Until a few months ago, the international information security standard, ISO 27001, hadn’t been updated for over a decade.
In February of this year, that all changed. A new iteration of ISO 27002 was published, meaning we can expect an updated version of ISO 27001 later this year.
Below, we’ll give you some background on ISO 27001 and ISO 27002 and the critical updates you need to know.
What are the ISO 27001 and 27002 standards?
ISO 27001 is an international standard for information security, designed to help organizations protect their data by creating an Information Security Management System (“ISMS”).
The ISMS empowers businesses to identify, analyze, manage and mitigate the potential risks to their corporate data.
Organizations can achieve certification to ISO 27001 as a means of assuring customers, prospects and partners that their data security controls reach an internationally-recognized level.
Often, ISO 27001 can help companies to boost their credibility and reputation. However, achieving the standard is far from a walk in the park. It takes time, dedication and resources to implement the necessary controls – but the resultant levels of security are worth the effort.
ISO 27001 is part of a broader family of information security standards, one of which is ISO 27002. ISO 27002 is a document of supporting guidelines that should be used to assist with implementing ISO 27001.
What is the difference between ISO 27001 and ISO 27002?
The two are part of the same overarching standard. The significant difference is that ISO 27001 is a standard you can certify to.
You can’t certify to ISO 27002. It’s a supporting document. ISO 27001 is the focal standard, while ISO 27002 offers guidance and best practices for achieving ISO 27001.
What’s new in the ISO 27000 family?
As briefly mentioned, the ISO body released an updated version of ISO 27002 in February of this year. In line with this release, we can expect a newer version of ISO 27001 to come out later this year. It’s rumored that the overarching standard will stay the same, bar a new version of Annex A in line with the controls in the new ISO 27002.
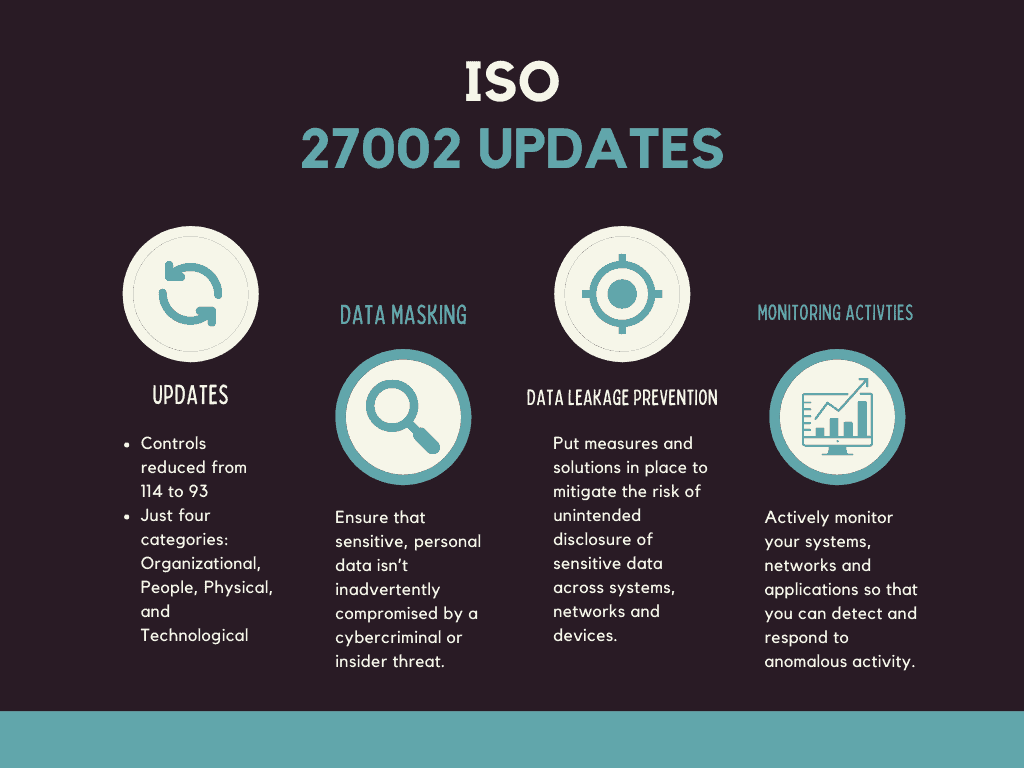
The major changes can be summarized as follows:
- Where previously ISO 27002 set out fourteen control domains, the new version sets out just four categories. These are Organizational, People, Physical, and Technological.
- The number of controls has been reduced from 114 to 93.
- While there are fewer controls, no old controls have been excluded. Instead, they’ve been condensed and updated to make them appropriate for the security landscape in 2022.
- Eleven new controls have also been added to ISO 27002. These are:
- Threat intelligence
- Information security for the use of cloud services
- ICT readiness for business continuity
- Physical security monitoring
- Configuration management
- Information deletion
- Data masking
- Data leakage prevention
- Monitoring activities
- Web filtering
- Secure coding
What does this mean from a data security perspective?
As you can see, the new version of ISO 27002 has shifted focus from a perimeter approach to information security management towards data-centric security.
For organizations that have certified to the standard, or are considering certification, you will need to update your approach. Moreover, even if you’re not planning to certify to ISO 27001, it’s well worth reviewing and implementing the suggested controls as they are industry best practices.
With that in mind, three controls stood out to us in the 2022 update that we’ll explore in more detail below.
At a high level, these are:
- A.8.11 Data masking: The practice of obfuscating data, via techniques like anonymization and pseudonymization to improve your data protection.
- A.8.12 Data leakage prevention: Applying protocols and solutions to prevent sensitive data leakage.
- A.8.16 Monitoring activities: Monitoring applications, systems and networks in order to discover, and respond to, anomalous activity.
Data masking
What is it?
If your organization must comply with regulations like the GDPR or CCPA, then you’re probably already familiar with data masking. Within ISO 27002, data masking is combined with access control to ensure that sensitive, personal data isn’t inadvertently compromised by a cybercriminal or insider threat.
The most common techniques for data masking are pseudonymization, anonymization, encryption and obfuscation. Here is how each of these works:
Pseudonymization: Replacing information that could be used for identification with a pseudonym, so the individual cannot be identified without the use of additional information.
Anonymization: Altering personal data so that it is no longer identifiable.
Encryption: Encoding data so that it can only be accessed by those granted with the correct key.
Obfuscation: Scrambling sensitive data so that it is impossible to understand to unauthorized users while still being of value to those intended to access it.
What tools do I need?
In order to mask your sensitive data, you first need to ensure you know where it is. This is increasingly difficult in the cloud-first world, where sensitive data is often unstructured, making it challenging to discover.
To that end, you should start with data mapping, which we have written about extensively here. We advise against manual data mapping. Instead, look for a data security solution that automates the process of data discovery, classification and masking for you.
At first, you will need to give your solution some guidance over what data should be masked, and who has what access rights. After that, the best-in-breed of these solutions will use machine learning to automate the process for you.
Our solution, for example, enables real-time detection and redaction of sensitive material such as PII, HIPAA-protected health information, and regulated financial information in popular collaboration tools like Slack, Zendesk, Zoom, Github and more.
Using cloud-hosted machine learning, it identifies sensitive data in mid-transfer and masks that data, either via encryption or hashing, to prevent unauthorized users from accessing it.
What else should I consider?
From an ISO 27000 documentation standpoint, we’d advise documenting your data masking rules and access rights in your Information Classification Policy, Access Control Policy and Secure Development Policy.
Data leakage prevention
What is it?
Data leakage prevention is a control focused on putting measures and solutions in place to mitigate the risk of unintended disclosure of sensitive data across systems, networks and devices. The control also aims to help organizations quickly discover and remediate data leakage incidents before they result in a breach or theft.
What tools do I need?
Data loss prevention solutions are the best way to defend against data leakage. However, not all solutions are created equal. Legacy DLP solutions can prevent sensitive information leakage from on premise and legacy structures but don’t have the capabilities to extend into the cloud.
Moreover, many lessor DLP solutions are infamous for generating false positives, adding complexity, labor costs and uncertainty to data leakage prevention.
Newer solutions utilize automation and APIs to extend data leakage prevention to the cloud. It works by monitoring personal data as it moves through the organization’s infrastructure, including endpoints and cloud-based applications. This dramatically reduces the risk of data loss, theft or exposure while increasing enterprise visibility.
What else should I consider?
Data leakage is just as much a people issue as a technology issue. Insider threats–employees who unintentionally leak data–are responsible for 60% of data breaches.
To that end, you should complement your digital approach with security awareness, with the aim of building a culture where people are conscious of data leakage and actively try to avoid it.
While security training away days have a negligible long-term impact, on-the-go nudge training is an excellent way to improve security awareness.
You may also want to update these documents with your DLP rules: Information Classification Policy, Security Operating Procedures and Policy on Acceptable Use.
Monitoring activities
What is it?
This control is about actively monitoring your systems, networks and applications so that you can detect and respond to anomalous activity, such as an employee logging on at an odd time of night or an IT administrator attempting to download a suspicious amount of data.
We’re in the age of the Dark Web and credentials compromise. Often, unusual behavior could indicate a hacker in your systems or even a malicious insider attempting to thwart company policies.
What tools do I need?
User and Entity Behavior Analytics (UEBA) are one way to monitor user behavior for signs of compromise. However, these tools can leave IT teams one step behind without automatic remediation powers.
So, look for a DLP solution that is embedded with UEBA for real-time monitoring and auto-remediation of sensitive data. Our solution uses employee-based risk scoring, based on machine learning analysis of data usage patterns. It then triages anomalous or risky behavior as it happens to prevent a breach.
Utilizing Cloud DLP like Polymer DLP is a key step to implement a zero-trust approach across your IT infrastructure.
What else should I consider?
Your employees should be made aware of monitoring activities, alongside expectations of their behavior regarding data security.
For audit and legal purposes, ensure to keep logs of monitoring activities.









