Enterprise privacy practices and security posture in general have not kept up with the increasingly decentralized tech stack. The remote workforce phenomenon recently, and cloud adoption in general, is accelerating adoption of tools and services that should trigger a ‘rethink’ by enterprises to look deep into data breach risks from within.
Background
As an organization you are no longer a ‘victim’ but a ‘culpable’ of a data breach. A 23% CAGR in security related spending globally (Gartner) demonstrates how privacy and security is a paramount concern within CISO and CIO offices.
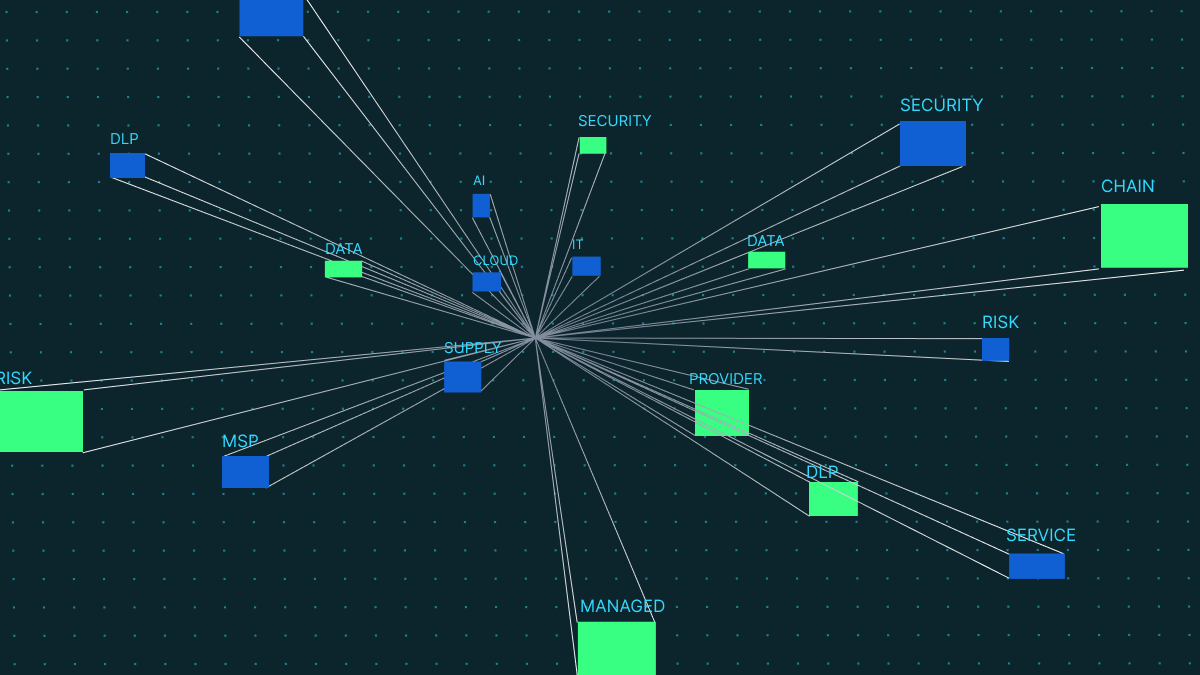
As the stakes to secure Personal identifiable information (PII) get higher the move to cloud (or SaaS services) is creating an ever-growing surface area to secure data.

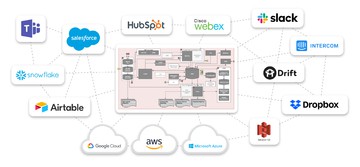
Additionally, due to Covid, future of work is playing out in expedited fashion with the adoption of collaborative tools. Advancements in low-code software makes it super-easy for individual installs and easy plug-and-play by line workers. No need to bother the database team when one can use Google Sheets, Airtable, Notion or Redis.
In this piece we will look at 3 related themes at a high level to highlight systematic challenges ( in spite of the $ spent) that is making it more difficult for organizations to be data-leak resistant and privacy-compliant.
1. Collaboration tools

(referring to tools such as Zoom, Slack, Hubspot, Notion, Google Docs/Sheets, Airtable etc.)
i) Lack of Policies or guidelines on usage for data sharing on these tools is blatant, especially in the post-covid work from home movement. With no clear guidelines, sharing of sensitive data across large-network channels is a norm and exposes vulnerabilities in the most unexpected places for an organization.
ii) Modern collaborative tool platforms are generally thin-clients that are easy to install, in many cases leveraging Google Chrome or are lightweight desktop tools. The ease of inter-opertability makes it easy to move data between domains. In effect, creating copies of PII in multiple places. These are typically not managed and often leads to disasters such as object store URLs being exposed or documents not having appropriate permissions.
2. Micro-services
i) Who owns the data in an enterprise? Is it is the database administrators or the application domain personnel. Lack of clear guidelines and policies on this creates a grey area where data handoffs between databases and applications is typically not a standardized approach across organizations.
ii) Both synchronous & asynchronous services have allowed faster go-to-markets. Just the nature of ‘speed of delivery’ behooves a developer to get what is needed with minimal latency rather than bother about privacy.
We often see multitude of PII data copies in unsecure areas due to the proliferation of microservices. This ease of use has unfortunately created bad patterns where privacy is secondary.
3. Cloud-based Infrastructure as a service

Migrating on-prem Identity Access Management (IAM) and User Permissioning in the cloud is a big challenge. Typical reason for this is culture- operators not necessarily equipped with a cloud-first mentality. This manifests itself in cloud migration projects where migrating User policy settings is typically a big bottleneck. This is not to say that technical issues are not there. For example:
i) Cloud Permissioning are generally Stateful. State has to be in sync with the infrastructure all the time. In large organizations if the stack is too large, resource management can be tricky and generally handled with ‘short-cuts’
ii) Vault-based key management systems such as AWS KMS or Hashicorp are great to store secrets but are complex to manage and require entire tech stacks to follow CSEK methods. Most companies will get the larger databases in-tuned but vulnerability points could be lurking outside these domains.
Summary
In summary, implementing Collibra or other Data governance products is not the panacea to solve some of these festering and ever-growing issues. Becoming data-leak-proof goes hand in hand with becoming data-privacy-compliant. This is not a top down solution but rather an employee-led, bottoms up approach of securing most vulnerable points along with the large data stores.
Current environment provides an opportunity to rethink handling of sensitive data from the inside out. With 20% of data breaches due to internal workforce, it is even more relevant to focus on creating a framework of access to data on a need-to-know basis.