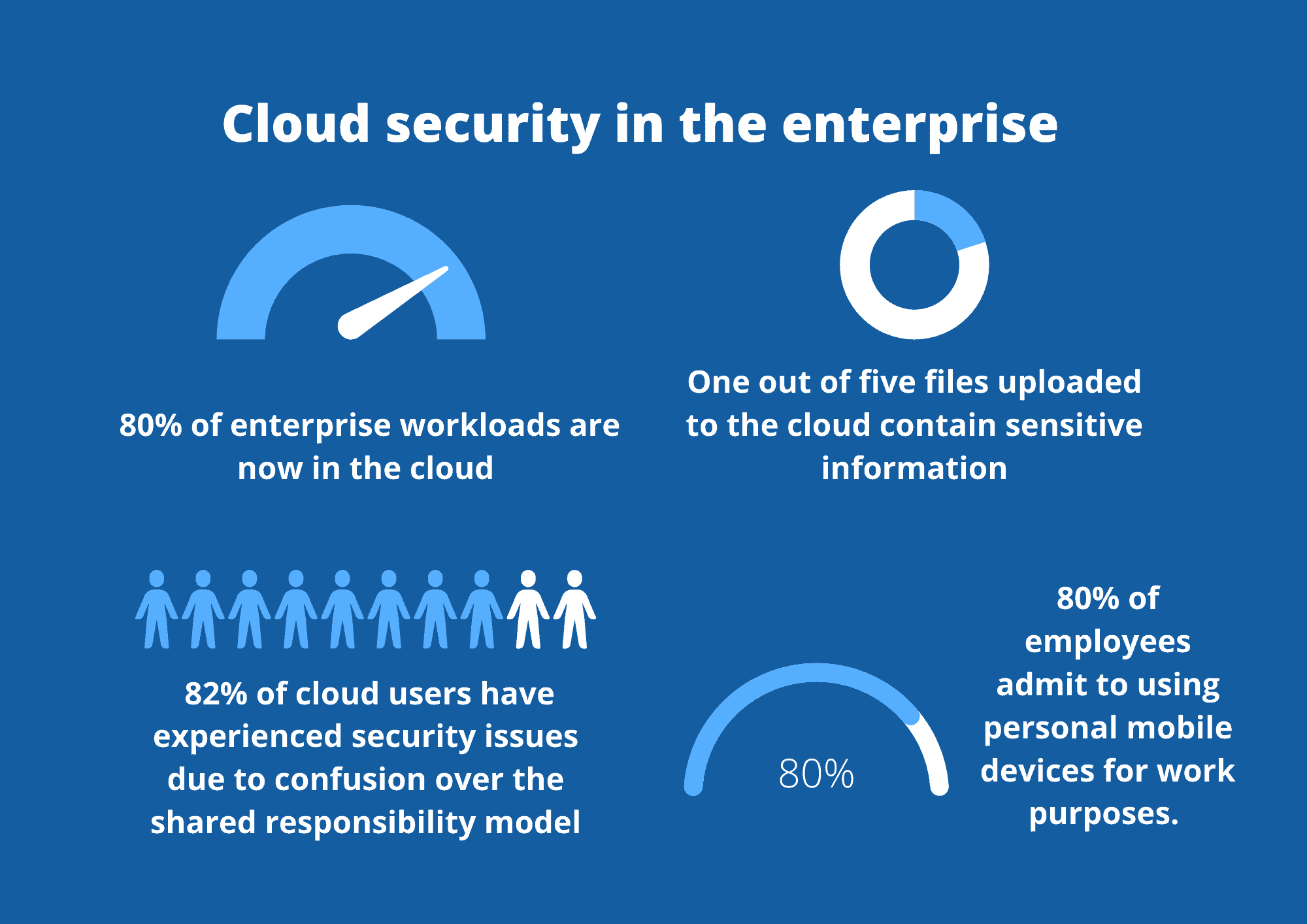
If you’re reading this, then chances are you’re in the market for a cloud access security broker (CASB). It’s a good decision; more than 80% of enterprise workloads are now in the cloud, and employee reliance for cloud applications–like Slack, Teams and Office 365–continues to soar with the rise of hybrid work.
Like all technology solutions, CASBs are an investment, so you want to make sure that your purchase will fulfill your requirements. The thing is, though, not all CASBs are created equal. There are lots of vendors out there and lots of different architectures too.
Here’s everything you need to know to make an informed choice about your CASB.
What is a CASB?
Before we dive into the different generations of CASB, let’s first get a firm definition of this technology in mind. According to Gartner, CASBs are “on-premises or cloud-based security policy enforcement points, placed between cloud service consumers and cloud service providers to combine and interject enterprise security policies as the cloud-based resources are accessed.”
A helpful analogy is to think of a CASB as the bodyguard outside an invite-only party. The party is your cloud applications, and the people trying to get inside are your employees–and possibly some hackers too. The bodyguard (AKA: the CASB) checks everyone at the door, ensuring that only people with invites can get inside. The bodyguard also checks to ensure that no one brings anything dangerous (like malware) inside or steals anything when they head home–like your company data.
What are CASBs used for?
The way organizations operate has moved forward leaps and bounds over the last decade, changing the nature of cybersecurity as a result. If you look back at the early 2000s, employees worked in the office five days a week. They couldn’t access corporate resources on their phones and most used desktop computers. In this setting, security was simple; companies simply needed to focus on securing the network perimeter.
Now, though, there isn’t a perimeter anymore. Employees work from their laptops and phones, often remotely, and engage with cloud-based applications like Slack and Teams to get their work done. From a productivity perspective, these apps are fantastic, enabling seamless collaboration and communication in the work-from-home world.
However, these apps also substantially increase your company’s attack surface. Without a CASB, companies can’t know what cloud apps their employees are accessing, what data they are uploading and downloading and whether there has been a data breach. The phenomenon is called shadow IT.
Many organizations fail to understand the cloud’s shared responsibility model to make matters more complex. According to KPMG, 82% of cloud users have experienced security issues due to confusion over the shared responsibility model.
Organizations must remember that, in the cloud, the service provider is responsible for securing the underlying cloud infrastructure. It is the organization’s responsibility, though, to keep data secure within the cloud environment. This means companies need to take care of authorization and data usage.
Going back to the party analogy: you can see why CASBs serve a purpose in the cloud environment. They’re an excellent way for companies to manage data and users in the cloud, providing much-needed visibility and control into cloud resources. A good CASB will also help with compliance, using data classification to support data governance.
The different types of CASBs
Ok, now that we’ve got to grips with the why of CASBs, it’s time to look at the what: the different types of CASBs on the market and how they work.
Broadly speaking, there’s three types of CASBs out there: CASB 1.0, 2.0 and 3.0. CASB 1.0 is the most primitive, traditional form of CASB – and CASB 3.0 is the newest of the bunch. Let’s take a look at each below:
CASB 1.0
As noted above, CASBs were created to tackle shadow IT. When SaaS applications first became popular, employees started feeling empowered to work around the technology department, downloading apps that the IT team hadn’t sanctioned. This created a data security storm. IT personnel couldn’t be sure where sensitive data was and who had access to it – a complete nightmare for compliance with regulations like the GDPR and HIPAA.
Enter CASBs: a way for companies to discover unsanctioned applications and provide visibility into their use. The original CASB was deployed as a physical appliance in the customer’s data center with various proxies. It used hard and fast policies to determine whether an application should be permitted or blocked.
While this helped fight shadow IT, it wasn’t an infallible solution. For one, deployment was often clunky and cumbersome. Moreover, proxies have a security disadvantage: they can’t see traffic unless this traffic is aligned to a specific handle.
Forward proxies, in particular, were hard to deploy and invasive to users. For these to work, organizations had to install software on end users’ devices to investigate traffic. This created privacy concerns and was hard to roll out in large companies with thousands of employees.
Reverse proxies were a bit better – but they also had their drawbacks. Namely, they would run into issues and often miss users who weren’t configured to access cloud services through them.
CASB 2.0
CASBs had potential but they also had issues. Vendors realized that they needed to innovate these solutions to be more effective and less invasive. Enter CASB 2.0 to save the day.
CASB 2.0s integrate with application programming interfaces (APIs). They are out-of-band solutions that integrate into cloud services, providing security and monitoring by maintaining a dialogue with other known APIs. Not only are they able to scan SaaS apps for sensitive data, but they can also detect instances of malware and analyze user behavior to prevent insider threats.
Below is a look at the four main pillars of a CASB 2.0. If you’re shopping for a CASB, make sure that your provider can meet these requirements:
- Visibility: A CASB 2.0 will give you granular visibility into cloud application usage, including which employees are using cloud services, how they are accessing them and what information they are trying to upload, download and store in the cloud.
- Compliance: You need to know where your data is to secure it. With a CASB 2.0, you can see precisely where information is, where it’s been and where employees are trying to move it too. Not just that, though, you can actually control the flow of data. Using pre-defined policies, you can ensure that no data in the cloud is moved, edited or deleted without the IT team’s approval.
- Data Security: A CASB 2.0 can enforce policies like encryption, redaction and authentication to ensure that data is only accessed legitimately. The best in breed of these solutions also embed employee training into the daily workflow, nudging users to make security-conscious choices and protect data as they work.
- Threat protection: With access and authentication controls in place, a CASB 2.0 framework helps you manage cyber risks and subvert malicious actors trying to get their hands on your data.
Is there a CASB 3.0 coming?
You might be wondering if there’ll be a third CASB. While vendors are constantly improving their solutions, the current CASB model effectively secures cloud applications. One up and coming solution is SASE – a technology that merges WAN with CASBs, Firewalls as a Service, Secure Web Gateways and the Zero Trust Model.
However, as we’ve written about here, SASE is still in its infancy. The technology has a long way to go before it becomes mainstream. In the meantime, a CASB 2.0 framework, like Polymer DLP, is your best bet for achieving cloud security.