Large number of businesses leverage offshore technology teams. However, very few of those companies have data governance on customer data nor understanding of the cyber-security risks involving some amazing and cheap talent.
Chances of breaching GDPR, CCPA and other global privacy regulations is high when working with offshore development teams.
Risks of working with remote and especially offshore teams is an underappreciated source of data leaks and cyber breaches. This is probably because these risks are not either properly understood by regulators or by firms themselves.
We are bringing to attention very clear and present risks in deciding a Remote work strategy involving offshore teams. The following is a checklist that should be part of all SOWs and SLAs.
Offshore team members do not have appropriate background checks
Offshore consulting teams or even extended company staff generally do not go through the same level of background checks as ones in the US. There have been many instances on the dark web where developers are sharing credit card and other sensitive PII data of US customers acquired through their work with US firms.
Lack of security protocols on offshore team devices
Any US based firm doing business offshore needs to verify policies around bring-your-own-device and what malware protection and device security frameworks are in place. As a business your data is as protected as the weakest point and that one device without proper protection could be the trojan horse into firms databases and sensitive records.
Collaborative software
Although automation is often touted for its ability to exponentially increase efficiency and productivity, it can “brings its own risks, especially related to data security and access security.” File-sharing systems that are used to create a seamless bridge between onshore and offshore teams should be carefully considered prior to implementation, especially when used to share content and data containing sensitive customer information. Nevertheless, automation can undoubtedly be safe, as well as save companies both time and money, so long as consistent surveillance of enacted security measures is performed.
Cyber risk training and awareness
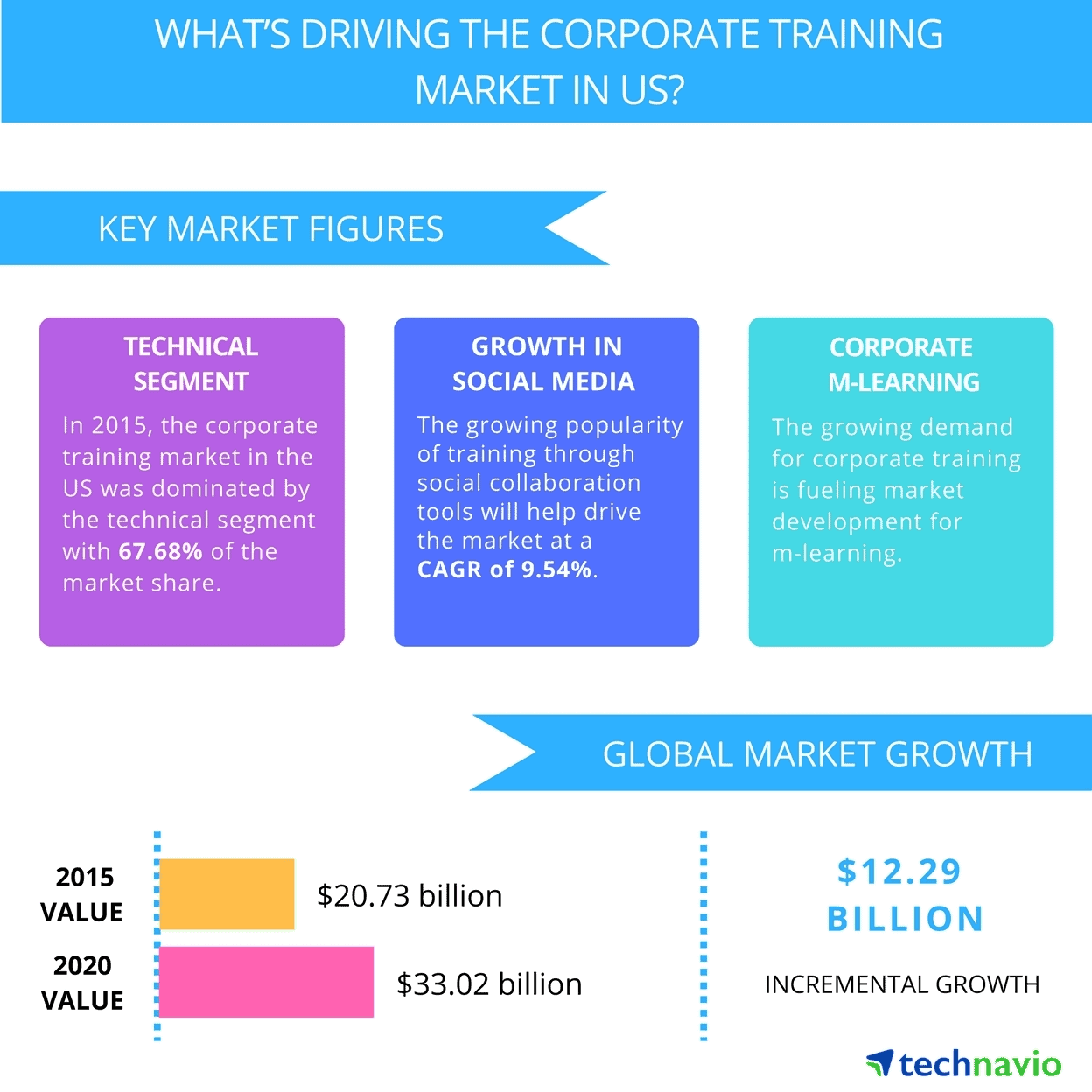
US based firms spend about $33B in corporate training with rought ~$5B spent on technical and cyber resilience. This makes the average corporate user fairly aware on not clicking phishing links and other bait-ware.
Training programs to bolster security posture in offshore teams is nowhere near as robust. To attempt to address this issue, offshore teams, although they often are not, should be properly trained regarding the technical elements of implementing data security protocols and guidelines. According to ISACA, this training can either be based on a framework or can be area-focused, for example, on topics such as network security, access control, data risk assessments, etc.
Network breaches
Following are other areas that need to be accounted for to improve resiliency in a firm’s security posture.
- 2 Factor authentication and Password Managers are a required tool for anyone onshore or offshore.
- Reducing the common data sharing platforms between onshore/offshore teams. Relying on Slack or open AWS S3 file links shared across communications channels are sources of risk.
- No Global Shared folders or weekly cleansing of files in such data sharing folders.
- Database access keys that are rotated frequently.
The spirit of Europe’s data privacy laws
In response to the plethora of data privacy risks that companies working with offshore teams might pose to their customers on a daily basis, the European Union began to roll out some of the world’s strictest online data privacy laws in May 2018.
Under the G.D.P.R. or General Data Protection Regulation, the European Union has enacted a set of rules which “aim to give internet users more control over what’s collected and shared about them,” while simultaneously punishing non-compliant businesses. And so, there are certain criteria that must be abided by when handling personal data. As a result, it is imperative that companies take care when sharing personal customer data with offshore teams, as to avoid any legal repercussions under local regulations.
References
Narang, Vinay. “Offshoring: Getting It Right Through a Security and Privacy Lens.” ISACA, 20 Dec. 2018, www.isaca.org/resources/news-and-trends/isaca-now-blog/2018/offshoring-getting-it-right-through-a-security-and-privacy-lens.
Satariano, Adam. “What the G.D.P.R., Europe’s Tough New Data Law, Means for You.” The New York Times, The New York Times, 6 May 2018, www.nytimes.com/2018/05/06/technology/gdpr-european-privacy-law.html.
——————–
Polymer protects against data loss (DLP) on modern collaboration tools like Slack, Dropbox, Zoom, Github and more with configurable real-time redaction of sensitive and regulated information such as PII, PHI, financial and security data.
Yasir Ali | yali@polymerhq.io | www.polymerhq.io