The cybersecurity training market is “globally exceeds $1 billion in annual revenue” and is constantly growing at about 13 percent per year(KnowBe4). An employees’ actions can damage an organization’s security and lead to many large expenses due to information breaches. Employees (and their corresponding mistakes) are the single biggest security risk for organizations. An average […]

How did T-Mobile breach occur?
Mobile carrier T-Mobile suffered a massive data breach recently, the 5th such occurrence in the last four years. Preliminary analysis revealed that the breach affected nearly eight million current postpaid customers and forty million former or prospective clients who had applied for credit with the company. The compromised data is as sensitive as it could […]

IP spoofing: what it is, & how to protect against it
Back in 2011, a botnet managed to infect an estimated 1 million computers worldwide. Known as GameOver Zeus, the infamous malware was programmed to specifically steal banking credentials. It then used the captured banking information to initiate or re-direct wire transfers, managing to steal over $100 million from individual users, businesses and organizations. It took […]

DO NOT Go all-in on a XDR & SASE solutions ..just yet!
Another day, another security acronym splashed across vendor marketing brochures. In present times, the most popular term you’ve probably come across is SASE, which is enjoyably pronounced like ‘sassy’. SASE stands for secure access service edge. While the term is everywhere at the moment, if you’re an MSSP looking to bolster your security offering to […]
Master data management (MDM): a key ingredient for effective security programs
Building a security program without knowing what you are securing is a fool’s folly. An inventory of assets is a necessary first step towards a comprehensive enterprise risk program. Assets can either be physical (such as laptops, server racks, offices) or digital (software, data, reports). Master Data Management (MDM) is the methodology to catalog data […]

How to buy breached data on the dark-web….fast!
Chances are, you’ve heard of the Dark Web. Often likened to the digital underbelly of the world, it’s a place that’s full of nefarious deeds. Drug sales, illegal weapons, hacking tools and stolen data are all up for grabs in its online marketplaces. However, it’s not easy to find. The Dark Web is invisible […]

What cyber insurance is right for my business?
Cyber insurance. You know you need it, but you’re overwhelmed by the types of coverage, the number of providers and the cost of insurance premiums. In fairness to you, your feelings of overwhelm are warranted. The cyber insurance market has exploded in the last few years. Spurred on by the increase in cyber crime, insurance […]
The top 3 data breach causes of 2021, & how they could be avoided
This year is shaping up to be a record setter in terms of data breaches. There were 491 incidents in the US in Q2 2021, an almost 40% increase over the same period last year. In fact, the number of data compromises recorded for the first half of 2021 already constitutes 76% of the total […]

A CFO’s guide to purchasing security products
In today’s digital world, a brand’s credibility is intrinsically linked to its ability to protect its data and IT infrastructure. This means that to maintain market share, keep customers satisfied and improve profits, choosing the right cybersecurity products is a must. Deciding which cybersecurity solutions to use was once in the power of CIOs and […]
What is data mapping?
Data is the lifeblood of the modern organization, and the number of data sources companies generate and use is growing by the day. Data takes many shapes and forms, meaning it can be difficult to structure and organize it. In fact, much of today’s enterprise data exists in silos, segmented by departments, geographies and even […]

What type of security tests should you use?
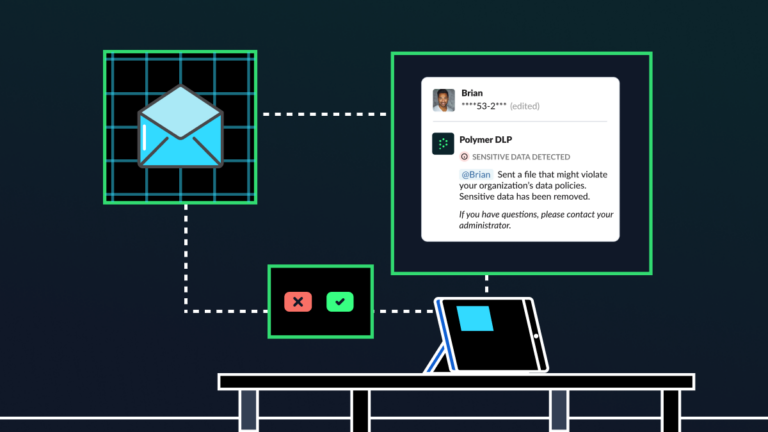
Security certifications such as SOC2, ISO27001 are great for an overall assessment of your tech and data governance posture. However these certifications are somewhat subjective and do not reflect an organization’s ability to withstand external cyber attacks or breach risks. In a cloud hosted environment with growing Shadow IT, data breach increases dramatically. Collaborative software […]