Colonial Pipeline was hacked recently.
The cyberattack that forced the United States’ largest gasoline pipeline shutdown has triggered fresh questions about the vulnerability of the country’s vital infrastructure and businesses at large to cybercriminals.
The breach at Alpharetta, Ga.-based company, is the latest high-profile cyberattack reminder that many of the nation’s businesses aren’t prepared to deal with threats posed by malicious data breaches.
In fact, a study commissioned by Hiscox found that 7 out of 10 American companies are not ready for a cyberattack.
What follows is a rundown of how a criminal gang code-named DarkSide managed to penetrate Colonial’s infrastructure, and the strategy they used – ransomware – is such a persistent threat.
Colonial Pipeline ransomware attack: The possibilities
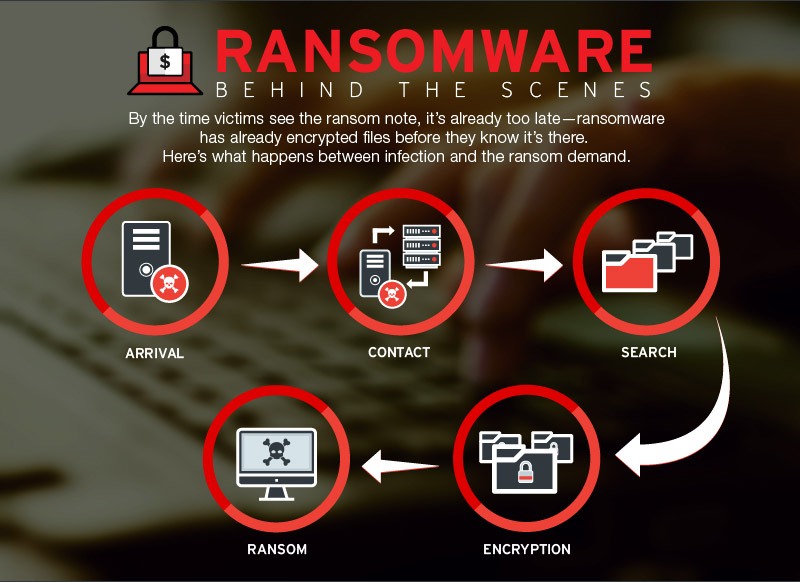
Colonial Pipeline announced that hackers had infiltrated its computer systems with ransomware – malicious code used to seize computers and extract payments from victims.
The breach pounced on Colonial’s business network, which is used for processes such as reporting data to regulators and managing payrolls.
While the initial attack vector remains unknown, there’s every possibility that an old, most likely unpatched vulnerability in Colonial’s system triggered the event. Other possibilities include:
- A phishing email that successfully fooled an employee including:
- Malicious Google Drive links containing an LNK downloader
- Dropbox links with Zip archives that downloaded the backdoor.
- Brute force password attack
- Insider threat
- An SQL injection vulnerability against Colonial’s Virtual Private Network (VPN) infrastructure
There are three unique sets of tactics, techniques, and procedures (TTP) that DarkSide could have used to take control of the company’s systems. Generally, cybercriminals create persistence in computers and networks through:
- Command and control (CS) infrastructure
- Using a backdoor that can execute.NET commands, takes screenshots, and supports keylogging.
- Downloading and using TeamViewer
Installing ransomware into Colonial’s systems
Upon gaining access, the attackers check the operating system language and install the malware. At this point, they have administrative and privileged access.
They then proceed to use CertUtil.exe and PowerShell.exe files to download and execute the DarkSide code. The attackers will also save a copy of the malware to the hacked device.
Further, the criminals escalate privileges by installing the malware, thereby gaining complete autonomy over the Colonial’s infrastructure. They can achieve this using:
- Mimikatz – An application used to harvest credentials
- Vulnerability operating on a Netlogon Remote Protocol, in this case, the CVE-2020-1472. That way, they can run applications on devices in the network.
- Local Security Authority Subsystem Service (LSASS) process memory dumps. These are memory files carrying domain, passwords, and usernames.
Encrypting files & exfiltrating data
With the malicious code already downloaded and access gained, it is time for cybercriminals to start collecting sensitive data and files. DarkSide made away with 100 gigabytes of data.
Having collected the information they want to hold for ransom, the criminals start to encrypt data using ransomware copy in the shared folder on the first device. That way, they can create a scheduled task to spread the fraudulent code throughout its systems.
The DarkSide code also stops and deletes processes that the organization may need to use.
It is important to mention that the DarkSide gang targeted Colonial’s business side. That means the attack was money-oriented and wasn’t intended to send the pipeline crashing down.
Colonial Pipeline paid a staggering $5 million to Eastern European hackers, according to Bloomberg.
Colonial Pipeline attack was likely phishing email-related
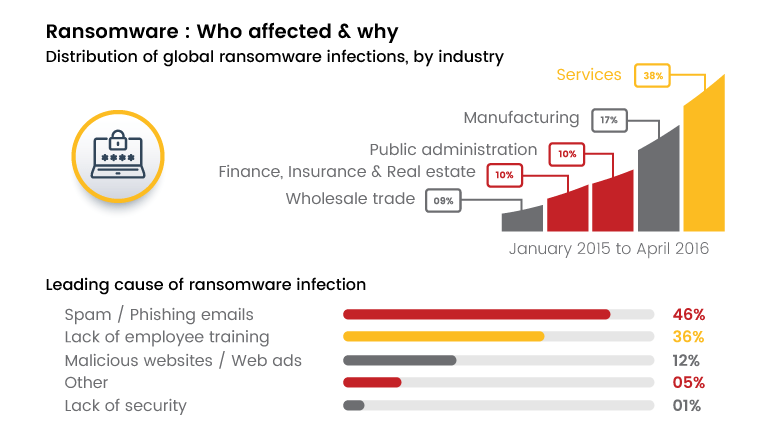
Sure, there are many theories of how the Colonial Pipeline data breach happened – and all could be true. However, we firmly believe that a phishing email was the most likely culprit.
The U.S. Cybersecurity and Infrastructure Agency (CISA) tied the DarkSide gang to other phishing-related attacks dating as far back as 2019. In all the incidents, the criminals used phishing emails to deliver ransomware to their targets.
Also, the cybercriminals were remote (based in Eastern Europe, according to multiple reports), which makes the use of document malware even more probable.
Besides, email is a universal communication tool that binds together the entire industry. And, with the ability to hijack a legitimate account, cybercriminals, and send an email originating from a legitimate domain known to the recipient.
In addition, phishing emails delivered through malicious macros in spreadsheets and documents were responsible for other recent high-profile attacks.
- In February 2020, the U.S. Department of Homeland security reported that a natural gas facility came crashing following an attack originating from an email containing a malicious link.
- In February 2021, SolarWinds reported that hackers compromised its email account and programmatically accessed its personnel in technical roles and business.
How can you protect your organization against ransomware?
The fact that a high-profile company such as Colonial Pipeline can fall victim to cybercriminals means every organization should work to protect itself against ransomware.
Cybercriminals such as DarkSide continue to evolve by day, which means the time to safeguard your business against document malware using Polymer is now.
Polymer is a data governance solution that monitors and secures sensitive information exchanged on tools such as Dropbox, Slack, GitHub, Zendesk, Teams, and more.
The solution allows you to tame the risk associated with files distributed across collaboration tools while ensuring that your systems run smoothly.