In the world of cybersecurity threats, you’ve probably heard the terms’ data leak’ and ‘data breach’ used interchangeably. While these incidents have some things in common, they are two very different terms.
To effectively protect your data, you need to know the risks it faces; this means having a thorough understanding of data leaks and data breaches. So, let’s dive in.
Quick-fire definitions
Data leak: A data leak occurs from the inside out. It happens when an employee or partner exposes data to unauthorized recipients. They can do this accidentally or deliberately. The most famous example of an intentional leak is probably Edward Snowden, who exposed highly classified information about numerous global surveillance programs in 2013.
On the accidental side, we can look at the wave of exposed Amazon S3 buckets frequently caught by security researchers. These data leaks occur to cloud misconfigurations or poor security controls instead of being the work of a malicious insider.
The tricky thing about data leaks is that, when data is left exposed on the internet for a long time, we don’t know who might have seen it, downloaded it or tampered with it. Indeed, a data leak can foreshadow a data breach, should a malicious actor get their hands on an exposed database or system.
Data breach: By contrast, a data breach occurs from the outside in. It happens when an external attacker infiltrates your company to steal sensitive data or launch an attack. Data breaches are a costly expense that can negatively impact a company’s reputation, finances, and customer loyalty. According to IBM, the average cost of a data breach in 2021 was a staggering USD 4.24 million.
Most data breaches are caused by hacking or malware attacks. Other standard attack methods include phishing, DDOS attacks and credentials compromise.
What’s the difference between a data leak and a data breach?
At a high level, we can see the data leaks occur from the inside out while data breaches occur from the outside in. While data leaks are due to insider actions, data breaches happen because of cybercriminals’ efforts to compromise company infrastructure.
Another difference between the two is the levels of exposure. When a data leak occurs, it’s often impossible to know how long the data has been exposed for and who has accessed it. On the other hand, with a data breach, you can be sure that your company data has been compromised–and might even be up for sale on the dark web.
What causes data leaks?
Data leaks can happen for several reasons. Here are some of the most common causes:
- Misconfigurations: Gartner predicts that by 2025, 99% of cloud failures will be caused by human error. In the cloud-first world, a simple click of a button can leave troves of data vulnerably exposed on the internet. The rise of remote work has likely worsened this risk. With more and more employees using cloud tools to collaborate, there are an infinite number of ways that sensitive data could accidentally leak into the wider digital world. No company is exempt from this risk either. In 2020, Microsoft accidentally exposed the data of nearly 250 million Microsoft customers after a database misconfiguration.
- Developer errors: Behind every website and computer program lies a human developer. Without getting too philosophical, humans are inherently flawed. This means that people make mistakes and, sometimes, your employees will make mistakes with the software and systems they create and manage. In doing so, they may accidentally expose sensitive data. As an example, we can look to the Danish government’s tax portal. The portal experienced a software error, exposing over 1 million Danish citizens’ tax ID numbers.
- Employees, partners and contractors: In the same vein, a data leak can occur when an employee accidentally sends an email to the wrong person. This kind of threat is pervasive, known as the accidental insider threat. In fact, Forrester predicts that insider incidents caused 33% of data breaches in 2021. On the flip-side, there are those employees like Snowden who leak data intentionally. These employees are what’s known as whistleblowers. They set out to reveal data. Their motivations can vary widely: from political to financial to ethical.
What causes data breaches?
Data breaches can also happen for numerous reasons. Here are some of the most frequent causes:
- Malware: Malware refers broadly to malicious software. A malware attack aims to harm or exploit a user device or company network. Common types of malware include viruses, worms, trojans, and ransomware. Cybercriminals typically use malware to steal sensitive data. This data can then be used directly for financial gain or held for ransom.
- Social engineering: It’s estimated that 98% of today’s cyberattacks start with a social engineering ploy. Social engineering attacks like phishing, SMSIshing and whaling see an attacker send a fraudulent email or text to their victim, pretending to be a colleague, supplier or trusted brand. The email will either contain a malicious attachment riddled with malware or a link to a phoney website that asks the victim to enter sensitive details.
- Hacking: Hacking encompasses a huge variety of attack tactics that cybercriminals use to breach company infrastructure. SQL injections, DDoS attacks and man-in-the-middle attacks are all approaches used by attackers to breach company networks and steal sensitive data.
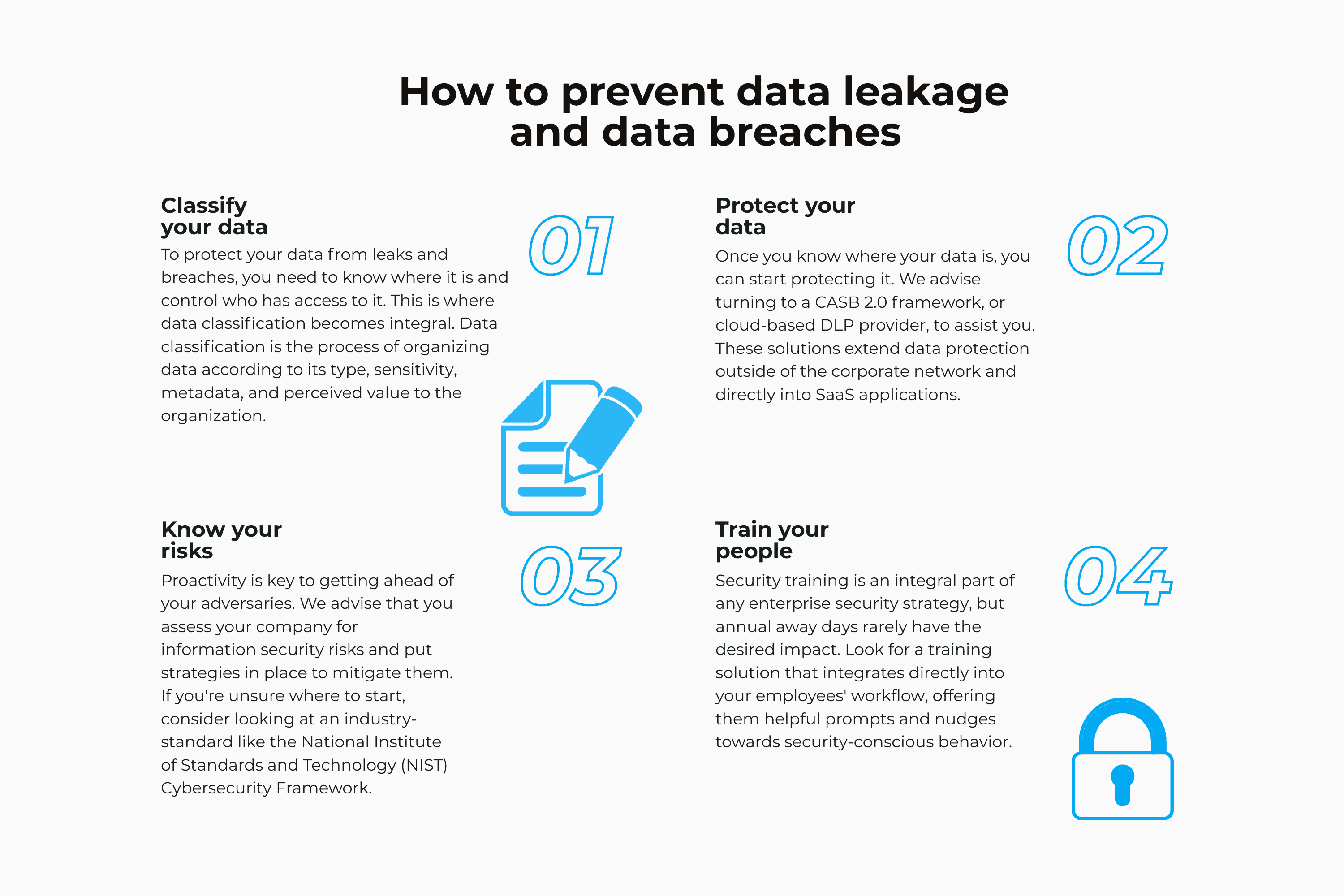
How to prevent data leakage and data breaches
The causes of data leakage and data breaches are multi-fold. So, your defense strategy needs to be multi-layered too. No one solution will thoroughly protect your company from the myriad of threats out there. You need to take a holistic, data-centric approach to security. Here’s how:
- Classify your data
To protect your data from leaks and breaches, you need to know where it is and control who has access to it. This is where data classification becomes integral. Data classification is the process of organizing data according to its type, sensitivity, metadata, and perceived value to the organization. A good data classification strategy is the foundation of data security, helping you implement data access controls, develop data protection policies, and improve visibility and control.
It’s worth noting that, in the age of the cloud, finding and classifying sensitive data isn’t as simple as it once was. Chances are, your information is strung across your collaboration tools and cloud applications. It’s unstructured and harder to detect. The good news is that there are solutions out there that are designed to identify, classify and protect data in the cloud, known as CASB 2.0s.
2. Protect your most sensitive data
Once you know where your data is, you can start protecting it. We advise turning to a CASB 2.0 framework, or cloud-based DLP provider, to assist you. These solutions extend data protection outside of the corporate network and directly into SaaS applications, giving you much needed control and visibility over how data is being used and stored–no matter where it travels.
As well as utilizing DLP, it would be best to incorporate identity and access management policies based on the principle of zero trust. Lastly, we advise that you put in place strict guidelines and auditing measurements to avoid cloud misconfigurations.
3. Know your risks
Proactivity is key to getting ahead of your adversaries. We advise that you assess your company for information security risks and put strategies in place to mitigate them. If you’re unsure where to start, consider looking at an industry-standard like the National Institute of Standards and Technology (NIST) Cybersecurity Framework.
4. Train your people
Security training is an integral part of any enterprise security strategy, but annual away days rarely have the desired impact. Look for a training solution that integrates directly into your employees’ workflow, offering them helpful prompts and nudges towards security-conscious behavior.
Ultimately, while the causes of data breaches and data leaks vary, the impact can be the same: sensitive data loss, compliance fines and a loss of brand equity. To protect against both risks, focus on creating a security strategy that is centered around safeguarding data anytime and anywhere.
Polymer protects against data loss (DLP) on modern collaboration tools like Slack, Dropbox, Zoom, Github and more with alerting & real-time redaction of sensitive and regulated information such as PII, PHI, financial and security data