If politicians use it, then why shouldn’t enterprises? We’re talking about nudging – a form of behavioral science. The theory behind nudging is that, by presenting information in a new way, you can gently influence people towards making better choices.
The concept rose to prominence in the Obama administration, when Obama made Cass Sunstein, the author of the bible on nudging, the head of The Office of Information and Regulatory Affairs, tasked with using nudges to improve regulations. Together, for example, they used an opt-out approach of being an organ donor, instead of opt-in, to boost the number of registered organ donors in many states.
As explored in a previous blog, nudging’s benefits extend beyond the political realm. The theory can be applied to corporate culture – specifically, to prevent insider data breaches and leaks.
But how exactly does nudging work in the enterprise, and how can you use it to your advantage?
Understanding fast and slow thinking at work
Successful nudging techniques are based on a positive manipulation of people’s actions. They either make people stop and think, so they can choose a better outcome or, as with the organ donor example, rely on people’s tendency to take the easy option.
This is all about the brain’s two systems: System 1 and System 2, as popularized by Nobel prize winner, Daniel Kahneman.
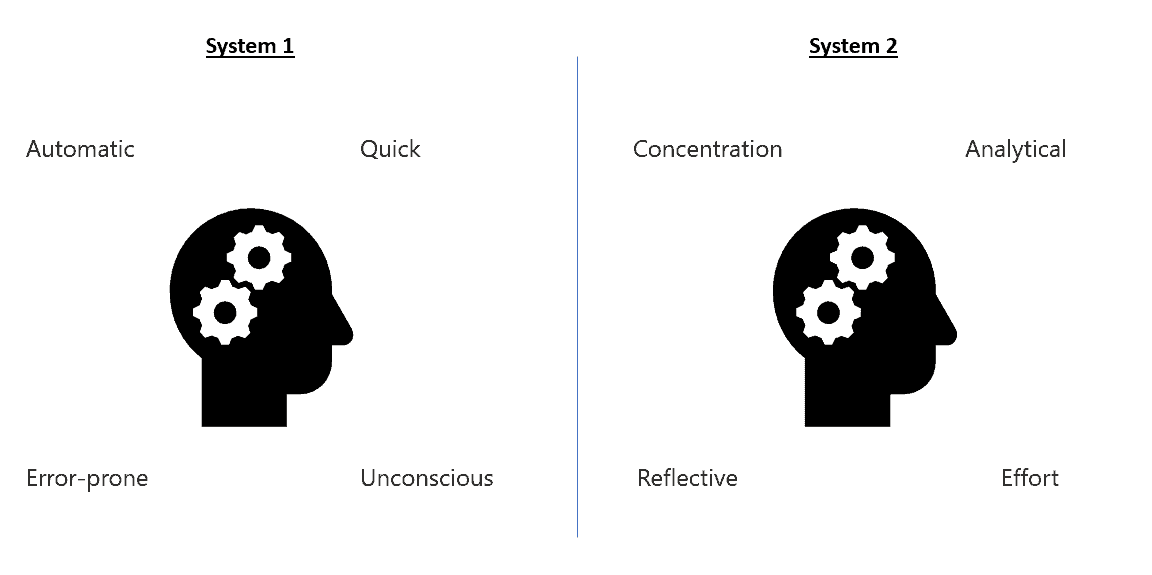
The idea is that our brains switch between these two systems. System 1 thinks fast, and System 2 thinks slow.
This is important to bear in mind for insider threats. Kahneman theorizes that our brains are “lazy”. We prefer to use System 1 decision-making because it’s easy and automatic. However, System 1 is also extremely error prone. At work, System 1 is what allows us to send emails to the wrong person or click on suspicious links without thinking. In fact, many cybercriminals rely on employees using System 1 thinking. They are betting on errors of judgement.
With 60% of data breaches caused by insider threats, reducing System 1 thinking is imperative to better security outcomes.
Applying behavioral science to your security policies:
Below are some essential tips for reducing System 1 thinking among the workforce:
Polymer DLP Behavioral Approach to Better Privacy
Polymer provides employee-based risk scoring based on patterns of sharing sensitive data. User nudges and warnings are designed to reinforce existing security training programs and best practices. For example:
- Synchronous In chats such as Slack, existing phishing simulations are incorporated to train employees in being proactive before clicking.
- Online file storage such as Google Drive, default sharing of public links is countered by framing users into private-only shares.
Polymer protects against data loss on modern collaboration tools like Slack, Dropbox, Zoom, Github and more with alerting & real-time redaction of sensitive and regulated information such as PII, PHI, financial and security data.
Further reading: