Data security leaders are navigating a new era. Digital transformation, SaaS adoption, and the rise of AI have dramatically expanded the enterprise attack surface. Sensitive data is moving faster than ever, often outside traditional guardrails. Security and compliance teams are under pressure to protect company data without slowing down collaboration and innovation. That’s why we’re […]
Data security news & resources
Malicious prompt injections: The AI threat CISOs can’t ignore
Generative AI is threaded through almost every enterprise workflow today — from daily tasks like asking ChatGPT a question, to powerful copilots embedded in SaaS like Microsoft 365, Salesforce, or Slack. That convenience creates a new attack surface: malicious prompt injections (MPIs). MPIs trick AI systems into ignoring rules, running hidden code, or leaking data. […]

Are identity tools failing SOC operations?
Data security breaches aren’t slowing down. From exposed AWS buckets to credential-stuffing attacks on SaaS platforms, compromised identities remain the weakest link in enterprise security. According to Verizon’s 2025 Data Breach Investigations Report, stolen credentials were the initial entry point in 22% of breaches, and a staggering 88% of basic web application attacks involved the […]

How to mitigate the security risks of frontline SaaS apps
A digital transformation is taking place on the frontline. Employees who were once underserved by enterprise technology are now gaining access to modern SaaS tools that drive efficiency, collaboration, and real-time decision-making. For organizations, it’s a powerful opportunity to unlock greater productivity at scale. But it also introduces new risks. Each new endpoint expands the […]
Misconfigured server exposes PII of millions of European citizens
A misconfigured cloud database has exposed hundreds of millions of sensitive business records linked to individuals and organizations in Sweden, in what experts are calling a serious lapse in data security. The exposed server, which used the open-source search and analytics engine Elasticsearch, was discovered by cybersecurity researchers who found it accessible without any authentication. […]
Do you need cyber insurance in 2025?
We’re only halfway through 2025, and there have already been over 12,000 publicly disclosed data breaches. From small brick-and-mortar businesses to multinational tech companies, it’s clear that no organization is immune to a cybersecurity incident. Preparation is key—and one increasingly vital part of shoring up against cyber-attacks is cyber insurance. In this article, we’ll explore […]

Getting started with AI security posture management
Organizations are charging full-speed into AI adoption—eager to boost efficiency, outpace competitors, and unlock entirely new ways of working. For business leaders, the mandate is clear: move fast, or get left behind. But for security teams, the pace is less exciting and more alarming. Every new AI model introduces risks: more potential for data exposure, […]
Qantas data breach exposes six million customers
Qantas is warning millions of customers that their personal data could be exposed after a cyber attack hit a third-party platform used by one of its offshore contact centers. Here’s everything we know about the breach so far. How did the breach happen? Qantas says it detected unusual activity on the affected third-party system earlier […]
The agentic SOC: A near reality?
Burnout has been rife within the cybersecurity sectors for years. But, this year, it seems many SOC analysts have reached breaking point. With 71% reporting burnout and 64% considering leaving the cybersecurity field altogether, it’s clear that something has to change in the security operations center (SOC). The question is…what? Most CISOs are no stranger […]
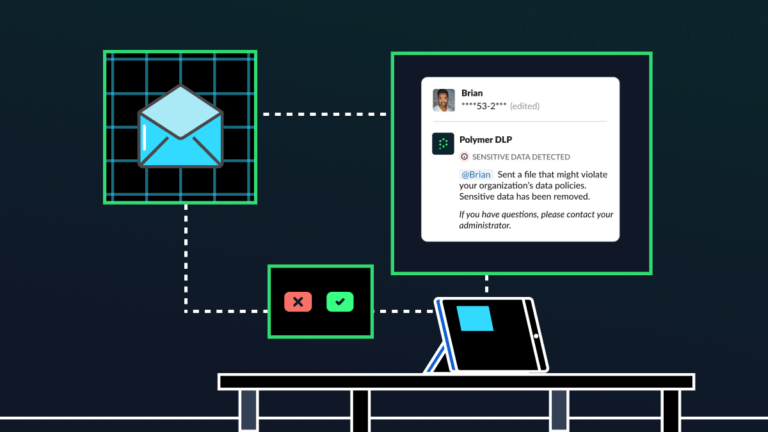
Human risk management: The key to a culture of cybersecurity
All employees make mistakes—whether that’s a typo in an email, sending a document to the wrong person or missing a deadline. Some mistakes, though, have greater consequences than others, especially when it comes to cybersecurity and compliance. Sending a sensitive document to the wrong recipient, for example, can be an immediate data breach and compliance […]
Runtime data security vs DSPM
In the alphabet soup of cloud security tools, few acronyms have risen faster—or with more promise—than data security posture management (DSPM). Touted as a cure-all for sensitive data exposure, DSPM promises deep visibility into cloud environments. But as many CISOs have found, visibility alone isn’t enough. DSPM might show you where the problems are—but it […]