Second in our HIPAA blog series, this post takes a closer look at HIPAA’s technical safeguards.
For starters, there are five technical safeguards as outlined in the HIPAA Security Rule.
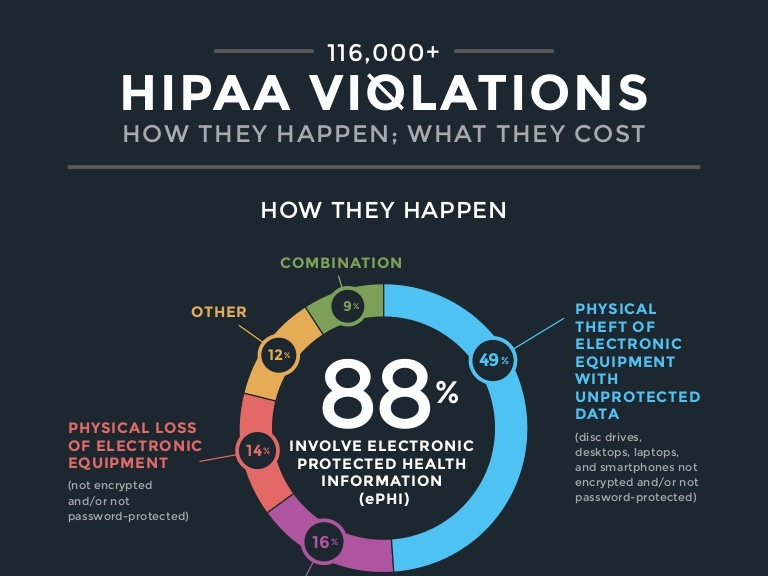
The primary purpose of these safeguards is to help healthcare providers ensure that electronic Protected Health Information (ePHI) is safe from data breach and security-related threats whether the information is at rest or in transit.
HIPAA technical safeguards definition
Technical safeguards refer to the technology, policies, and procedures used to guard electronic Protected Health Information (PHI) and control access to it.
Covered entities and business associates must determine what technical control enables them to best protect ePHI while ensuring HIPAA compliance.
Read on to learn more about the five HIPAA technical safeguard requirements.
#1. Access control
The access controls standard requires a covered identity and business associates to prevent unauthorized access to ePHI.
A health care organization can accomplish this through:
- Unique User Identification such as distinctive employee passwords, usernames, and log in to identify and track a particular user’s activity.
- Implementing an automatic log-off at workstations to prevent unauthorized access to the system.
- Developing emergency access procedures to protect data during emergencies such as power outages or natural disasters.
- Data encryption and decryption for extra protection from unauthorized users or 3rd party SaaS applications.
#2. Audit controls
The audit controls standard requires healthcare organizations and business associates to have a system that enables regular audit trails across hardware and software that contain or use ePHI.
Organizations can accomplish this through:
- Investing in a centralized platform that generates detailed audit reports on devices containing ePHI and assigned users.
- Adjusting and updating policies as necessary.
- Reviewing audit records regularly.
#3. Integrity
The integrity standard requires organizations to implement reasonable measures to protect ePHI from destruction or alteration.
Recent hacking and cybersecurity-related events show that it is easy to compromise data integrity. Moreover, data can become corrupted on its own. An error while saving a file or a glitch in the system, for instance, can cause accidental information change.
The best practice for healthcare organizations to maintain data integrity is to store all PHI data offsite for five to six years from the creation date.
#4. Authentication
One of the most critical measures to protect ePHI for healthcare providers and patients alike is to verify a user’s identity before accessing data. The authentication standard confirms that individuals seeking access to ePHI are who they claim to be.
There are several ways to accomplish this requirement, including:
- Biometric patient identification.
- Two-step authentication.
- Phone or voice authorization.
- Specialized software with e-signature functionality.
#5. Transmission security
This standard requires organizations to take extra caution when transmitting information electronically.
The thing is, data in transit, even between authorized parties, is prone to vulnerabilities. Besides, one of the parties may not secure the information as well as the other. Further, there might be glitches and weaknesses in the transmission networks.
With all these risks, cybercriminals can intercept information leading to data loss, even without hacking the organization.
You can accomplish transmission security through:
- Encrypting ePHI as needed without corrupting the data’s integrity.
- Tracking authorized users via audit controls.
- Evaluating personal emails and devices.
Side note – Organizations should use encryption tools as intended. Therefore, encryption software used by both the sender and receiver must be the same or compatible.
Manage HIPAA compliance with Polymer DLP
With Polymer Next Generation Data Loss Protection (DLP), you can streamline compliance management tasks while preventing malware and phishing attacks during data transmission.
Our customizable solution allows you to meet your organization’s needs, business associates, and patients in a flash through one-click installation.
Click here to get started with Polymer DLP today.