If your organization works with the Department of Defense in the US, then you need to know about CMMC (Cybersecurity Maturity Model Certification).
What is CMMC?
CMMC was initially launched in 2020. It’s a cybersecurity framework with different tiers that are loosely based on established standards, such as NIST and DFARS. Organizations that work with the DoD must comply with the framework, and there are more stringent requirements for companies that handle Controlled Unclassified Information (CUI) and Federal Contract Information (FCI).
The DoD defines FCI and CUI as follows:
“FCI is information, not intended for public release, that is provided by or generated for the Government under a contract to develop or deliver a product or service to the Government, but not including information provided by the Government to the public (such as that on public websites) or simple transactional information, such as that necessary to process payments.”
“CUI is information the Government creates or possesses, or that an entity creates or possesses for or on behalf of the Government, that a law, regulation, or Government-wide policy requires or permits an agency to handle using safeguarding or dissemination controls.”
While organizations may groan at the idea of having to comply with another standard, it’s easy to understand why the DoD has launched CMMC.
The DoD stores and generates vast amounts of sensitive data. If this data were to get into the wrong hands, it could be used as the basis for acts of cyber-terrorism or cyber-warfare.
Recent hacks like the Kaseya ransomware attack and SolarWinds breach highlight that today’s digital supply chains are often the foundation for successful cyber-attacks.
With CMMC, the DoD aims to better control and secure its extensive supply chain.
Who needs to attain CMMC Compliance?
Companies that work with the DoD either as contractors or subcontractors will need to achieve CMMC certification.
CMMC may also apply to companies that work with DoD contractors in instances where the company has access to a contractor’s data, systems or infrastructure.
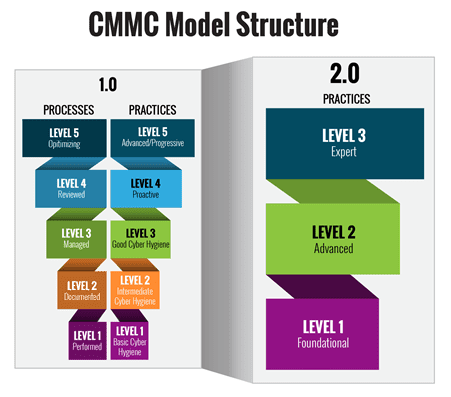
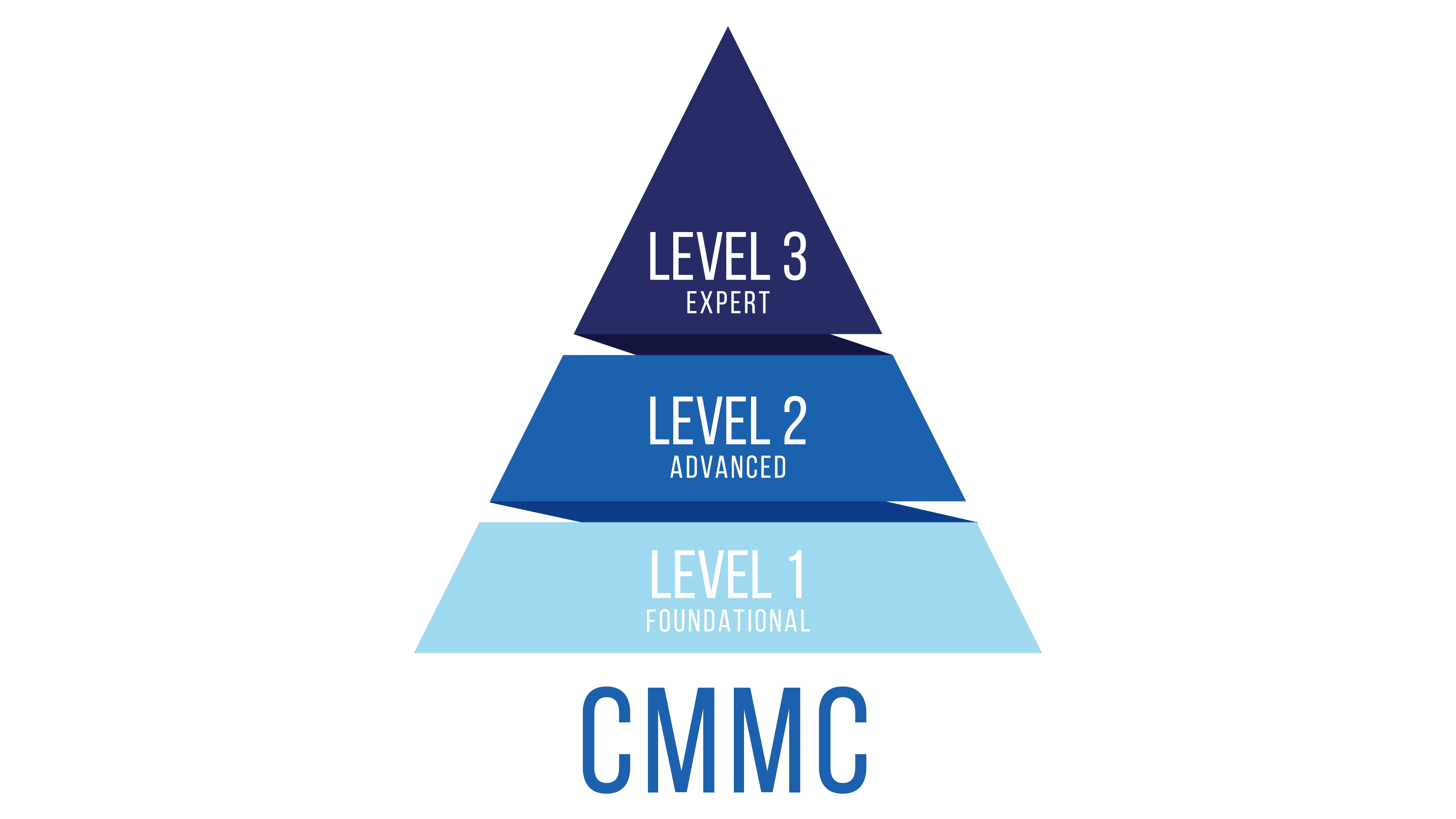
What are the levels of CMMC compliance?
When CMMC first launched, there were five levels. However, in November 2021, the DoD released an update on the CMMC – as it was previously viewed as too complex and confusing.
The new version of CMMC closely follows the principles of NIST 800-172. Here’s more on the three levels of CMMC compliance requirements.
Level 1: Organizations will need to meet basic cyber security hygiene by implementing 17 safeguarding controls as noted in FAR 52.204-21, which is a preexisting clause in DoD contracts. These controls fall into six domains, which are: Access Control, Identification and Authentication, Media Protection, Physical Protection, System and Communications Protection and System and Information Integrity.
Level 2: Organizations will need to meet the requirements of NIST SP 800-171. These controls already exist under DFARS 252.204-7012 clause.
Level 3: Organizations will need to meet a subset of requirements within NIST SP 800-172 – although these are yet to be defined. It’s presumed these requirements will help companies protect against advanced persistent threats (APTs).
It’s worth noting that level 1 organizations – which don’t come into contact with CUI data – will be able to self-certify. Organizations that need to meet Level 2 or Level 3 will need to seek third-party certification.
According to the DoD’s CISO, around 200,000 companies will self-assess to Level 1, 40,000 will need to certify to level 2, and roughly 500 will need to attest to level 3.
What is the CMMC compliance deadline?
Right now, there’s not much information out there about CMMC 2.0, but we can expect more resources and advice to come out in the coming months as the DoD formalizes the certification. Keep an eye out on our blog, as we’ll release a CMMC compliance checklist to help you meet your CMMC requirements.
Even as we wait for more information, we advise organizations to be proactive about CMMC compliance. To that end, you should start working towards the controls in NIST SP 800-171 as a matter of priority.
Next steps
If you’re looking for CMMC compliance support, we can help. At its core, this security framework is concerned with protecting critical data from unauthorized usage and access.
So, to protect critical data, you need to take a data-centric, zero-trust approach to security. That’s where we come in. We can help you meet CMMC compliance requirements through our next-gen DLP platform data exposure prevention, which enforces cloud compliance policies and protects sensitive data to maintain a compliant posture.