Work-from-home security risks within collaborative and productivity apps such as Slack is being under appreciated.
Security failures on platforms like Slack may not manifest directly as ‘platform breaches’ but indirectly through leaks of files downloaded and data shared that is then saved locally. Data breaches, malware infestations, brand or credibility damage have occurred when vulnerable end points within organizations are exposed through user errors and incorrect security setup. SaaS products being used at home are one of those vulnerable end points.
All good security protocols could fail an un-secure WIFI or home computer without sufficient controls. Slack users may leaves sensitive data, files, messages, and sensitive information open to cyberattacks.
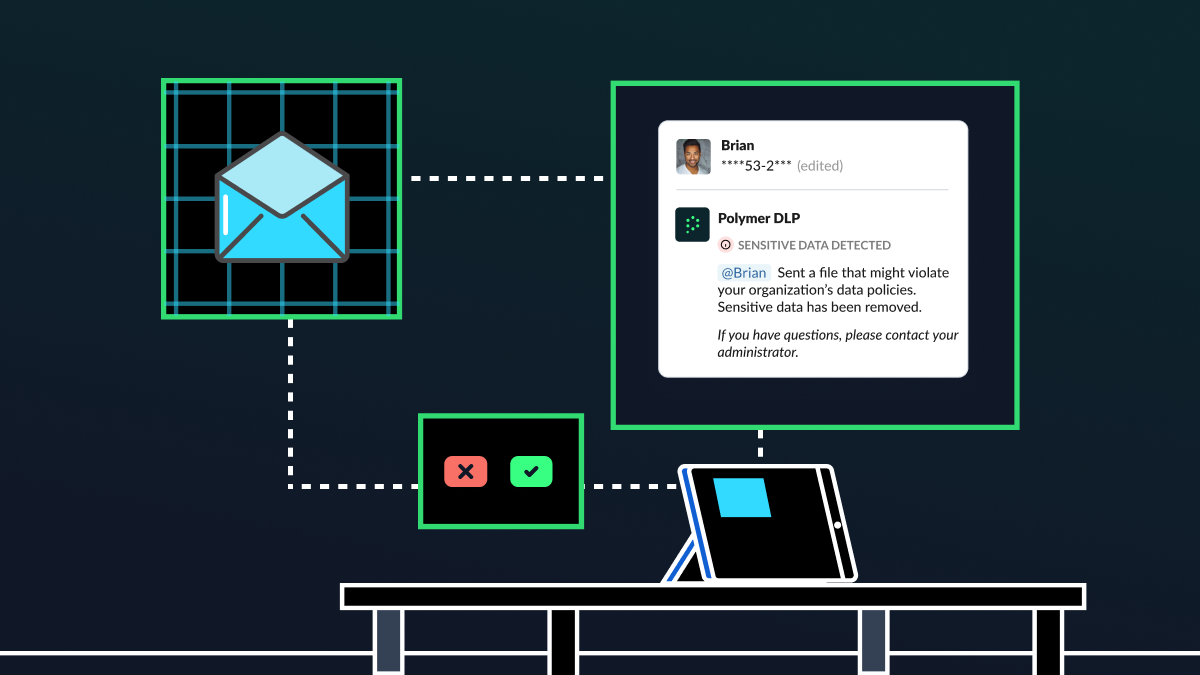
Organizations must do more to promote l have the power to ensure the best practices in using Slack and ensuring reduction of PII or sensitive data in public channels.
Third-party apps
Around 43% of all third party apps in the approved Slack App Store can read messages within chats. The sensitive information within these channels can be accessed in a breach of any of your partners.
Automated account takeovers (ATOs)
In March 2020, following the initiation of much remote work, a profound vulnerability was discovered on Slack, which had the potential to provoke automated account takeovers (ATOs) and could ultimately lead to significant data breaches.
As described by “a HackerOne bug-bounty report, a[n] HTTP Request Smuggling bug, in a proof-of-concept, was used to force open-redirects within Slack, leading users to a rogue client outfitted with Slack domain cookies.” Consequentially, when users attached to this rogue client, this malicious actor had the opportunity to gather session cookies which could eventually be used to perform a — potentially automated — account takeover.
And after mastering a login or password recovery workflow, cybercriminals and attackers commence their attack on the accounts with credentials that they are certain are authentic. These automated attacks employ the use of bots in order to take control of the greatest number of accounts and are omnipresent across countless collaboration apps.
Phishing attacks and malware infestations
Through collaboration platforms like Slack, attackers can make a variety of cyberattacks for numerous purposes. Similar to email, Slack’s messaging element acts as a prime target for cyberattacks, often preyed upon via phishing attacks and malware infestations carried out through basic attachments and links. In leveraging stolen login information or ushering strong-arm credential-stuffing attacks, external hackers have the capability of achieving access to highly sensitive data stored within Slack messages/chat rooms.
As a result, this sensitive data may become compromised and utilized for malicious intent, possibly attacking addition in-company targets in the process. Moreover, these rogue attackers may even impersonate employees within Slack chat rooms or threads, sending through malicious content that is seemingly unsuspicious and can easily make its way onto another employee’s device or account.
Direct-message vulnerability
The transition to remote work that countless business worldwide have had to make in response to growing concerns surrounding COVID-19 have not only changed the way in which work gets done, but it has also altered company comradery and culture. Conversations intended to be private often remain so when individuals are face-to-face. This isn’t always the case when these conversations make their way onto collaborative apps.
Although private on the surface, Slack Direct-Messages may be accessible to the intended recipient, as well as to executives, senior-level staff, and the HR department if a company subscribes to one of Slack’s paid models. Although applicable laws must still be followed for those utilizing one of Slack’s paid options, the contents of DMs are far from secure, so conversations not for the ears of everyone in the company should be avoided while using the platform.
Private data retention
Due to the fact that Free Slack workspaces prevent users from limiting the amount of data that the application can retain, Slack effectively never loses access to any data shared through its chat rooms. Only a user with a paid membership has the ability to access messages beyond the 10,000 message limit enacted by Slack.
Gennie Gebhart, Associate Director of Research for the Electronic Frontier Foundation, simplifies this issue, clarifying that users “don’t have the ability to delete… or edit [old messages], but they’re still hanging around on Slack servers.” This means that the messages, files, documents, photos, etc. that have become unavailable to the user who sent them or who was among the intended recipients remain available to Slack, as well as to hackers, attackers, and law enforcement.
Cybersecurity threats disguised as add-ons
Offering users with an abundant software library of add-ons, Slack enables individuals to streamline their accounts to boost efficiency and time management. Slack empowers its add-ons to access channel data. However, this can leave a channel open to cybersecurity threats, as an attacker can create a seemingly appealing add-on that, once installed, has the power to reveal all channels within the user’s workspace.
Conclusion
Unfortunately, the strength that Slack offers in its ease of collaboration and connection doubles as its primary weakness. Slack may be a low-hanging fruit for malicious attackers on the hunt for sensitive data. Through the collaboration that occurs between users via Slack, the data, files, messages, attachments, links, etc. that are shared are left relatively out in the open. Although the features supplied by Slack have enabled companies to streamline their shift to remote work, there are certainly some cybersecurity vulnerabilities posed by the platform. For this reason, it is crucial that businesses developer additional data security measures when utilizing collaborative apps to help ensure the safety of their delicate data.
References
Grauer, Yael. “Slack, Zoom, Google Hangouts: Are Your Remote Work Apps Spying on You?”
Medium, OneZero, 23 Mar. 2020,
onezero.medium.com/slack-zoom-google-hangouts-are-your-remote-work-apps-spying- on-you-cf1e33809cf7.
Seals, Tara. “Beyond Zoom: How Safe Are Slack and Other Collaboration Apps?” Threatpost
English Global, 6 Apr. 2020,
threatpost.com/beyond-zoom-safe-slack-collaboration-apps/154446/