The technology industry is still technically in its infancy. Every year, it seems that innovation hurls forwards in leaps and bounds. At the same time, the cyber security risks that organizations face are constantly evolving too.
Because everything is, well, so new, there’s a lack of standards and rules out there for mitigating cyber risk – with one exception: the NIST CyberSecurity Framework.
Back in 2013, President Obama recognized the need for a standardized cyber security framework to help both the government and organizations mitigate cyber threats. This led to the creation of the NIST CyberSecurity Framework. Then, in 2017, President Trump announced the cybersecurity executive order, which formalized the Framework into federal government policy.
That’s not to say that the Framework is aimed at governments only, though. It’s meant for businesses of all shapes and sizes – and in all sectors.
Want to learn more about the Framework? Let’s dive into the details below.
Who’s NIST?
First things first, let’s cover off the Framework’s creator: NIST (AKA: the National Institute of Standards and Technology). NIST was founded in 1901. It is a non-regulatory US government agency focused on driving innovation through technology.
NIST’s remit is expansive, focusing on various technologies from sustainability devices to healthcare equipment to telecommunication networks. One of its responsibilities is also cybersecurity. NIST supports federal agencies in meeting the requirements of FISMA, which focuses on securing government data.
And then there’s the Cybersecurity Framework. NIST created this along with industry stakeholders to help businesses worldwide mitigate and manage cybersecurity risks. The Framework has been an enormous success so far. It’s estimated that 30% of US organizations use it, including JP Morgan, Microsoft, and Intel.
Is the framework mandatory?
Unlike regulations such as GDPR, HIPAA and PCI DSS, the NIST framework is not mandatory. This means that you don’t have to follow it – and there are no penalties for choosing not to adopt it.
Rather than law, this Framework is a piece of voluntary guidance designed to help companies improve their cybersecurity resilience. At its simplest, it allows organizations to protect and secure sensitive data – such as PII, PHI and proprietary information. Following the Framework can improve your compliance with data protection laws and reduce your chance of a cyber breach, so it’s well worth considering.
Another good thing about the Framework is that it was designed with accessibility in mind. You don’t need to be an MIT graduate to understand the information in the guidance, meaning it’s suitable for organizations of all sizes – even start-ups that lack a dedicated IT team.
I’m listening…so what’s the framework all about?
The Framework has a few key goals. Mainly it aims to:
- Standardize and integrate disparate cyber security best practices into a single point of truth, so organizations can more easily manage cybersecurity risks.
- Demystify cyber security requirements and regulations by creating a common language that all employees can understand
- Provide helpful guidance on how to secure sensitive data and combat cybersecurity risks
- Help organizations to respond and recover from cybersecurity incidents while focusing on a cycle of continuous security improvement
- Reach organizations of all sizes by offering a flexible approach that can be tailored to each company’s unique needs and challenges.
If you’re struggling with an end-to-end approach to security, then this Framework could be precisely what you need. Of course, the Framework isn’t a cyber security solution in itself (that’s where we come in!) But, it does guide you in creating a holistic cyber security strategy, enabling you to find the right security solutions for your business.
The NIST Framework comprises three pillars: the Framework Core, Profiles, and Implementation Tiers.
The NIST framework core
The framework core covers the five essential aspects of cybersecurity. Note, the Framework Core is not a checklist that you are meant to tick off as a one-off. It’s more of a strategic approach to cybersecurity that your organization can use for decision-making.
Think of the core as a lifecycle, which you use for assessing, managing and mitigating cyber risks over time. The five functions are:

- Identify: Assess current data usage and then evaluate potential risks;
- Protect: Deploy solutions that help protect the business and its data;
- Detect: Discover threats in real-time;
- Respond: Respond to issues as they arise;
- Recover: Put steps in place to ensure the effective recovery of lost data.
Now, while this might look very top-level, there’s a lot more to the five functions. Each function contains categories designed to help organizations identify relevant challenges. For example, the protection function could include data protection, anti-virus and regular patching.
Then, within each category, there are sub-categories. These contain specific objectives that help organizations to put their goals into action. The protect function could ensure updates are configured every two weeks or utilizing data classification.
The implementation tiers
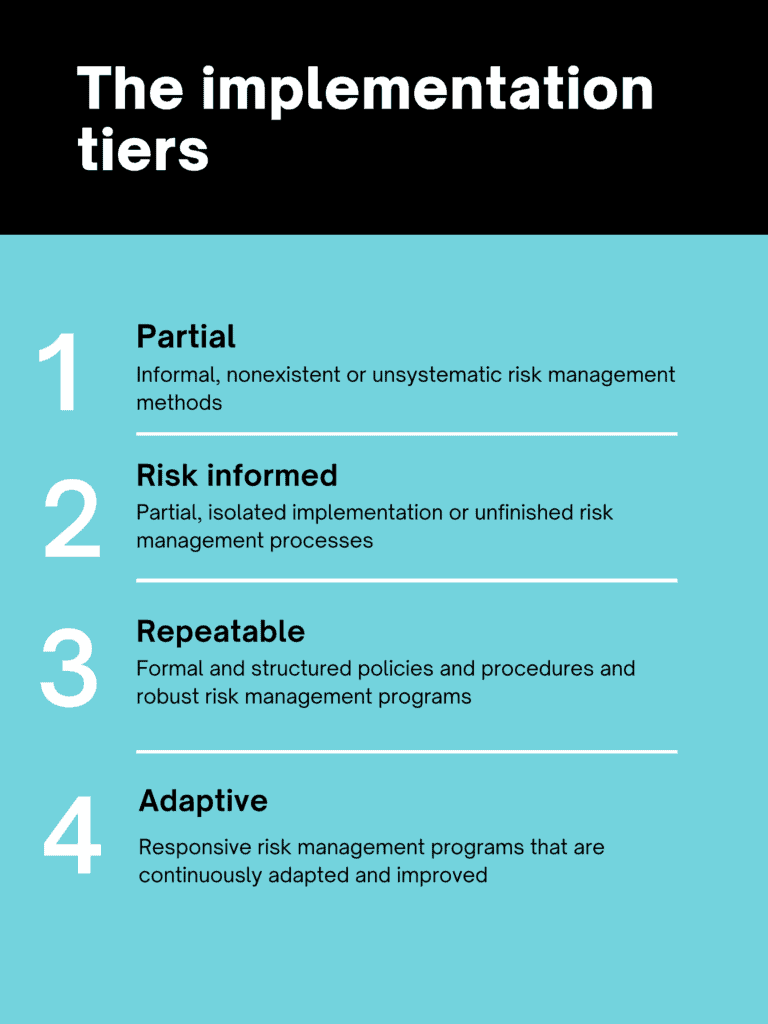
So, that’s the framework core. Now, let’s talk about the implementation tiers. There’s four of these, and each one describes a different level of risk management maturity. The tiers are a benchmark that will help you understand how mature your approach to reducing cyber risks are.
- Tier 1: Partial — Informal, nonexistent or unsystematic risk management methods
- Tier 2: Risk Informed — Partial, isolated implementation or unfinished risk management processes
- Tier 3: Repeatable — Formal and structured policies and procedures and robust risk management programs
- Tier 4: Adaptive — Responsive risk management programs that are continuously adapted and improved
Depending on your industry, budget and risk tolerance, you choose the tier that fits your company best. For example, a healthcare organization will likely put itself in tier 4 for most processes due to strict compliance regulations. However, organizations in other sectors may only need to stick to tier 2.
Moreover, the Tier system isn’t meant to be a blanket approach. You might want to benchmark some areas of your business against tier 4 but other areas against tier 1. It all depends on your organization’s security needs.
Profiles
The last pillar is Profiles. A profile is an assessment of your company’s cybersecurity resilience at a moment in time. Essentially, a profile is a snapshot. As you embark on your NIST journey, you’ll collect and create numerous profiles. You start with your profile before implementing the Framework, and then you create the profile of where you want to be as a target. Creating these profiles helps you populate a roadmap for reducing cyber risk and measuring your progress.
Remember, none of the pillars are meant to be rigid. They are a guideline that can be tailored to your unique needs.
I want to learn more!
Good! As well as our handy guide, NIST also has several resources available about the Framework, including frequently asked questions, industry materials, case studies, and other guidance.
Should I implement the NIST Cybersecurity Framework?
Ultimately, the NIST Cybersecurity Framework is a solid way to boost your cybersecurity resilience. It is worth bearing in mind that it is an investment, meaning it comes with a price tag. However, when we look at the cost of a data breach ( $4.24 million in 2021) the price of prevention seems small in comparison.
Depending on your organization’s risk tolerance, you may wish to borrow elements of the Framework, without adopting it completely. Our advice is to make sure you focus on discovering and securing sensitive data wherever it travels, which we can assist with.



