Research shows that 94% of organizations are concerned about cloud security, with misconfigurations and unauthorized access ranked as the most significant security threats by IT leaders.
It’s understandable why they’re worried. As cloud adoption has increased, the number of data breaches in the cloud has also skyrocketed.
Most of these breaches aren’t the result of advanced, complicated security threats. Instead, they’re down to poor identity and access management (IAM) on the customer side. This issue is so prevalent that Gartner believes, by 2025, 99% of cloud security failures will be the customer’s fault – and a huge 75% of those failures will occur due to poor IAM.
It’s clear that IAM is a beast that needs to be tamed. As cloud applications continue to proliferate, and employees and partners access these apps from various devices, managing access privileges and securing sensitive data are paramount.
Chances are, you already have some form of IAM process in place – but you’re concerned that it might not be robust enough. This worry increases if you operate in a multi-cloud environment, using a host of different cloud vendors and applications.
While these vendors offer their own native IAM tools, these tools only work within singular cloud environments, creating silos, roadblocks and complexity where IAM feels more like a tangled mess than a streamlined, secure process.
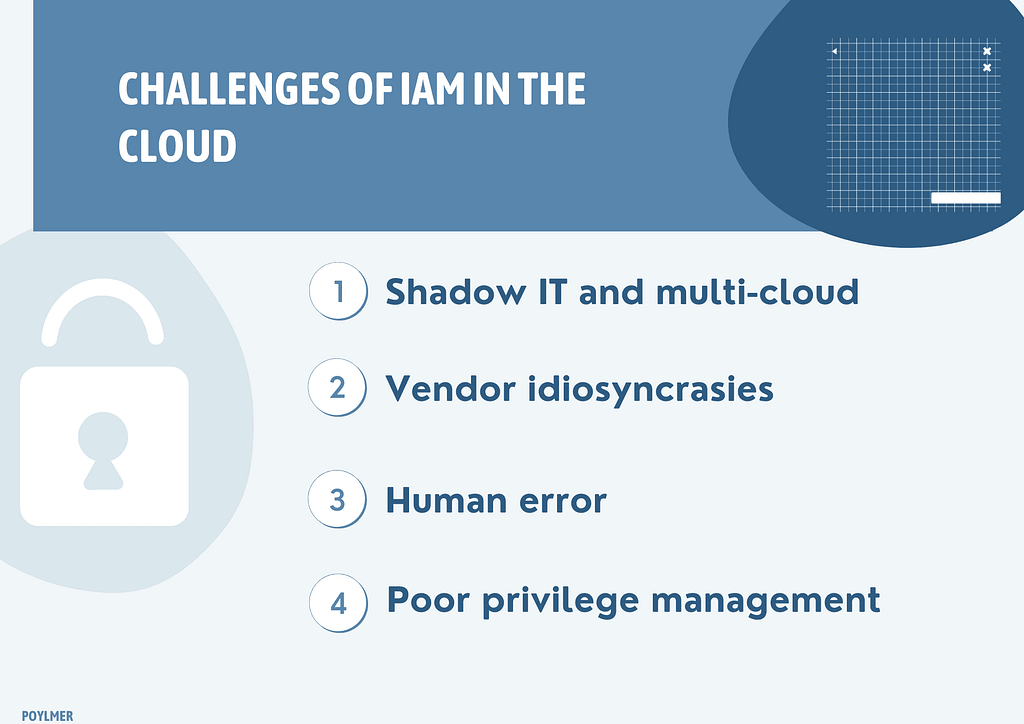
The challenges of IAM in the cloud
To help illustrate the challenge, here are some of the most common obstacles we see to successful IAM in the cloud:
Shadow IT and multi-cloud: Keeping track of identities across a growing portfolio of cloud applications is extremely challenging and time-consuming. Moreover, many employees take cloud usage into their own hands and use applications that the IT team does not even know about.
Dynamic changes: Cloud applications are constantly evolving, and so is the workforce. As people come and go, and containers are used and then forgotten, keeping track of who should have access to what is difficult.
Vendor idiosyncrasies: Many IT personnel might feel like jacks of all trades but masters of none. By this, we mean that every cloud provider has its own way of handling IAM. Each vendor will have different policies, permissions and capabilities. Streamlining IAM across these various providers may not be possible, and, even where IAM has been correctly configured, one small change could set everything off balance.
Human error: Employees may unintentionally expose cloud instances by misconfiguring them and leaving them public. We’ve seen this a lot with AWS S3 buckets. For example, the security company Verizon suffered two data breaches only a few months apart, exposing more than 6 million customer accounts due to misconfigured S3 buckets.
Poor privilege management: It’s common for teams to share login details amongst themselves for efficiency. Sometimes, IT personnel may also not be stringent enough with their permissions, enabling users to access and alter more information than they should be able to. Again, this can lead to data leakage or even theft.
IAM faults are a data breach waiting to happen
If identity and access management is poorly implemented, your company is just one wrong turn away from a data breach – and possibly a hefty compliance fine too, if your governed by HIPAA, CCPA, GDPR or PCI-DSS.
Even if you’ve invested millions of dollars in watertight cloud security, a misconfiguration could end up costing you billions in data breach remediation costs and compliance fines.
It’s clear that something needs to be done.
Reimagine cloud security with next-gen cloud DLP
We’ve written extensively about how to improve IAM in the cloud. But IAM alone will never be enough. Your IAM strategy needs to be complemented by a more rigorous approach to cloud security management, focusing on access at the data level rather than the application level. That’s where cloud DLP comes in.
Cloud DLP technology-based strategy for ensuring compliance and protecting sensitive data, including intellectual property, financial information and personal details. DLP works by analyzing, inspecting and encrypting data at rest, in use and motion as it travels through cloud applications.
In practice, this means DLP protects your sensitive data as it is being sent or received through messaging applications, downloaded to an end-user device or being stored in the cloud. To do this, it uses AI-powered actions such as redaction, blocking and nudging your users towards more secure behaviors. The action the DLP solution takes depends on the context of the situation.
While IAM policies often fail or are too clunky, cloud-DLP has an extremely high success rate. It works dynamically in your SaaS apps, discovering, classifying and protecting data in real-time.
How cloud DLP can protect against IAM faults
Here’s a deeper look at how cloud DLP can support data security in the cloud.
Deep visibility into multi-cloud environments: While IAM solutions are often vendor-specific, a good cloud DLP solution will work across your cloud environments like Slack, Teams and Google Drive. You get one centralized console, which gives you visibility and control over your data across all these applications.
Real-time, granular IAM: Cloud-DLP protects data at the source, ensuring that it cannot be viewed or edited by anyone it’s not supposed to. best-in-breed solutions feature intelligent, multifaceted permission settings that enable pointed data access or restriction based on role, responsibility, employment status.
Enforce regulatory policies: Cloud-DLP automatically monitors, intercepts, and redacts sensitive data according to FINRA, HIPAA, and other security privacy rules across your cloud applications.
Improve user awareness about security: Security aware culture is the best defense against ransomware, data breaches & insider threats. Leading cloud DLP solutions incorporate ‘learning moments’; nudge tools that alert users to policy violations and redact the data at risk.
Incident response and auditing: Cloud DLP tracks and audits user interactions with data assets such as access, sharing and downloads. Any policy violation is tracked, alerted and automatically remediated without human intervention. Compliance teams are notified of any high-risk incidences.
The cloud is undoubtedly the future of work – but cloud security breaches are one of the most prominent challenges organizations will contend with within the coming years. Don’t let your security investments go to waste due to faulty IAM policies. Make sure you’ve got intelligent, cloud-based DLP enabled, so that your data is protected no matter what.










