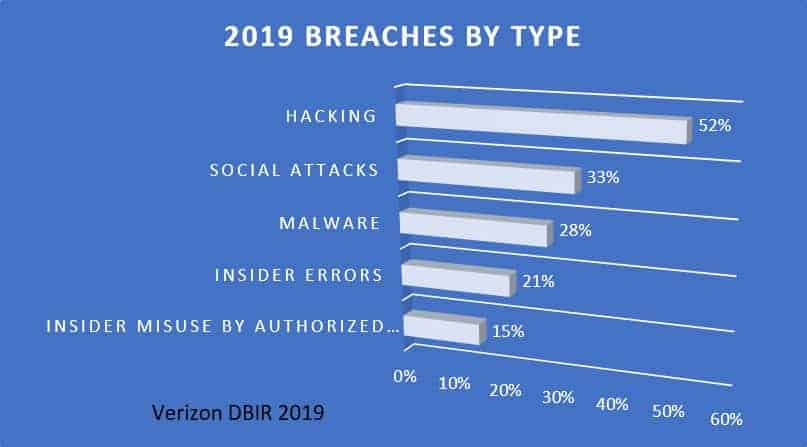
In the US alone, the overall cost of healthcare breaches in 2019 was US$ 11.8 billion (£9.2 billion) – more than double the 2018 figure, & healthcare breach discovery time is the longest for any industry.
Technology and process audits such as SOC2, ISO and HIPAA compliance certificate often creates a false sense of security posture and privacy law adherence. Being ‘compliant’ does not make an organization safer from breaches. In fact, the number and magnitude of breaches is increasing in spite of the popularity of these audits.
Take HIPAA for example. “1.5 million patients’ data exposed in September-reported healthcare breaches. Nearly 1.5 million people had data exposed in healthcare breaches reported to the federal government last month. That’s more than double the roughly 730,000 people who had data compromised in healthcare breaches reported the month prior.”
According to HIPAA Journal, the number of large healthcare data breaches is steadily growing – from 310 in 2014, to 510 in 2019.
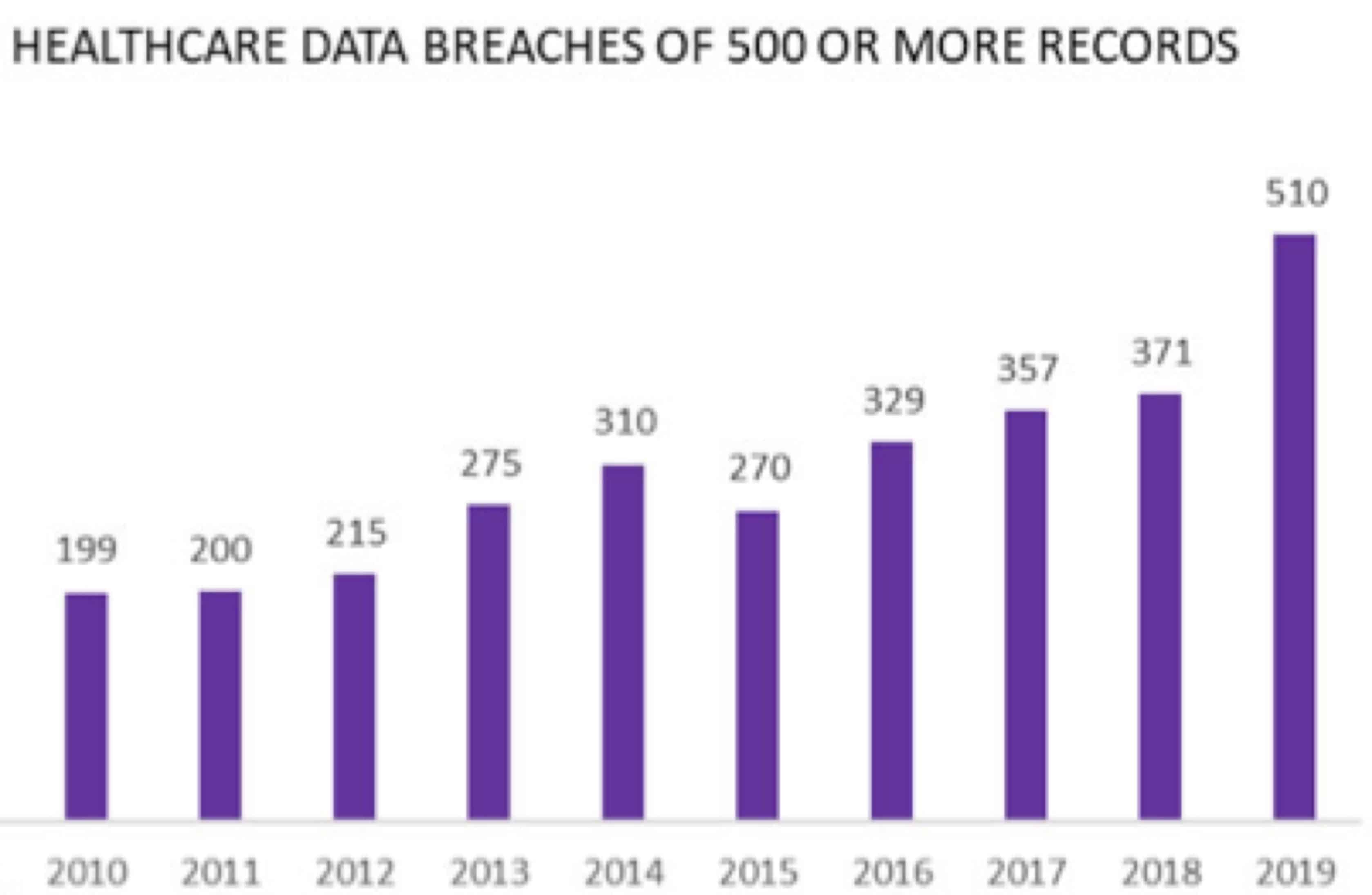
By now, one would expect HIPAA legislation to have had a positive impact, but that’s not proving to be the case. Why, despite broad compliance, is HIPAA legislation not reducing the number of data breaches?
In this article we outline what HIPAA and SOC 2 is designed to accomplish, and why taking adherence to these measures as the final word can lead to a false sense of security. We also outline what practical strategies companies can use to truly secure their at-risk data.
How does SOC2 and HIPAA work?
First, let’s look at audit standards such as SOC 2 and ISO 27001. First, the System and Organization Controls (SOC) standard is defined by the AICPA (the American Institute of Certified Public Accountants). It is a rigorous audit procedure that intends to ensure that you manage your data in a way that protects your interests, and that protects the interest of your clients.
An independent auditor reviews your internal data security controls and issues a SOC 2 attestation. The practical implication is this: at a specific moment your company (or your service partner) was found compliant with set criteria. Essentially, the criteria the AICPA deemed adequate when SOC 2 was published.
However, SOC 2 criteria are not dynamic: it does not reflect the most contemporary risks. There is another issue: a SOC 2 attestation reflects the past – it does not prevent a drift away from compliance.
HIPAA poses similar challenges. While SOC2 is voluntary, the Health Insurance Portability and Accountability Act (HIPAA) was signed into law in 1996 with maximum fines of up to $1.5m. Compliance is mandatory for covered entities. In data security circles, when HIPAA is referenced, we generally refer to Title II of the Act and the updated HIPAA Final Rule on Privacy and Security.
As a law, HIPAA provides a starting point that enforces minimal compliance for healthcare providers. However, as with any law, HIPAA carries loopholes. And just like SOC2, HIPAA is a box-ticking exercise. HIPAA is also not in tune with a cloud-first technology environment delivered via SaaS and used in remote working scenarios.
It’s also worth noting that HIPAA is not nearly as in-depth in nature as SOC2. Arguably, it is a law that requires little more than lightweight self-certification. It creates a dangerous situation where appearing to comply with the law leads to a false sense of security.
Why do SOC2 and HIPAA fail to deliver?
Simply put, work is done differently over SaaS than what these audits were supposed to solve for. Let’s look at a few examples.
Collaboration software
You can audit your internal processes and security measures as often and as hard as you want – only for a collaboration tool to open the door. Tools including Slack, DropBox and Airtable are critical for productivity and are in use by companies of all shapes and sizes.
However, the productivity effect relies on openness and sharing. As a result, data can rapidly leave designated, safe silos. In turn, audit frameworks do not effectively account for the data leakage risks posed by collaboration and productivity platforms.
Third-party security
Audits and laws cover the internal policies and processes of your business. But what about your technology partners? It’s common for business technology to plug into countless external, cloud-based solutions. Whether for collaboration or just to make essential business functions tick.
Partnering with a SaaS vendor typically means approving deep, expansive permissions that are difficult to map and track. Companies also have little control over how SaaS vendors deploy internal data security policies. Auditors may approve your procedures, but your technology partners are a big unknown.
Point in Time status
We alluded to the fact that both SOC2 and HIPAA represent an audit at a specific point in time. What happens when circumstances change? Where, for example, an employee is accidentally permitted to access data that they should not access?
Another issue is compliance consistence. In theory, organizations will maintain measures to ensure compliance when the next audit comes around. In practice, compliance is more like a valley of hills: high compliance closer to audits, lower compliance right after an audit.
Moving from ticking boxes to real-world, effective data security
Submitting to an auditing exercise has its merits. Complying with HIPAA indicates that you meet legal requirements. A SOC 2 attestation is, of course, reassuring to your clients. But effective data protection requires additional security protocols and an employee base that takes privacy seriously.
An exhaustive discussion of enterprise-grade data protection policies is beyond the scope of this article. However, here are a few suggestions that address some of the biggest weak points of audit processes:
• Data discovery. Not all data is high-risk. The first step in effective data security is to identify the confidential data in your system. In other words: where, how, and why is personally identifiable data or any other at-risk data stored in your organization? It requires a detailed diagnosis of what data is stored locally, and in the cloud.
• Real-time monitoring. Data needs to flow freely and dynamically and that demands ongoing, real-time compliance monitoring. Data loss prevention (DLP) policies can flag confidential data that is shared inappropriately. Likewise, advanced data privacy services will monitor social tools such as Slack to block the exposure of confidential data.
• Track data movement. External partners operate on a “need to know” basis, but lax permissions can mean that private data is inadvertently exposed. Effective security requires a close watch on how data flagged to be critical is moved between and amongst the many external vendors modern-day IT depends on.
• Controls at the data-element level. Again, given “need to know” considerations, it’s essential to enforce granular control over data. In other words, don’t share a full data record when only specific elements are needed to execute a task. Encrypting or masking data elements when sharing records is one option.
• Data breach policies. Rapidly reacting to signs of a breach is critical too and that requires pre-built policies. Reactively responding to signs of data loss can mean that crucial time is lost in cauterizing ongoing loss and in notifying those affected by data loss – which can lead to larger fines.
We’ve outlined five ways that aid companies in applying an effective rather than theoretical, tick-box data protection regime. It serves to illustrate why sticking to HIPAA, SOC2 or an ISO standard is simply not enough.
One could argue that keeping to the “spirit” of audit regimes and laws implies taking the necessary measures anyway. However, in the real world, there is a high risk that passing an audit and complying with the law will lead to a false sense of security. That’s why companies should look beyond SOC2 and HIPAA and assert broader, deeper data security protocols.