In a hyper-connected world, individual data footprints can be found everywhere. Each day, millions of people share information like email addresses, banking details and telephone numbers across applications and web browsers.
This type of information is known as personally identifiable information (PII), and there’s a 100% chance your organization processes it – either via customers, employees, or both.
But what exactly counts as PII and why is it important to keep it safe? And more importantly, how do you protect it? Let’s take a look below.
Definition
Put simply, PII refers to any data or information that can be used to identify an individual. This can be basic information like:
- Physical addresses
- IDs
- Social Security numbers
- Contact numbers
- Email addresses
In places like the European Union (EU), it can also extend to “quasi-identifiers”, such as digital traces that can be used to identify individuals, including:
- IP addresses
- Mac address
- Device IDs
- Login credentials
- Geolocation data
In the US, the National Institute of Standards and Technology (NIST) divides PII into two categories: linked and linkable information.
Linked information can be directly used to distinguish an individual, while a piece of linkable information – on its own – may not be enough to identify someone. However, when used in conjunction with another piece of information, it can be used for identification.
Why Is it important to protect PII?
PII is extremely lucrative. Armed with it, malicious actors can carry out all kinds of illegal activities: from targeted phishing scams based on people’s email addresses and contact numbers, to fraudulent bank withdrawals, to unlawfully selling data to third parties. In fact, obtaining PII is one of the most common motivations for cyberattacks.
However, as outlined by NIST, breaches that involve PII are not just harmful to consumers, they are hazardous for business too.
With the rise of data privacy regulations across the globe, businesses who fail to protect PII risk legal consequences; the cost of remediation, fines and settlement; and loss of brand prestige and public trust.
One infamous example is the Cambridge Analytica scandal of 2018. The company harvested the PII of 50 million Facebook users using a popular personality quiz, which promised it would not collect personal information – even though it did. This data was then illegally sold to a third-party political consulting firm. The breach cost Facebook $3 billion in legal expenses, and it saw a 50% slump in Q1 2019 profits year-on-year.
What are the laws regarding PII?
Across the globe, regulatory bodies have recognized the danger of misused, lost or stolen PII, and put in place numerous laws that require organizations to protect it.
United States:
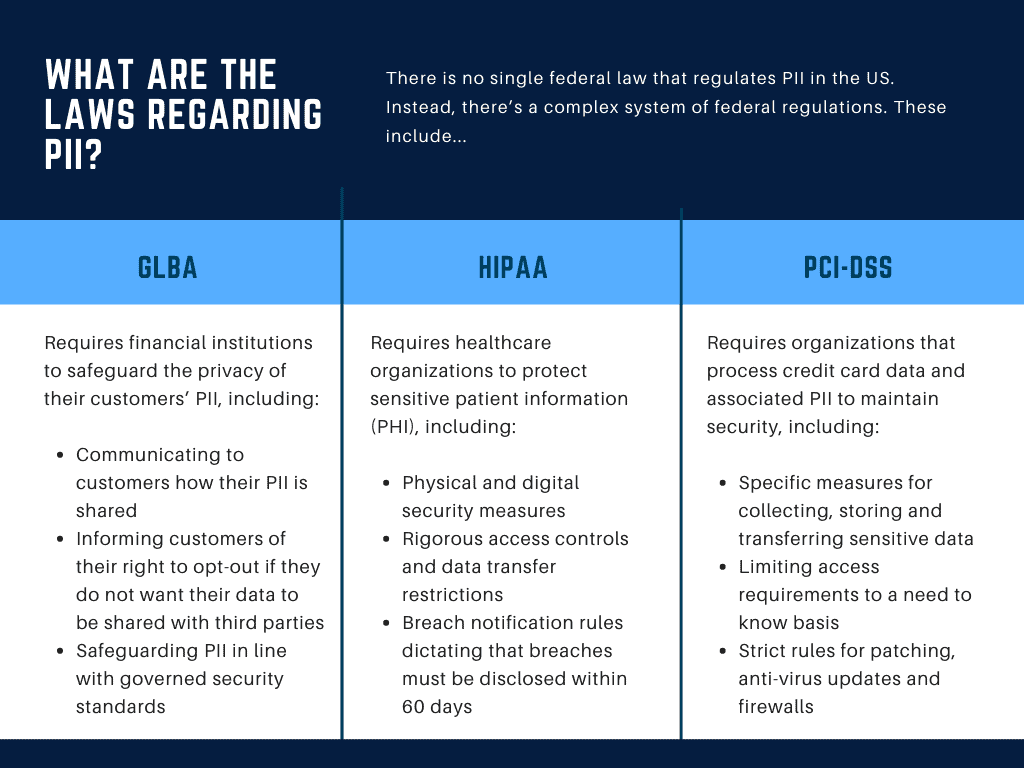
There is no single federal law that regulates PII in the US. Instead, there’s a complex system of federal regulations, state laws, and self-regulation by industry groups. These include:
- The Federal Trade Commission Act (FTC Act), which prohibits unfair or deceptive trade practices involving the collection, processing, and disclosure of PII.
- The Health Insurance Portability and Accountability Act (HIPAA), which applies to healthcare and medical data.
- The Electronic Communications Privacy Act (ECPA) and the Computer Fraud and Abuse Act (CFAA), which apply to electronic communications.
- The Fair Credit Reporting Act (FCRA), which regulates information regarding consumer credit.
- The Controlling the Assault of Non-Solicited Pornography and Marketing Act (CAN-SPAM), which regulates commercial emails.
- The Children’s Online Privacy Protection Act (COPPA), which applies to the online collection of information from children under 13 years old.
Because there is no central directive from Washington for data privacy, many states have enacted their own laws:
- The California Consumer Privacy Act (CCPA) is a comprehensive piece of legislation for consumer privacy protections on the internet. It was enacted in 2020.
- The Stop Hacks and Improve Electronic Data Security (SHIELD) act was introduced in New York in 2019. It created more rules and regulations for organizations that collect New York citizens’ PII.
- Passed earlier this year, the Virginia Consumer Data Protection Act (VCDPA) gives Virginia consumers more influence over how companies use their personal data.
European Union:
The Data Protection Directive of 1995 regulated the processing of personal data within the EU. This was superseded by the General Data Protection Regulation (GDPR) in 2018, and it applies to all websites that may be visited by EU residents, regardless of their location in the world.
This law imposes hefty fines for compliance violations, which can be up to 4% of a company’s annual revenue.
What are the principles of PII protection?
The growing number of national, international and state data privacy regulations show just how serious protecting PII is. To achieve compliance, businesses must have a firm understanding of the laws and requirements governing PII.
To assist with this, in 1998, the U.S. Federal Trade Commission (FTC) published a report containing essential data privacy principles for the Internet age. While the digital world has come a long way since then, these standards are still relevant today. Businesses should adopt them as a foundation for safeguarding PII.
- Notice: This is about informing consumers – for example, visitors to a website – about the data that could be collected from them, and how it will be used. Notice is integral to transparency and data ethics. It is a consumer’s right to know that their data is being stored, analyzed and shared.
- Consent: It is unlawful to use personal information without consent. This stage involves giving consumers a choice about how their data may be used. To be truly transparent and ensure proactive consent, we advocate using an opt-in form.
- Privacy policy: Organizations must have a well-defined and accessible privacy policy, highlighting how they process data, how it is protected, and any third parties it may be shared with.
- Access: Consumers should be granted the ability to access, edit and delete organizations’ information about them.
- Security: PII should be safeguarded with appropriate security protocols, to prevent mishandling, loss or theft.
Safeguarding PII with a data protection framework
With data breaches on the rise, and costing an average of $8.64 million each, protecting PII must be a top priority for businesses. But, as the stakes to secure data get higher, the increasing amount of enterprise cloud applications is creating an ever-growing surface area. This means securing PII is trickier than ever before.
It’s therefore paramount that organizations put in place a robust data protection framework, which is a structured set of policies for protecting sensitive data like PII. It helps define what sensitive information is, and how to implement data privacy controls to safeguard it.
The main elements of a data protection framework are:
- Data classification
Data classification is the practice of categorizing enterprise data by its type, sensitivity, and metadata, as well as its perceived value to the organization. By organizing data on such parameters, it allows organizations to:
- Mitigate risk in case data is altered, deleted, or stolen
- Comply with industry standards such as the HIPAA, DSS, or the EU’s GDPR
- Implement data access controls and come up with data protection policies
- Improve visibility and control over the vast amount of stored and produced
For a more detailed explanation of data classification, read our guide here.
2. Privacy Impact Assessment (PIA)
PIAs are an evaluation of how PII is being gathered, processed, shared and stored. These reports are an important part of demonstrating compliance for regulations like GDPR, in cases where operations extend to Europe. PIAs should be carried out on an ongoing basis, to ensure that personal data is being used ethically throughout its lifecycle.
3. Implementation of security controls
Security controls go a step beyond categorization and assessment to proactively secure the PII that organizations hold. In the remote working world, it’s no longer enough to focus on network security alone. Instead, organizations should take a data-centric approach that includes the following solutions:
- Data masking techniques – such as data encryption – act as a lock around sensitive data like PII, ensuring that it can only be accessed by users who have the key.
- Data loss prevention (DLP) is a comprehensive suite of technologies that helps to monitor and protect PII as it moves within the organization’s infrastructure, cloud applications and servers. In conjunction with data classification policies, DLP remediates threats to sensitive data. For example, if a user attempts to send PII to a third-party on an app like Slack, DLP will automatically redact it in real-time, preventing a data breach.
- A zero-trust approach to security is a framework for preventing breaches, by giving employees and third-parties access to only the information they need to do their jobs, and nothing more. It’s the idea that no one can be trusted when it comes to data security. This approach reduces the likelihood of a data breach via human error, or through stolen credentials. Forward-thinking DLP solutions incorporate zero-trust principles into their models.