Perimeter security has historically provided the analogy of protecting the keys to the kingdom for Enterprises. Once you have been approved to enter the drawbridge which typically consists of verifications such as password, VPN, 2-Factor, a user can have access to all the data and applications within the castle. However once you are in the castle (or the network) you are anonymous and lose identity. Hence, spies were so effective in these environments in the eons past, and hackers in the current era.

This ‘walled’ model works well if all employees are sitting in 1 office building within an enterprise. With anyone being able to come to the gates and request access to the castle using the mobile phone or public internet connected wifi, the robustness of the drawbridge protocols are not quite sturdy.
Privilege access of applications
There is a huge plethora of software companies that focus on a roundabout way of securing Enterprises via outdated Access Management. Network Packet Analysis based products, VDIs etc. but the inherent problem in this architecture (as it pertains to distributed staff) was not addressed.
Cloud and SaaS software required a rethink. Defining moment came in 2010 when Google was breached by Chinese hackers leading to Operation Aurora.
Google poured in resources after that hack to develop the next generation framework of identity access management that was open-sourced in the seminal BeyondCorp white paper. Based on Zero Trust methodology, the methodology can be summarized as follows:
- Who someone is and can they be allowed to use a certain application?
- Knowing who the user is accessing a bank account (for example) beyond just the username/password based identification
- Enterprise managed Employee Device database with a listing of authorized devices
- User and group database on a single-sign on
- Authentication protocols when accessed from external networks
The big leap that has come in recent years with frameworks like Layer 7 is attestation of identity management moving to the 21st century. Now an enterprise can differentiate between someone having access to the phone directory vs someone having access to bank account details within the same organization.
As an employee I can only access authorized applications and I am good to go. But wait, how does this methodology work with data?
If many folks within an organization are working over the same platform who has access to what information? Privilege access within collaborative tool is not a thing, or is it?
Privilege access of data
Databases have traditionally been the ultimate collaboration platforms that provide the common knowledge-base for the enterprise. Access can be controlled based on authentication frameworks described above as well as low level access by the admin that can be managed by limiting access to tables or areas within the database. For example, a salesperson would not have access to the finance portion of the database in a data warehouse.
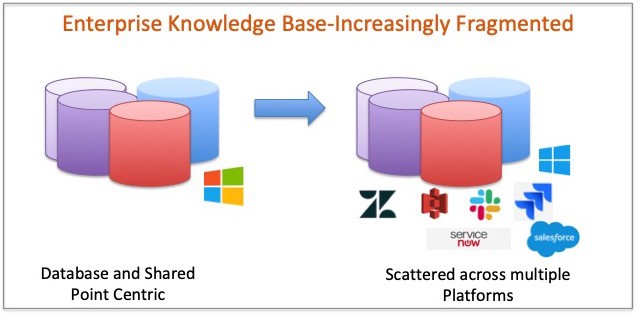
Databases (and maybe Shared folders) provided all you needed to know for a business. Salesforce changed it about a decade ago. Here was a cloud-based workflow tool to not only create and store information but also make it cumbersome to export it out. Suddenly organizations had to work with 2 sources of data now, SaaS and traditional database domain.
Over the years, other tools within the organizations were added to the mix in the form of ServiceNow (enterprise architecture artifacts, service tickets etc.), Github/Bitbucket (codebases), Jira/Zendesk (service tickets) and the list goes one.
In the knowledge space, the increasing adoption of collaborative software such as Slack, Dropbox, Zoom created other datasets that are increasingly making Enterprise knowledge store highly desegregated and scattered.
Polymer: Beyondcorp for data
Polymer was designed on the footprints of BeyondCorp- at a data level. This framework of privilege access to sensitive data was borne out of a need to identify access not at an application level but at a data element level. Each SaaS application brings with it a different set of usage patterns and what data is created. Privilege access to data within these platforms is not only needed but essential as organizations grapple with privacy and data breach risks.
We are looking to open-source aspects of this framework to open up this discussion more widely. Keep an eye out for that. In the meantime, drop me a line if you agree/disagree or have things to add to my layman summary above.