So, you’re in the market for a data protection solution that can protect your clients’ data in the cloud. It’s a good decision. 80% of enterprise workloads are now in the cloud, and reliance on cloud applications, like Slack, Teams and Office 365, continues to soar with the rise of hybrid work.
You realize that your customers are worried about cloud data leakage, and that they’re willing to spend more to achieve assurance that their data is safe.
In line with this, research shows that 69% of organizations plan to spend more on cybersecurity in 2022, while 29% say cybersecurity spending will be approximately the same as in 2021. Just 2% intend to pay less.
The thing is, the MSSP and MSP space is competitive. You need to offer your clients cost-effective solutions while also providing superior data protection to meet compliance obligations like HIPAA, GDPR and GBLA.
To make matters more complex, there are many solutions out there to choose from, each claiming to be the best of the bunch. How do you know which one is right for your business model?
To help you find the best data protection solution for protecting SaaS applications, we’ve compiled this handy guide.
So many solutions, so little time!
You could easily spend months looking at the different security solutions that promise to meet your data protection needs. From our experience, you’ll see a few products come up repeatedly. These are:
- Secure Access Service Edge (SASE)
- Extended Detection & Response (XDR)
- Cloud Access Security Broker (CASB)
- Data Loss Prevention (DLP)
Now, let’s take a look at each of these below – including the pros and cons.
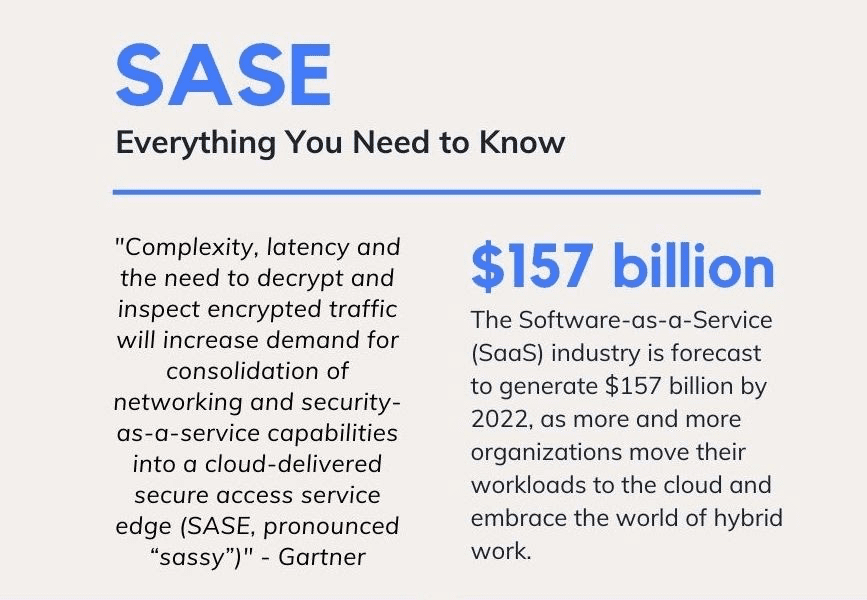
SASE
SASE is not a new security technology, but a convergence of WAN with already existing next-generation security solutions like Cloud Access Security Brokers, Firewalls as a Service, Secure Web Gateways and the Zero Trust Model. Gartner proposes that, when combined, these solutions form SASE: a streamlined, cloud-delivered security service that protects data at the edge, while delivering high-speed functionality that improves the end user experience.
SASE sounds excellent but it’s not a reality at the moment. This is because the edge of SASE relies on the set of cloud gateways ( known as POPs). A successful solution will need to utilize POPs at scale to provide full coverage and high-speed performance. For smaller enterprises, generating a system like this will cost a lot of money and will be extremely difficult for MSSPs to manage confidently.
Pros
- If deployed successfully, it will simplify and streamline cloud security
- Enhances security and the user experience at the same time
Cons
- SASE will have an important role in enterprise security in a few years’ time. However, right now, the functionality just isn’t there.
- The complexity of deployment and integration challenges means that most solutions currently fall short.
- SASE could create shadow IT problems while also costing a lot of money.
XDR
XDR is a holistic security solution for detection and response. It breaks down the silos between different security layers, such as endpoints, email, the cloud and the network, to provide comprehensive monitoring and detection capabilities across the entire attack surface.
Pros
- XDR is a step above today’s detection and response solutions. It scans everything at once and creates a complete picture of the enterprise environment – in theory.
Cons
- Like SASE, the functionality for successful XDR deployment doesn’t exist right now
- No vendor has put together the complete package yet. Current iterations inevitably leave security gaps
- Expensive to deploy
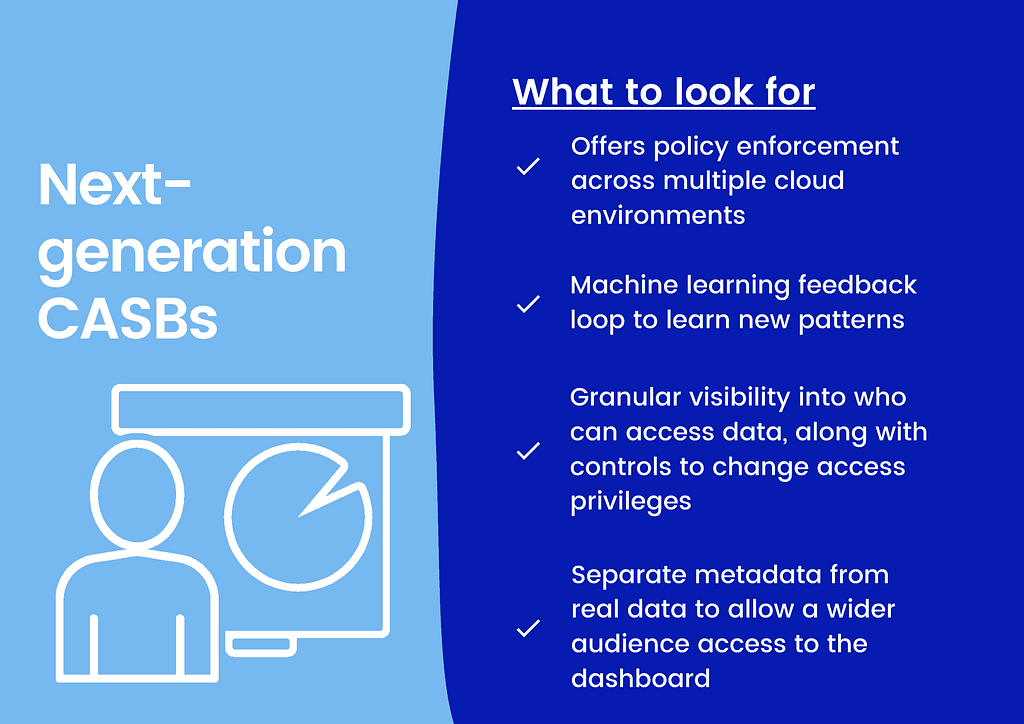
Traditional CASB
Traditional CASBs work by using proxies: either an agent is installed on end-user devices to monitor data, or an agent is placed in the cloud to monitor data in transit between cloud services and end-users.
However, with the proliferation of working from home, more users access company data through unmanaged devices, collaboration tools and unmanaged services, creating blind spots in the CASB framework. For example, traditional CASB solutions cannot monitor how sensitive data is being shared in collaboration tools like Slack.
Pros
- Bring data protection to the cloud
Cons
- Doesn’t cater to unmanaged devices and unmanaged applications
- Can impact the user experience
Legacy DLP
Even though DLPs are understandably popular, many miss the mark of preventing actual data loss. DLPs are typically designed to recognize patterns in structured, regulated data. Methods that recognize these patterns (REGEX) are poor approximations of how large amounts of sensitive data is shared.
When a DLP tool cannot separate irrelevant data and protect what matters most, the ripple effect is a lack of accurate and actionable insights. Further, security analysts cannot prioritize and respond to threats efficiently and intelligently. As a result, there’s a drain on IT and security productivity leading to “alert fatigue.”
Moreover, traditional DLP tools cannot decipher suspicious exchanges of info over communication platforms such as Slack, HipChat, SharePoint, or Gchat.
Pros
- Suitable for traditional network data protection – but not the cloud!
Cons
- Inefficient and expensive
- Stressful for your employees – or customer – to manage, depending on whether you offer DLP as a service
So, what’s an MSP to do?
When we described CASB and DLP, you’ll notice that we used the words traditional and legacy.
The thing is, the older versions of these solutions aren’t really fit for the complexity of today’s enterprise SaaS environments.
However, for every problem, there’s a solution. Companies like ours noticed the gap in the data protection market. We saw that enterprises needed a solution to extend data protection to collaboration tools like Slack, Google Workspace, Teams, Box and more.
That’s why we created cloud-based Data Loss Prevention (DLP) built on a zero-trust model.
What is cloud data loss prevention?
Also known as SaaS DLP, our solution uses APIs to secure cloud apps accessed by unmanaged devices and endpoints, offering comprehensive and borderless protection, reaching beyond the firewall to secure, check, and analyze any incoming traffic to your cloud applications.
As more organizations rely on applications like Slack, Teams and Google Workspace, working with a cloud-based DLP vendor is one of the smartest moves MSPs and MSSPs can take to secure enterprise data in the cloud.
Our solution helps you to secure data as it travels in and out of collaboration tools and cloud applications. Benefits include…
- Visibility: Achieve granular visibility into cloud application usage, including which employees are using cloud services, how they are accessing them and what information they are trying to upload, download and store in the cloud.
- Compliance: You need to know where client data is to secure it. With Polymer, you can see precisely where information is, where it’s been and where employees are trying to move it too. Not just that, though, you can actually control the flow of data. Using pre-defined policies, you can ensure that no data in the cloud is moved, edited or deleted without the IT team’s approval.
- Data Security: Enforce policies like encryption, redaction and authentication to ensure that data is only accessed legitimately. The best in breed of these solutions also embed employee training into the daily workflow, nudging users to make security-conscious choices and protect data as they work.
- Threat protection: With access and authentication controls in place, our framework helps you manage cyber risks and subvert malicious actors trying to get their hands on client data.










