Here are a couple of recent data leaks to give you a sense of just how easy it is to expose data in Google Drive accidentally.
Last year the tech publication, Wired UK, stumbled upon a public Google Drive owned by the UK Government Department of Health. The Drive should’ve been private. It contained documents labelled: OFFICIAL – SENSITIVE relating to the NHS Covid-19 contact tracing app. Yikes!
Then, recently, a school student in New York found a Google Drive filled with the personal information – like academic records and other data – of over 3,000 New York City students and educational staff members. Again, this Drive was meant to be private.
These incidents aren’t anomalies. Research about Google Drive has shown that:
- 73% of employees can access data that they shouldn’t be able to
- 69% can view data they shouldn’t be able to
- 59% can see data from other departments
You might think this is an access control problem. In a way, it is – but the issue is much deeper than that.
Why access controls and permissions in Google Drive aren’t enough
While deploying access controls and permissions in Google Drive is essential. It’s not a bulletproof strategy. Here’s why:
The insider threat
The same research found that a third of ex-employees who exfiltrated data before leaving their position were encouraged by their new employers to share it with new colleagues. This is an example of the insider threat: employees with legitimate access to data who abuse their privileges.
While we’d all like to put good faith in our employees to follow company practices, good faith by itself isn’t enough. You need the tools to block and flag suspicious behavior – like downloading tons of files after handing in a letter of resignation.
Third-party risks
Google Docs and Sheets are built for collaboration. Sharing these resources with partners, clients and suppliers probably feels like second nature. But your third party contacts might not have the same security training and culture as you.
Sure, they may have legitimate access to some of your documents – but who’s to say they are using them securely? For all you know, they could be downloading vast troves of data onto unmanaged devices, which puts you at risk of a compliance fine!
Employees make mistakes!
We’ve all sent an email to the wrong person. And many of us have probably forgotten to check the access controls on our Google Docs too. It’s no wonder this is the case. Today, employees are time-pressed, stressed and super busy. In fact, a huge 94% of American workers say they experience stress at their workplace.
Feeling stressed and overwhelmed means employees may forget about simply security procedures. While security is your bread and butter, we have to remember that employees are just trying to do their jobs.
To that end, you need a security solution that does the work for your employees – something that is automated and quiet, running in the background of day-to-day operations to secure data without hampering productivity.
Compromised credentials
Verizon’s DBIR found that 61% of data breaches link back to compromised credentials. Suppose a hacker gets their hands on your employees Google Workspace logins. In that case, the damage they could do is significant – whether it’s deploying malware into your cloud environment or stealing troves of sensitive files.
Unfortunately, access controls won’t do anything to combat credentials compromise. In these instances, hackers use ‘legitimate’ logins to access company data.
There’s a simple way to combat this threat – use multi-factor authentication. This means that, should an employee’s password end up in a breach, a threat actor still won’t be able to access company resources.
What about the rest of these issues?
So, MFA is a good tool for combatting credentials compromise. However, you need a different solution altogether to manage the insider threat, accidental data loss, and third-party risks. This solution needs to go beyond focusing on users and instead focus on securing data.
In essence, you want a technology that can protect data dynamically, ensuring that it is safe from leakage and theft wherever it goes and whoever tries to access it.
Bear in mind that in Google Drive, users are constantly reformatting and uploading data in an unstructured way. So, you need a solution that can identify and protect data no matter its format.
So, what’s the answer?
Drumroll please….
SaaS DLP (Data Loss Prevention) – also known as a Data Exposure Prevention – is the best way to combat these issues and secure data in Google Drive.
We’ve spoken before about why traditional DLP solutions suck. It’s important to understand that cloud-based DLP is another ball game to traditional DLP.
Here’s how cloud-based DLP can help you secure your data in Google Drive seamlessly:
Visibility: Using APIs, cloud-enabled DLP extends data protection outside of the corporate network and directly into SaaS applications like Google Drive, giving you much needed control and visibility over how data is being used and stored – no matter where it travels.
Self-learning: One of the biggest burdens of traditional DLP was constantly updating data classification policies. Security teams were always on the back foot, worried that their updates were too late, and data might have been missed. That’s no longer an issue with cloud-based DLP. These solutions are self-learning with Natural Language Processing (NLP) capabilities and machine learning embedded. They get an idea of the types of data you want to protect and automatically find and secure them – without you having to lift a finger!
Dynamic: Cloud-based DLP incorporates user behavior analytics to flag and block suspicious user behavior, such as a compromised account. This empowers you to keep data safe, even if access controls fail. Here’s what this looks like in practice:
- Identification: Through real-time monitoring, DLP identifies a threat to data security based on predefined policies.
- Sounding the alert: The solution alerts the security team to the threat for visibility.
- Enforcing remediation: At the same time, DLP automatically encrypts the data in question to prevent a data breach.
- Reporting: To meet compliance standards and audit requirements, DLP provides reporting functionality so organizations can prove that data is being used correctly and any incidents have been avoided.
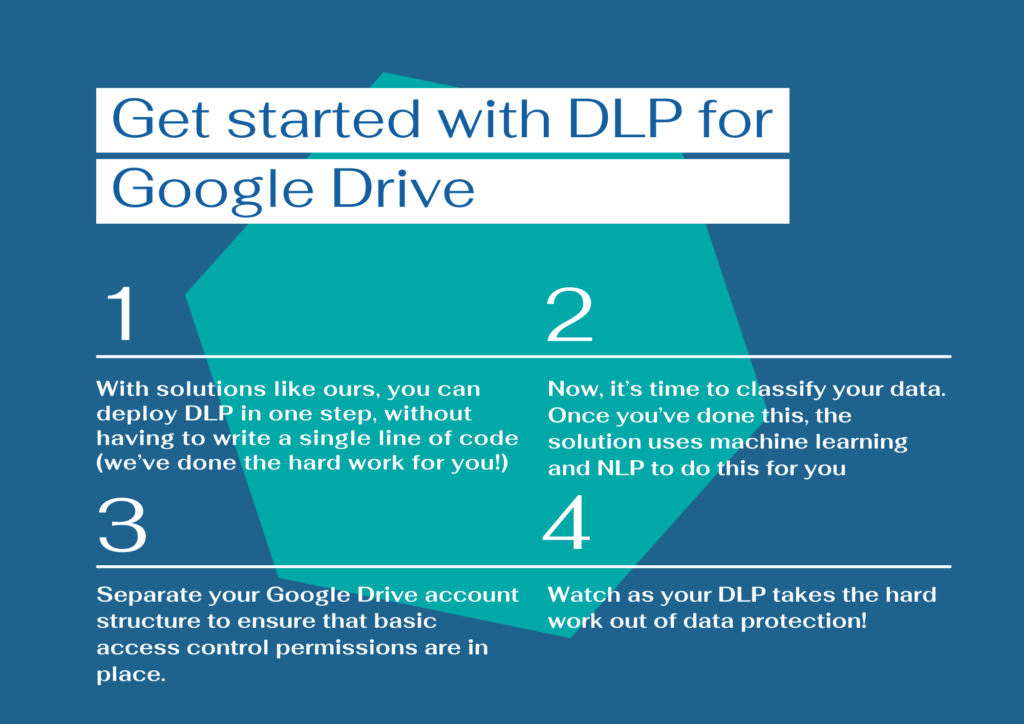
Get started with DLP for Google Drive
That’s the ‘what’ of DLP. Now, here’s an overview of how to get started with your DLP solution:
Step 1 – Click-one installation
Gone are the days when DLP was a cumbersome, time-consuming installation. With solutions like Polymer DLP, you can deploy DLP in one step without having to write a single line of code (we’ve done the hard work for you!)
Step 2 – classify for your data
Data classification is the process of organizing data according to its type, sensitivity, metadata, and perceived value to the organization. It’s an essential building block of DLP. So, once your solution is installed, it’s time to classify your sensitive data.
Once you’ve done this once, the solution uses machine learning and natural language processing to take over-classification for you, so you can focus on high-value tasks.
Step 3 – Simplify your drive structure
It would be best to separate your Google Drive account structure to ensure that basic access control permissions are in place. This helps DLP work as seamlessly as possible, by giving it an understanding of roles and responsibilities within the organization.
Step 4: Let your DLP policies get to work
Watch as your DLP takes the hard work out of data protection. With features like user nudges to promote good security behavior, real-time redaction and audit reporting, you’ll soon get a handle on Google Drive security.