Atlassian Confluence vulnerability
On August 25th, Atlassian released a statement warning about the critical remote code execution vulnerability (CVE-2021-26084).
According to the company, the vulnerability affected the Confluence server and Confluence data center.
What is the CVE-2021-26084 vulnerability?
The vulnerability involves an Object-Graph Navigation Language (OGNL) injection flaw on Atlassian’s Confluence server and data center software.
For starters, OGNL refers to a scripting language that enables Java code interaction. Most Confluence software uses the OGNL technology.
The software is typically installed on Confluence self-hosted project management, team collaboration platforms, and wiki.
What is the impact of the Confluence vulnerability?
The CVE-2021-26084 vulnerability allows cybercriminals and hackers to execute a remote code on Atlassian’s Confluence server and data center.
The ripple effect is that the vulnerability rated 9.8 on the CVSS scale, enables unauthenticated or non-administrator to remotely access vulnerable end-point team collaboration platforms.
Why is this vulnerability an urgent item to fix?
First, the CVE-2021-26084 vulnerability is easy to exploit. If successful, it can enforce a command on the targeted server.
According to Atlassian, an attacker would normally have to be logged into the network to exploit it. However, with this Confluence vulnerability, a cybercriminal can remotely exploit services without any authentication.
Essentially this means that cybercriminals can use commands to download software such as web shells. Attackers can also launch a malicious program on the exploited server.
In fact, the US Cyber Command has issued a warning to businesses and organizations using Atlassian Confluence to brace for widespread exploitation.
True to this warning, cybersecurity companies started to report that attackers were actively scanning and exploiting compromised servers soon after Atlassian announced the CVE-2021-26084 vulnerability.
For instance, Tiago Henriques, Coalition Director of Engineering, detected penetration testers trying to locate vulnerable Confluence servers, most probably for bug bounties.
Bad Packet, a cybersecurity intelligence firm, on the other hand, detected even more appalling activity. Threat actors from various countries were exploiting servers to download and run Linux shell scripts and PowerShell.
According to Bad Packets, the actors were striving to install crypto miners on Linux Confluence and Windows services.
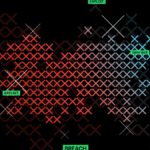
A perfect example is this attacker using the scripts shown in the image below to install XMRig cryptocurrency miner for Monero.
Even though attackers are currently exploiting the CVE-2021-26084 vulnerability for cryptocurrency mining, it doesn’t mean they cannot use it for more advanced attacks, more so for on-premise Confluence servers.
Some possible attacks that can spread throughout an entire network include data breaches and ransomware attacks.
Confluence is a popular and widely used collaboration software which means that CVE-2021-26084 is an extremely potent vulnerability. It is expected therefore, threat actors will continue to execute attacks in the coming days.
What should you do?
Atlassian has already patched the CVE-2021-26084 vulnerability. To safeguard your organization against potential attacks, we highly recommend that you start by identifying vulnerable Confluence installations.
Next, you’ll need to upgrade them to the latest long-term support release as soon as possible. On top of that, we advise that you enable signatures for CVE-2021-26084 in your security controls.