Data breaches are never good news. But, they’re even worse news if the compromised information includes national security data. And, even worse news if your company found out about the breach through the media.
Unfortunately, that’s exactly what might have happened to General Electric (GE), after supposed DARPA (Defense Advanced Research Projects Agency) data stolen from its systems was put up for sale on a popular hacking forum.
Here’s what you need to know.
How did the GE breach happen?
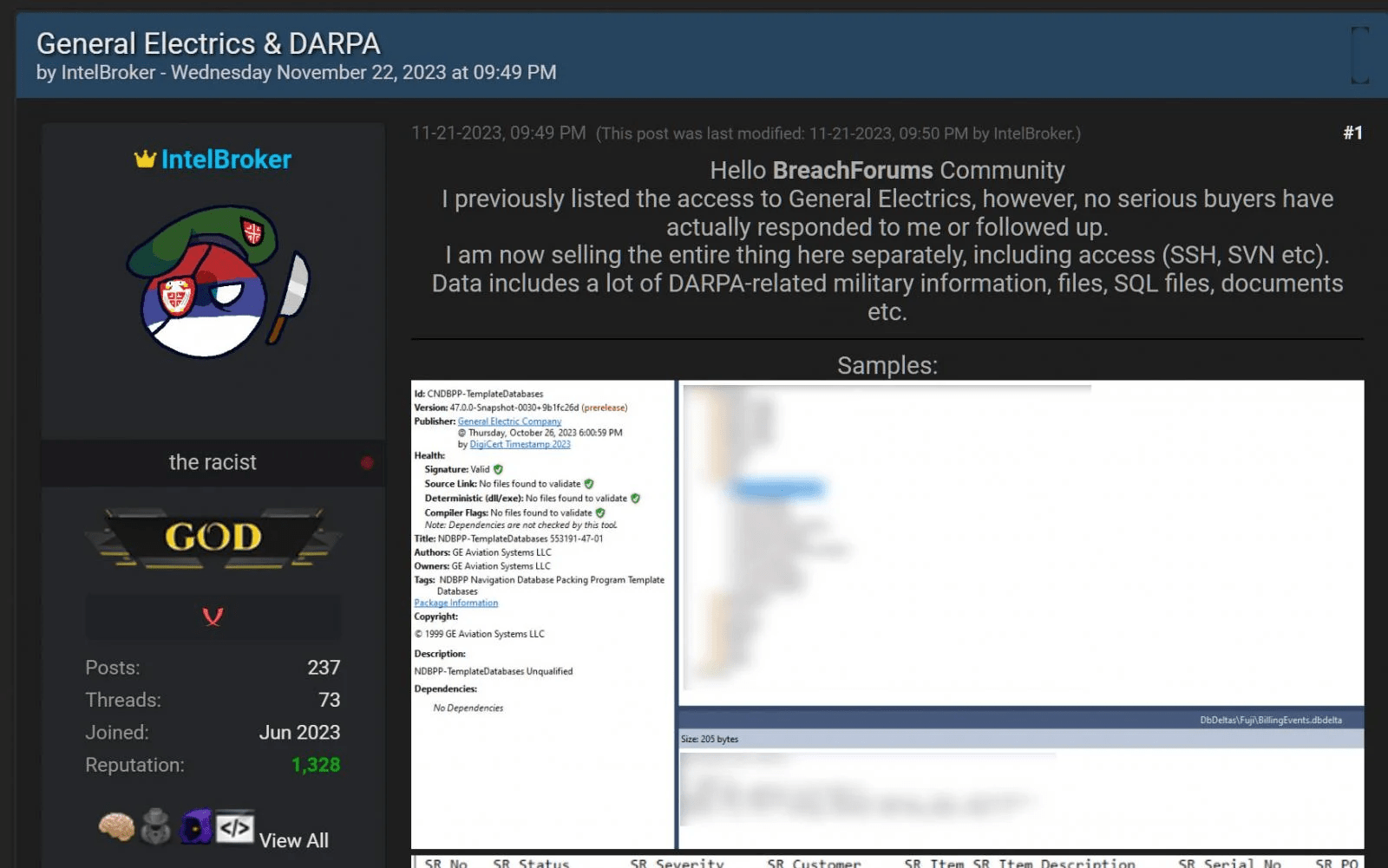
On the 19th of September, a hacker known as IntelBroker posted on the dark web platform, BreachForums, stating they had access to “some development and software pipelines belonging to General Electrics.”
The price tag for this sensitive information? A cool $500, granting buyers access to GE’s GitHub and SVN (sub versioning and revision control).
Interestingly, the initial post didn’t spark much interest; only two replies rolled in, and it seemed like potential buyers weren’t taking the bait. Undeterred, the threat actor took a different tack and announced that they were now selling both network access and the supposedly pilfered data.
In a post on a hacking forum, the threat actor shared, “I previously listed the access to General Electrics, however, no serious buyers have actually responded to me or followed up. I am now selling the entire thing here separately, including access (SSH, SVN, etc).”
The data, as claimed by the threat actor, includes DARPA-related national cybersecurity information, encompassing files, SQL files, and documents.
To prove the validity of the data, the hacker shared screenshots purporting to be stolen GE data, including a database from GE Aviations that allegedly contains information on military projects. However, these screenshots are yet to be verified.
How is GE responding to the breach?
In responses provided to the media, GE has acknowledged the claims made by IntelBroker regarding potential data compromise. The company assured that they are actively investigating these claims and are prepared to take appropriate measures to safeguard the integrity of their systems.
While GE has not officially validated the legitimacy of the reported breach, given IntelBroker’s history, there’s a considerable likelihood that the data theft is indeed genuine.
For example, in March of this year, the hacker successfully acquired personal data from 170,000 individuals by compromising the health insurance marketplace DC Health Link, which is overseen by the DC Health Benefit Exchange Authority (HBX).
This wasn’t the only instance; the threat actor previously targeted the US-based online grocery delivery platform, Weee!, resulting in the exposure of data from 1.1 million customers online.
With such a strong success rate, it could very well be that IntelBroker has successfully compromised GE and stolen national security-related information.
What are the potential implications of the GE data breach?
GE and the US defense arm are collaborating on a number of classified initiatives, including artificial intelligent research and the MIND (Monitoring & Inspection Device) project, which is designed to enhance the network security of crucial information systems. If this information is among the data stolen by IntelBroker, it could undermine important aspects of the US defense program.
On top of that, if this data breach is legitimate, there are also grave concerns about an increased risk of supply chain attacks, where threat actors could use stolen GE credentials to get into the environments of federal agencies and GE partners, leading to many more data security incidents.
Stay tuned
As this data breach continues to unfold, we’ll keep you updated with the latest news. Keep an eye on the Polymer blog to find out more.