a long way to make PaaS more secure. By collaborating early on in the development process, IT teams can address security risks on the macro and micro code levels.
- Invest in a CASB: Cloud access security brokers (CASBs) were a hero during the first wave of shadow IT, and their data protection powers can extend to PaaS. These solutions combine a variety of security services – including user authorization, data loss prevention and cloud configuration audits – to enhance the IT team’s visibility and control over how data is being stored and where. If you’d like help with choosing a CASB, read our guide.
- Embrace automation: Another tool to consider is application security testing (AST). This can be used in tandem with automation testing processes to find vulnerabilities, without hindering the speed of development.
As more and more organizations embrace the cloud, we will see more developers turn to PasS for cloud-native development. To prevent another wave of Shadow IT, it’s imperative that IT and security teams adopt advanced cloud security tools that keep up with the pace of change.