SaaS applications like Office 365, Salesforce, Slack, Zoom, and Google Workspace all come with default security settings, which are designed to make deployment easy for customers.
If you’re yet to change these default security settings, then you’ve potentially got a problem on your hands. You see, default permissions and security settings are typically set with a low barrier for entry.
Cloud providers expect you to securely configure your applications – but many companies don’t realize that this is their responsibility. It’s no wonder that 99% of organizations have cloud misconfigurations they aren’t aware of. Too many enterprises think that default settings are automatically secure – but they’re not.
Let’s take a look in more detail at this issue.
Why are default settings a security risk?
Default security settings are a risk for both software and hardware products. Manufacturers and service providers roll out their products and applications with default configurations to maximize usability. They want to make it easy for their customers to get started. These default settings are all about efficiency.
What they’re not about is security. Accepting default settings often leaves gaping security gaps that, in the long-term, cause data leakage and data theft.
You might think: isn’t the cloud provider responsible for securing the cloud? Here’s the sticking point. If you think your SaaS provider is responsible for securing the cloud, you’re kind of right but also kind of wrong.
Basically, the cloud operates under what’s known as a shared responsibility model. This means that responsibilities are divided between the customer and the cloud provider. The division of these duties is dependent on the type of cloud computing model you use.
For the sake of this article, we’re focusing on SaaS. In this environment, the cloud provider is responsible for securing the underlying infrastructure of the application, but it’s up to you to secure all of the data within the application and to implement proper access controls.
This, of course, is where default security settings come into play. Under the shared responsibility model, it’s up to your company to make sure that you’ve implemented compliant, secure access controls and data protection settings. If you don’t you’ve essentially enabled a cloud misconfguration.
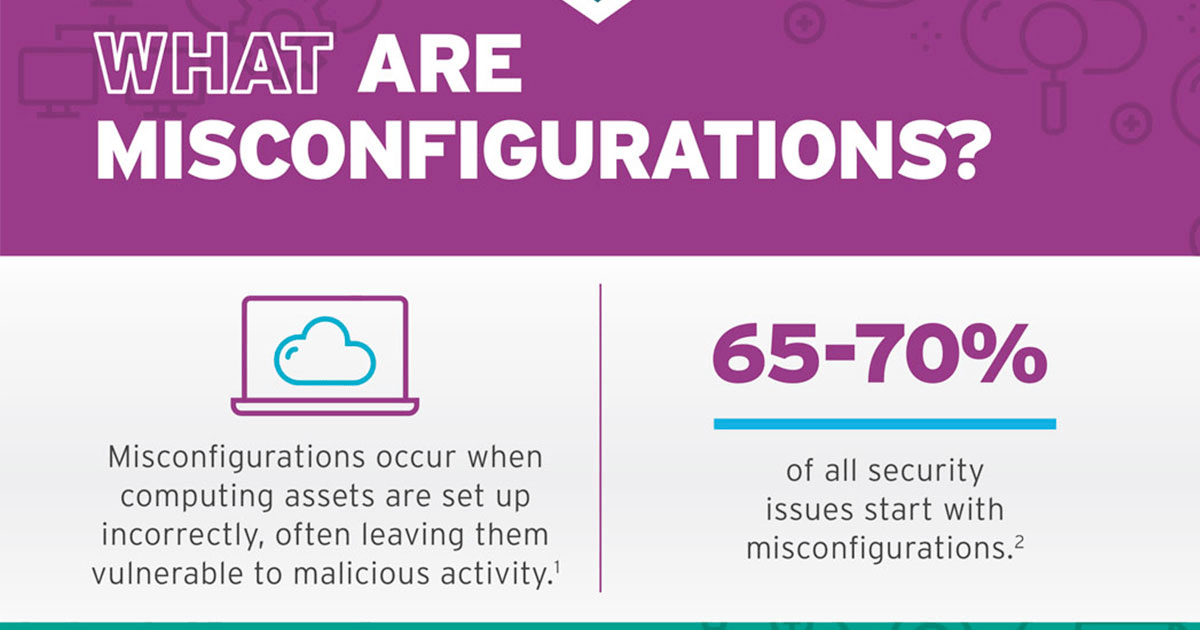
To make things a little more complex, implementing secure configurations isn’t exactly easy. Every SaaS application has its own workflow, interface and policies. Plus, cloud environments are dynamic. They’re constantly shifting and growing. For even the most experienced security architect, keeping on top of configurations can be overwhelming.
In fact, even the head of global security programs for Amazon Web Services said that his biggest concern is customers’ applications not being properly configured for security.
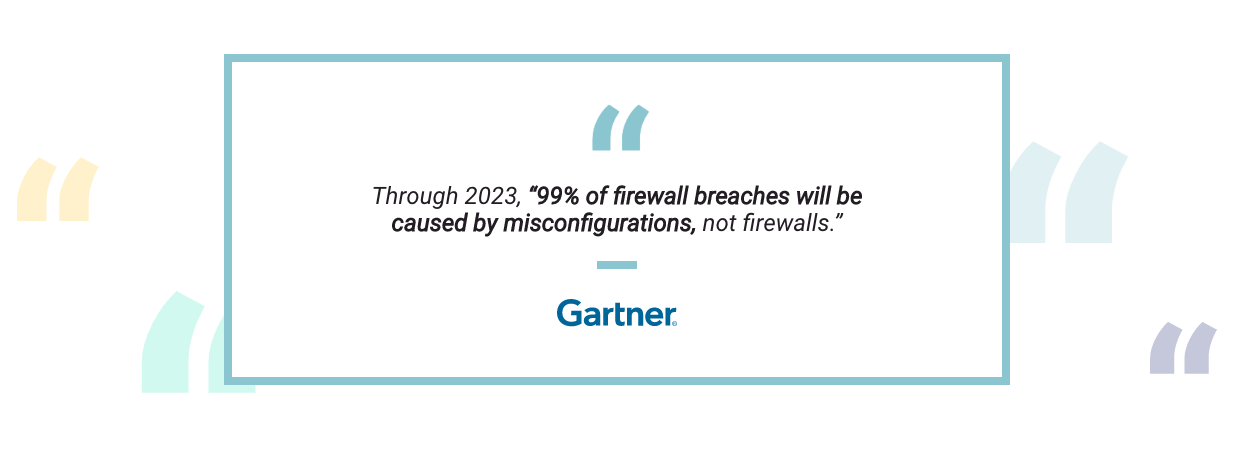
As a result, it’s no wonder that Gartner predicts that, by 2025, 99% of cloud security breaches will be the customer’s fault. Keeping on top of default settings and implementing correct configurations is undoubtedly a tough job unless you have the right tools to help (more on that below!)
What are some common cloud misconfigurations?
So far, we’ve talked about misconfigurations in a very abstract sense. To help you understand what these look like in practice, here are some of themost common insecure default settings to watch out for. Note that this list is far from exhaustive. There are a host of default SaaS settings out there – many of which put sensitive data at risk.
Logging: Many providers – for example, AWS CloudTrail – offer solutions to help with logging and auditing of events within the cloud environment. However, these solutions are not enabled by default and you have to pay a little extra to access them. This means that many administrators won’t know what’s happening in the cloud environments – including whether data has been stolen or misused.
Authorization: Too often, SaaS services offer very relaxed authorization mechanisms by default. The average user may even have administrative privileges, for example. Companies must proactively implement the principle of least privilege across their SaaS applications and correctly configure their access controls.
Network Configuration: The misconfiguration that is most often behind data breaches is the accidental exposure of private cloud environments to the public internet. Amazon’s S3 buckets, in particular, have been notorious for this. There was also the MS PowerApps fiasco. Essentially, you should never assume that your cloud environments are set to private by default. You will definitely need to triple check that only authorized, eligible users can access your instances and applications.
What will happen to my company if I suffer a cloud misconfiguration?
A whole host of things could happen to your company if you suffer a cloud misconfiguration. The severity of the incident will depend on a few factors, including the type of data and whether cyber-criminals were involved.
Here are the most significant risks to know about:
Leaking of sensitive data
If you have incorrect access controls or your cloud instance is exposed to the public internet, you could inadvertently leak sensitive data. For organizations in highly regulated industries like healthcare and finance, there could be huge financial and compliance repercussions for this kind of incident.
The same goes for companies that accidentally leak customer data. Under regulations like the CCPA and GDPR, there are severe fines for failing to properly secure PII.
Moreover, it’s not just leakage you have to worry about. It’s theft too. Data is super lucrative. Hackers can use it as the basis for fraud or sell information on the dark web for cryptocurrency. A misconfiguration is one of the easiest ways for these criminals to exfiltrate sensitive data – and you won’t even know until it’s too late.
Operational downtime and disruption
Sometimes, getting into your cloud environment is just the start for malicious actors. Once they’re in, they’ll think strategically, taking their time to ensure they can deliver the most disruption.
Ransomware attacks are a great example of this. These attacks encrypt access to your files until you pay a hefty ransom, often taking companies offline for days and weeks at a time.
It’s scary to think that one small cloud misconfiguration can lead to a widespread ransomware attack, but this is very much the reality of today’s digital business world.
How to mitigate cloud misconfiguration risks
Companies don’t have to be sitting ducks when it comes to default security settings. You can implement proactive changes to reduce your risk.
Firstly, before allowing a third-party application to be added to your workspace, diligently evaluate the app’s default permissions. Be sure to immediately adjust any bothersome permissions, such as default access to files, messages, channel names, profile information, and the like.
However, as noted above, managing permissions is, well, difficult. So, don’t just lean on your IT administrators to shoulder the burden. Support them by using the following tools:
Invest in SaaS-based DLP: Using APIs, SaaS-enabled DLP extends data protection outside of the corporate network and directly into SaaS applications like Google Drive, giving you much needed control and visibility over how data is being used and stored – no matter where it travels.
Our solution also incorporates user behavior analytics to flag and block suspicious user behavior, such as a compromised account. This empowers you to keep data safe, even if access controls fail.
Plus, you don’t need to worry about overburdening your IT team with yet another security solution. Polymer’s engine is self-learning, meaning it protects sensitive data from misconfigurations with little to no engine. Everything is automated and logged for you!
Train your people: In an ideal world, misconfigurations wouldn’t even happen in the first place. At their core, these issues are the result of human error. This is why training is paramount. By educating your people on the tools they use – and how to use them securely – you can drastically reduce your chances of error. By training, though, we don’t mean annual away days. Our solution, for example, integrates training directly into your employees’ workflow, helping them to learn about security on the job. For example, in Google Drive, default sharing of public links is countered by framing users into private-only shares.
Audit: Last but not least, you should get into the habit of regularly auditing your cloud environment to discover any misconfigurations that slipped through the net.