Data protection and data governance are two important facets of every organization’s cybersecurity and compliance strategy. Not only that, but they’re essential to keeping things running. If your people can’t find the data they need, or it’s difficult to use, this could cause a number of problems.
Plus, with the advent of both state and international data privacy regulations, it’s more important than ever to understand where your enterprise data is stored, how it’s used and how it’s secured.
While this sounds simple enough in principle, the task can be overwhelming. In 2020 alone, the world created 2.5 quintillion data bytes daily – that’s a million raised to the power of five (so many 0’s were not even going to type them out!). So, as a business leader, we understand that managing the massive amounts of data you and your people produce can seem challenging.
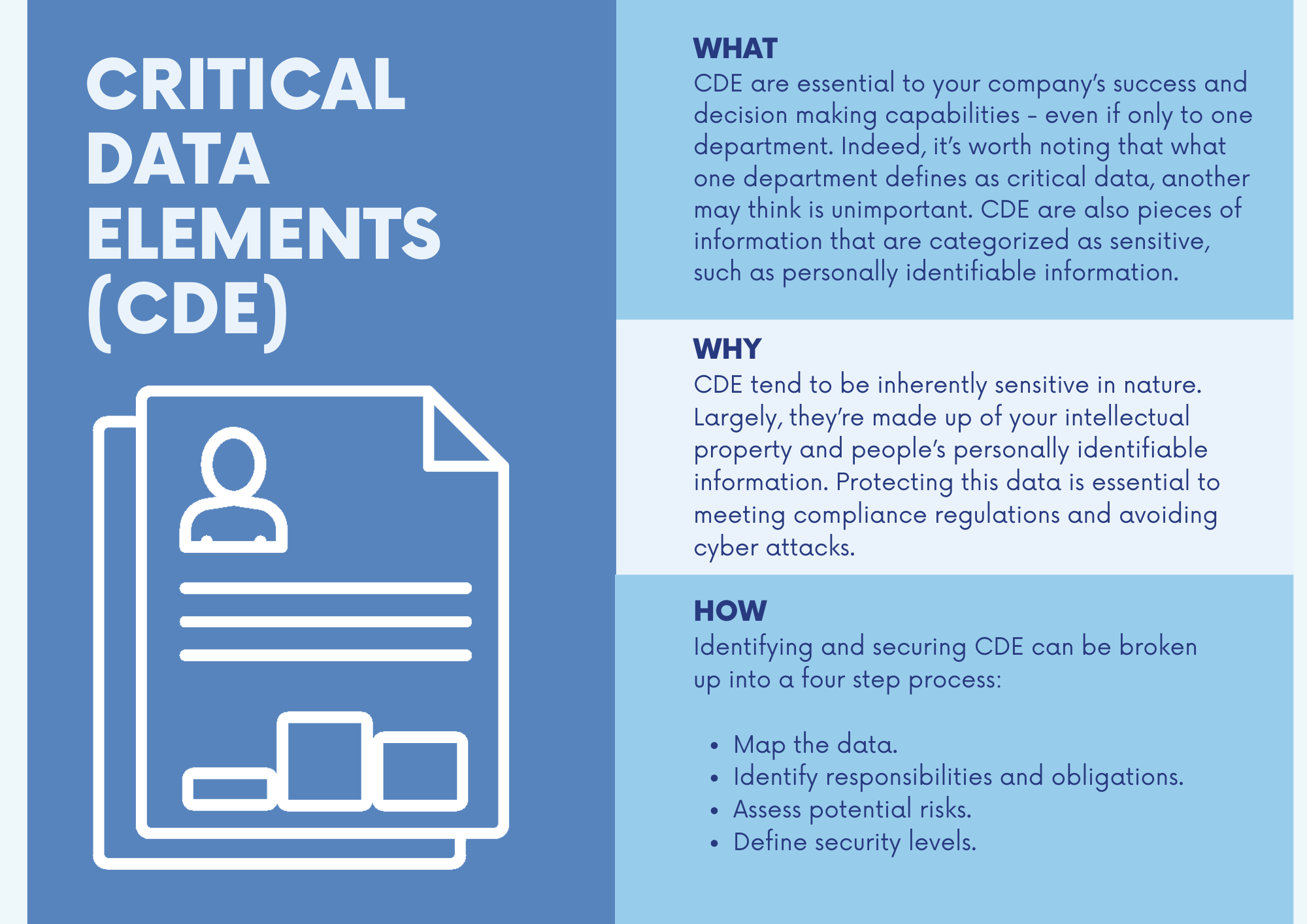
The good news is that not all data is created equal. Part of a strong data governance strategy is understanding what data is the most critical and needs special attention. This data is what’s termed “critical data elements” (CDE).
CDE are essential to your company’s success and decision making capabilities – even if only to one department. Indeed, it’s worth noting that what one department defines as critical data, another may think is unimportant. CDE are also pieces of information that are categorized as sensitive, such as personally identifiable information.
Common examples of CDE include:
- Customer data
- Employee data
- Supplier and partner data
- Operational data
- Financial data
- Data that is used for analytics and forecasting
Why is managing critical data elements so important for security?
CDE tend to be inherently sensitive in nature. Largely, they’re made up of your intellectual property and people’s personally identifiable information. Protecting this data is essential to meeting compliance regulations and avoiding cyber attacks.
As a side note, it’s also worth mentioning that a strong data governance strategy also improves employee productivity, reduces wasted resources and lessens workplace frustration. As a 2019 McKinsey study noted, 30% of employees’ total enterprise time was spent on non-value-added tasks because of poor data quality and availability. By mastering critical data elements management, the rewards are plenty.
So, how do you do it? Let’s take a look…
A strategy for critical data elements
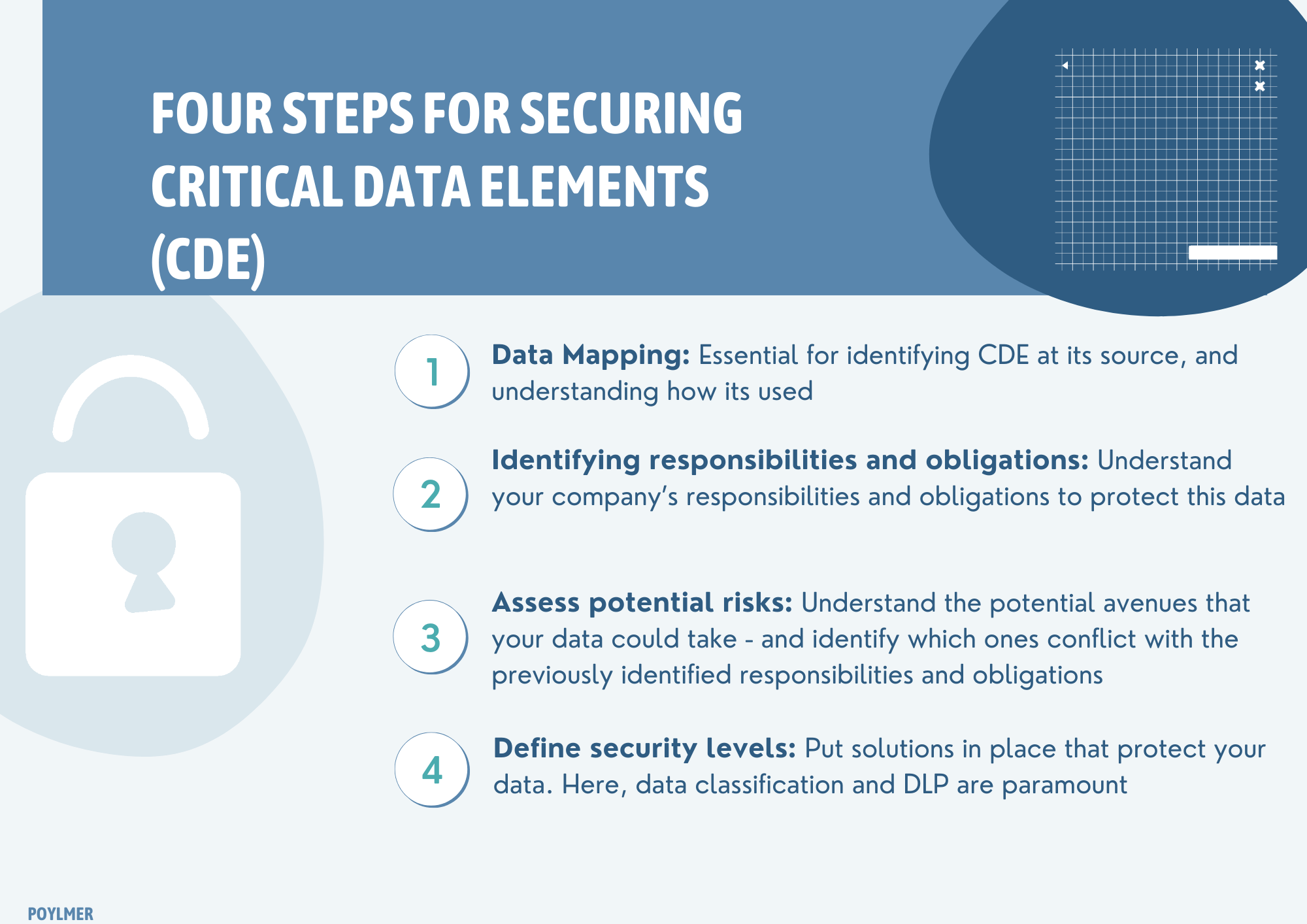
Identifying and securing CDE can be broken up into a four step process:
- Map the data.
- Identify responsibilities and obligations.
- Assess potential risks.
- Define security levels.
Mapping data
Data Mapping is a process where organizations match fields from numerous datasets into a schema – by which we mean a centralized, unified database.
It enables you to build an intelligent store of your internal and external data, providing much needed organization and structure to the masses of information you create. It is essential for effectively managing and processing CDE. By identifying CDE at its source, and understanding how it’s used, you can then move onto…
Identifying responsibilities and obligations
Chances are, a lot of your CDE will come under the jurisdiction of regulations like the GDPR or California Consumer Privacy Act. To that end, the next step is to understand your company’s responsibilities and obligations to protect this data.
Assess potential risks
While data may be created at a source, it rarely stays there for long. It can be transmitted, updated, backed up, deleted and more. You need to understand the potential avenues that your data could take – and identify which ones conflict with the previously identified responsibilities and obligations. For example, for sensitive customer data, who has access to it? Is it possible it could be downloaded without authorization? These are things you need to consider from a security standpoint.
Define security levels
Once you’ve built up this picture of your CDE and their risk profiles, it’s time to put the solutions in place that protect your data. Here, data classification and DLP are paramount.
DLP is a technology-based strategy for ensuring compliance and protecting sensitive data, including intellectual property, financial information and personal details – aka: CDE! DLP works by analyzing, inspecting and encrypting data both at rest and in motion: whether it is being sent or received through messaging applications, downloaded to an end user device or being stored in the cloud.
DLP is a must-have tool for protecting CDE in the modern enterprise. It’s often complemented by data classification capabilities: a real-time process of organizing data according to its type, sensitivity, and metadata, as well as its perceived value to the organization – based on predefined inputs from data mapping.
The road to master data management (MDM)
By completing this four step process, your company is well on the way to creating a robust master data management strategy – an end-to-end process that brings consistency, accuracy and accountability to the master data sets that organizations store and produce.
One last thing! Remember that this four step process is not a one-off. We’re creating more data by the day. Nothing is stagnant. So, as part of your CDE strategy, you need to regularly review and check your four step process, to ensure that all CDE are accounted for and secure.
As a next-generation DLP provider, Polymer has the data classification and management expertise to help you get a handle on your CDE. With real-time redaction capabilities and alert capabilities, we can bring structure and visibility to your data sets, so security is one less thing you have to worry about.