A couple of months ago, we wrote about CMMC 2.0, the second iteration of the Department of Defense’s Cybersecurity Maturity Model Certification. The revamped CMMC 2.0 is meant to be easier to implement for small and medium-sized businesses, so that contractors and suppliers of all sizes are able to meet the DOD’s cybersecurity requirements.
If your company needs to meet CMMC 2.0 by 2025, then there’s a few things you need to know. At the moment, the regulation is still in flux. The DoD has stated that it is “pursuing development of acceptance standards between CMMC and other cybersecurity standards and assessments.”
In other words, CMMC 2.0 can’t – and shouldn’t – be viewed in isolation. Your company will likely have to consider other standards that have interweaving requirements. In particular, we’re hearing increasing chatter about the links between CMMC 2.0 and the Federal Risk and Authorization Management Program Plus (FedRAMP+).
Here’s everything you need to know.
What is CMMC 2.0?
CMMC 2.0 is a cybersecurity framework that builds on well established cybersecurity standards like NIST and DFARS.
Organizations that work with the DoD must comply with the framework, and there are more stringent requirements for companies that handle Controlled Unclassified Information (CUI) and Federal Contract Information (FCI).
CMMC may also apply to companies that work with DoD contractors in instances where the company has access to a contractor’s data, systems or infrastructure.
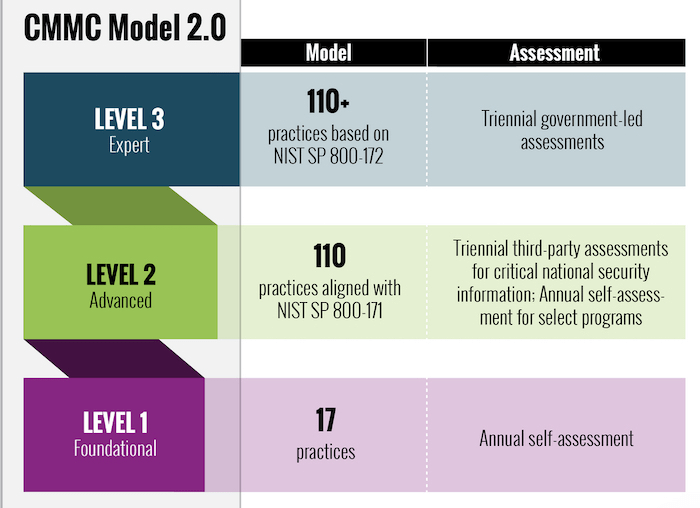
CMMC closely follows the principles of NIST 800-172 and its compliance requirements are split into three levels.
Level 1: Organizations will need to meet basic cyber security hygiene by implementing 17 safeguarding controls as noted in FAR 52.204-21. Level 1 companies can self-certify.
Level 2: Organizations will need to meet the requirements of NIST SP 800-171 and seek third-party certification. These controls already exist under DFARS 252.204-7012 clause.
Level 3: Organizations will need to meet a subset of requirements within NIST SP 800-172 – although these are yet to be defined – and seek third-party certification. It’s presumed these requirements will help companies protect against advanced persistent threats (APTs).
Major updates for cloud services are upcoming
As organizations start to roll out their CMMC compliance programs, we highly advise them to consider their use of third-party cloud services – things like Slack, Teams, Dropbox, Google Workspace and more.
Of course, we already know that the CMMC flow down process requires companies to consider data security requirements in the software supply chain. However, we also expect that organizations that store, transit or process CUI and FCI will need to meet FedRAMP+ too – and so will the cloud services they use.
This is vital for DoD contractors to understand. We’ve seen many contractors and companies fail to realize that their cyber security responsibilities extend to third-party cloud services.
These organizations need to familiarize with the cloud’s shared responsibility model and the role they must play in keeping sensitive data safe when making use of external service providers.
If they don’t, they may inadvertently put classified information at risk, leading to data leakage, data breaches or even potential acts of cyber warfare should certain pieces of information end up in the wrong hands.
While no announcements have yet been made by the DoD, we highly advise organisations to gain a deeper understanding of FedRAMP+ and its relationship with CMMC 2.0.
FedRAMP+: Get to know the Impact Levels
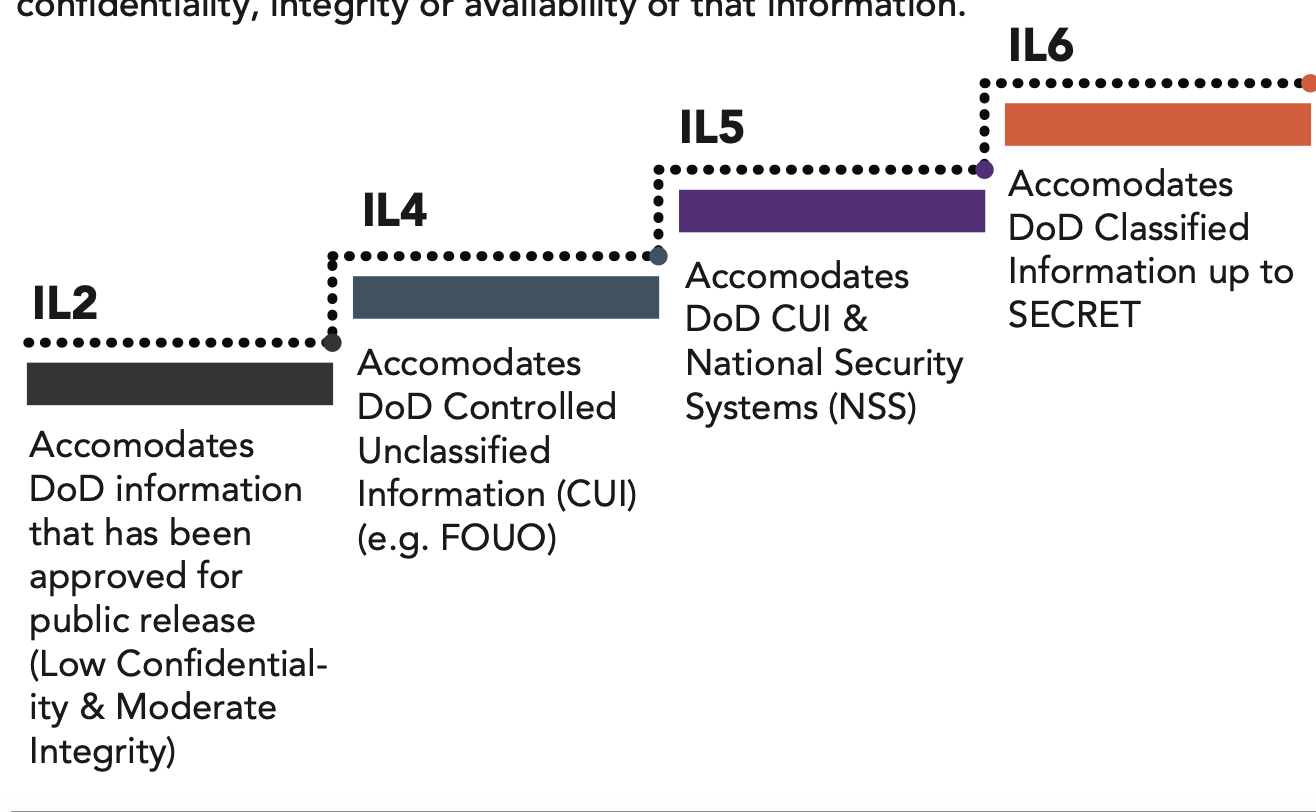
FedRAMP+ outlines security requirements for cloud products and services used by the DoD.
It features four information Impact Levels (IL), with escalating requirements based on factors like:
- The sensitivity of the data stored in the cloud – from public to highly classified
- The potential fallout should this data be corrupted, lost or stolen
Below is an overview of each of these impact levels in more detail.
What does IL4 & IL5 designation mean for companies using SaaS?
DoD IL2 is the lowest, least challenging authorization level, so we won’t spend any time on it here. The thing your company will likely need to think about – if you handle CUI – is IL 4 and IL5.
As shown in the graph above, IL4 and IL5 relate to CUI and the cloud. While the IL framework is aimed at cloud service providers, your company will have a responsibility to appropriately categorize your data, so that only authorized information enters the relevant hosting environment. For example, classified information would not be allowed in IL4.
So, even if you work with a cloud provider that meets FedRAMP compliance, it’s your responsibility to ensure that the environment, data and applications you use are correctly configured to adhere to FedRAMP+ and CMMC.
How to meet DoD compliance requirements in the cloud
While the climb to FedRAMP+ and CMMC 2.0 compliance might seem steep, the tools exist to help you keep sensitive information safe in cloud environments. In fact, security vendors created SaaS DLP for this exact reason: to help organizations find, manage and secure their information across cloud environments.
A good DLP solution will empower you to achieve cost-effective, seamless data security and compliance across cloud applications, making it easy to meet DoD security standards.
Best-in-breed solutions are built with auditing and reporting in mind. Our DLP platform, for example, is a simple plug-and-play solution with in-built templates that automatically enforce cloud compliance policies and protect sensitive data to maintain a compliant posture.
On top of this, we help you to build a culture of compliance. Using machine learning, our solution becomes your in-house compliance trainer, notifying users of compliance violations so that they will learn from their errors, while auto-enforcing remediation to keep data safe.
Ultimately, as the government continues to ramp up its focus on data security, all DoD contractors will need to invest in improving their cyber security posture. Under the shared responsibility model of the cloud, this means putting an increased focus on keeping data safe in SaaS applications.
Don’t wait until the last minute to start your compliance journey. Start today – and you’ll not only ensure your compliance with DoD mandates, but you’ll reduce your likelihood of suffering data breaches too.