We all know what a traditional phishing scam is, where a cyber-criminal sends a fraudulent email to their victim in a bid to trick them into sharing sensitive information or downloading malware.
Phishing scams are so widespread that most email providers have now installed impressive features that block standard phishing emails. However, just because email anti-phishing solutions are getting better, that doesn’t mean your organization is safe from these attacks.
Phishing in the cloud; the latest, greatest threat
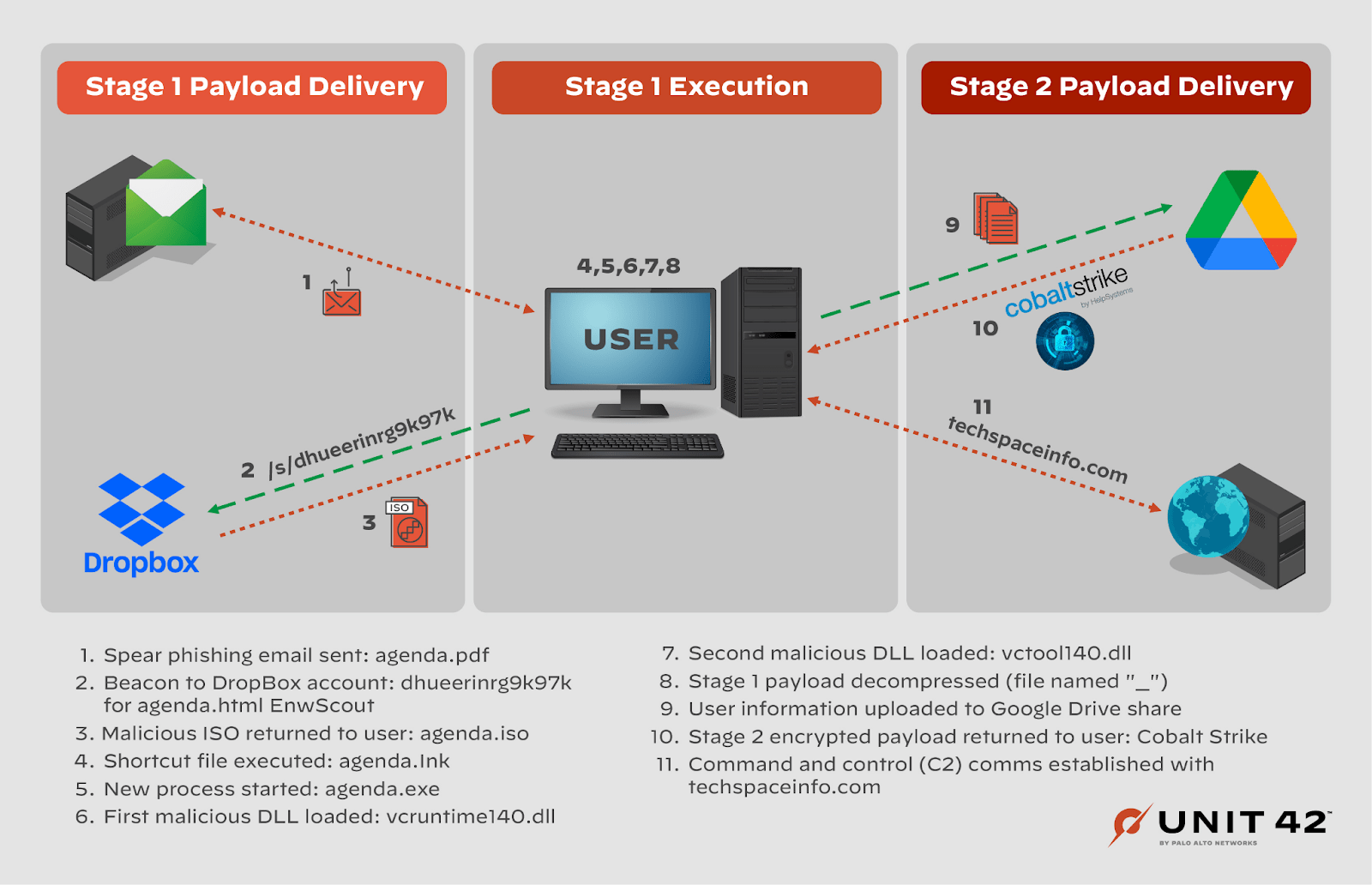
Cyber-criminals can be creative, motivated folk and, recently, we’ve seen a host of crafty phishing attacks that take advantage of cloud services like DropBox and Google Drive, as reported by Unit42 security researchers.
Let’s face it, most companies today use at least one – if not both – of these services. They’re fantastic for collaboration and are generally considered super reliable and trustworthy. However, this is the exact problem. The cyber-attackers responsible for these attacks are exploiting our implicit trust in these well-known, popular cloud services.
Here’s everything you need to know.
Who’s responsible for the phishing campaign using Google Drive and Dropbox?
The group behind this sophisticated phishing campaign has many names: Cozy Bear, Nobelium, APT29 and Cloaked Ursa. Whatever you call the group, it’s what is known as a Russia-based advanced persistent threat (APT) collective.
While it’s not confirmed it’s been suspected for years that Cozy Bear has strong ties with the Russian government, particularly because its attacks tend to target government organizations.
For example, back in 2016, this group hacked the United States Democratic National Committee (DNC). It’s also thought to be responsible for the SolarWinds supply chain incident of 2020.
What is the Google Drive and Dropbox phishing campaign?
Back in May of this year, foreign embassies in Portugal and Brazil started receiving phishing emails with links to Google Drive or Dropbox. Supposedly, the link contained an agenda for an upcoming work meeting.
When recipients clicked the link, they would be taken to Dropbox or Google Drive, where they would then download the agenda to their devices.
However, alongside downloading the file, the victims also downloaded backdoors into their systems, enabling Cozy Bear to deploy malware at any moment. This is because clicking the link deployed Cobalt Strike Beacons through an HTML dropper attachment dubbed EnvyScout.
Why does the Cozy Bear cloud phishing campaign matter?
While Google Drive and Dropbox have both worked to shut down this campaign, this new, devious form of phishing should serve as a warning to all organizations that social engineering attacks are still a potent threat to data security and business continuity.
It also highlights the importance of moving security to the cloud, which appears to be fast becoming the new battleground for cyber attacks.
In the case of Russian nation-state hackers, in particular, all organizations need to be on their guard right now – especially given the current conflict in Ukraine. It’s all too likely that the conflict between Russia and the rest of the world may extend into the cyber sphere at any minute.
How to defend against Google Drive and Dropbox phishing risks
In the case of any form of phishing scam, your best line of defense is education and awareness. Sure, your employees may know to look out for traditional phishing risks, but you also need to keep them up-to-date on the latest type of phishing scams, like this one.
One thing you could do is send out a weekly or monthly cyber bulletin, where you inform your employees on the latest kinds of phishing threats. That way, they know to keep an eye out for emails with Google Drive and Dropbox links that they weren’t expecting.
At the same time, you should complement your training programme with controls to help your people make security-conscious decisions. Our solution, Polymer Data Loss Prevention (DLP), provides in-the-moment nudges in popular apps like Google Drive, Dropbox and Slack.
As well as securing your sensitive data in real-time, our solution will alert employees if an action they’ve tried to take could harm data security. At the same time, our engine blocks the action from occurring, so data security isn’t compromised.
In the case of the Google Drive phishing scam, for example, Polymer DLP will warn your employee against downloading the suspicious file, thus preventing the payload from ever being triggered.