….Yes, probably. That’s the long and short answer to the question our title poses. But, we know you want more detail than that: what are rogue cloud apps, why are they leaking your data, and how do you get a handle on this phenomenon? We’ve got you covered. Let’s dive in.
What are ‘rogue’ cloud apps?
Rogue cloud applications are apps that your employees use without your knowledge. You haven’t adopted these applications officially. Instead, your employees have downloaded them independently, without you knowing.
There’s not usually malicious intent in this. Most employees just want to be as efficient and productive as possible – and there are now hundreds and thousands of cloud applications out there to help them with this. Moreover, most of these apps are free, simple to install and available via any Internet connection. Apps like Trello, Dropbox, Slack and Zoom are common examples.
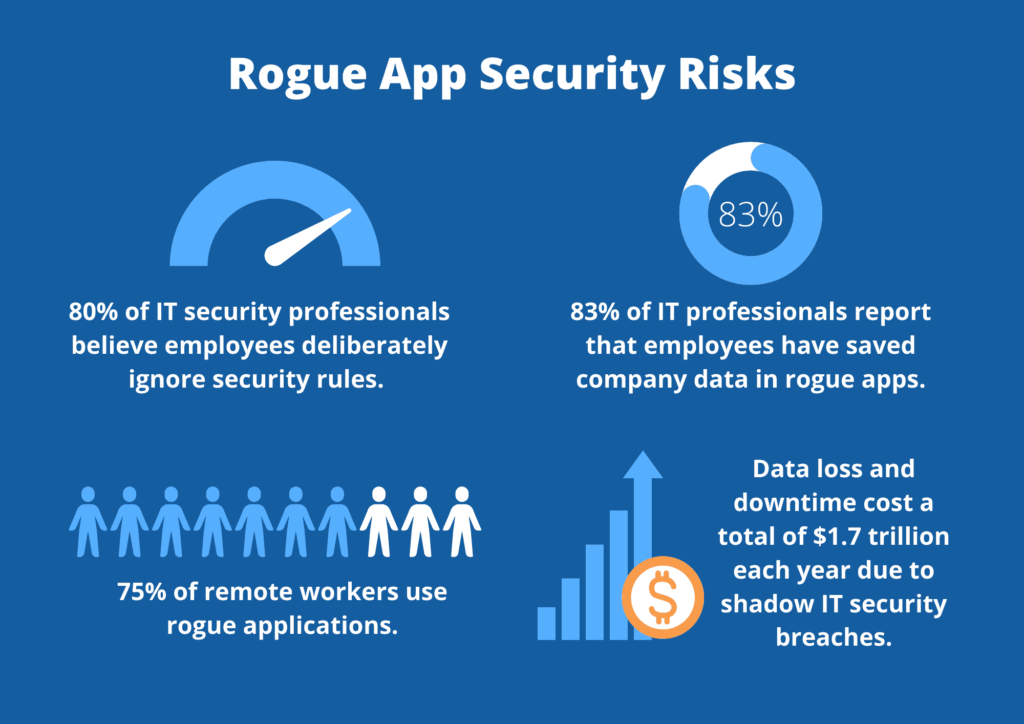
Research indicates that almost three-quarters of remote workers use these rogue applications – and a quarter admit to using a lot of them. This phenomenon is also known as ‘shadow it’; the practice of employees using technology without the IT department knowing.
Why is rogue application usage a problem?
While some rogue applications may be harmless, many threaten enterprise security and compliance obligations. Visibility and security go hand in hand – but rogue apps hide in the shadows, making it impossible for the IT team to know where data is, how it’s being used and who it is being shared with.
The security risks surrounding rogue applications can be divided into three main buckets:
- Increased risk of a data breach or data leak
Applications that the IT department sanctions usually go through thorough security checks before roll-out. The IT department also takes responsibility for updating these apps regularly in case of vulnerabilities. Applications that employees install do not go through the same analysis, meaning they could be more vulnerable to security risks.
Moreover, we must remember that employees are not security experts. They may incorrectly configure the rogue applications they use, leaving data publicly accessible. This is becoming more and more common. Gartner believes that, by 2025, 99% of cloud data breaches will be caused by this kind of human error.
2. Compliance and regulatory violations
Unmanaged applications are a huge compliance risk, which could easily lead to violations of regulations such as HIPAA, PCI, GLBA and GDPR. With the average HIPAA fine now at $1.5 Million, this is a costly expense all businesses should look to avoid.
3. Low visibility
IT departments cannot protect what they don’t know. As data passes through rogue applications, the IT team loses control and visibility. This, in turn, has a domino effect on the team’s ability to perform disaster recovery, classify data, and implement adequate security protection safeguards.
Quick stats – rogue app usage
- Shadow IT cloud usages is estimated to be 10x the size of known cloud usage.
- 82% of teams have pushed backed on IT or management about which collaboration tools should be used.
- 83% of IT professionals report that employees have saved company data in rogue apps.
- Data loss and downtime cost a total of $1.7 trillion each year due to shadow IT security breaches.
- More than 1 in 5 organizations have experienced a cyber event due to an unsanctioned IT resource.
How to mitigate the risks of rogue applications
Many companies have corporate policies that forbid the use of rogue applications. Honestly, though, these policies don’t work. Most of the time, employees will choose efficiency and productivity over security. In line with this, 80% of IT security professionals believe that corporate employees deliberately ignore security rules issued by the IT department.
Sure, you could put in place technologies that block access to specific websites and applications, but this will hamper the employee experience, leading to frustration and possibly low productivity.
So, rather than focusing on app security, we advise you to focus on data security instead. By putting in place a solution that secures sensitive data wherever it goes, your employees can use any apps of their choice. At the same time, you and your team can feel confident that no data breach, data leak or compliance fine will arise.
This kind of solution is known as cloud data loss prevention (DLP). Here’s the technical explanation of how it works. Cloud DLP uses API controls to monitor and secure corporate data as it travels through cloud applications. It works scans your cloud environment in real-time to discover third-party apps that the IT team may not be aware of and then uses risk-based analysis to determine appropriate security policies.
In laypeople’s terms, it’s helpful to think of cloud DLP as a virtual bodyguard for your sensitive data. It ensures that only authorized personnel access your data and prevents sensitive data from going anywhere it shouldn’t.
The best-in-breed of these solutions are also self-learning and super easy to deploy. While legacy DLP solutions are complex to manage, DLP solutions like ours use AI to automatically act on your behalf, blocking policy violations and redacting sensitive data in real-time.
Plus, with context-driven risk recognition, cloud DLP learns from historical usage patterns. This self-learning engine can then predict and prevent privacy violations before they occur – even if the data is unstructured.
Cloud DLP is essential for combating rogue apps – but its benefits go way beyond that! It can also help you secure data in sanctioned SaaS apps like Teams or Google Workspace. Essentially, a great cloud DLP solution will become your one-stop shop for all things data protection and compliance in the cloud.
Given that the cloud is undoubtedly the future of business, there’s never been a better time to invest in SaaS DLP.